-
Joachim
- OpenVpn Newbie
- Posts: 8
- Joined: Wed Feb 10, 2021 11:37 pm
.ovpn file cannot be imported in Android, but works perfectly in Windows
I have a .ovpn config file that works perfectly in the Windows OpenVPN GUI, but when I want to import the same file in Android it gives the following message: «Failed to parse profile: option_error: remote option not specified».
This is very strange because it is no problem in Windows and the remote option is specified (see below). Is this a bug in the Android app (OpenVPN Connect)? I obtained the .ovpn file from a Synology NAS configuration.
My .ovpn file looks like this:
Client config
dev tun
tls-client
remote my.ddns.com 1194
# The «float» tells OpenVPN to accept authenticated packets from any address,
# not only the address which was specified in the —remote option.
# This is useful when you are connecting to a peer which holds a dynamic address
# such as a dial-in user or DHCP client.
# (Please refer to the manual of OpenVPN for more information.)
#float
# If redirect-gateway is enabled, the client will redirect it’s
# default network gateway through the VPN.
# It means the VPN connection will firstly connect to the VPN Server
# and then to the internet.
# (Please refer to the manual of OpenVPN for more information.)
#redirect-gateway def1
# dhcp-option DNS: To set primary domain name server address.
# Repeat this option to set secondary DNS server addresses.
#dhcp-option DNS DNS_IP_ADDRESS
pull
# If you want to connect by Server’s IPv6 address, you should use
# «proto udp6» in UDP mode or «proto tcp6-client» in TCP mode
proto udp
script-security 2
reneg-sec 0
cipher AES-256-CBC
auth SHA512
auth-user-pass
auth-nocache
<ca>
——BEGIN CERTIFICATE——
ABCDEFGHIJ
——END CERTIFICATE——
——BEGIN CERTIFICATE——
KLMNOPQRST
——END CERTIFICATE——
</ca>
Last edited by Joachim on Thu Feb 11, 2021 7:34 pm, edited 2 times in total.
-
TinCanTech
- OpenVPN Protagonist
- Posts: 11142
- Joined: Fri Jun 03, 2016 1:17 pm
Re: .ovpn file cannot be imported in Android, but works perfectly in Windows
Post
by TinCanTech » Thu Feb 11, 2021 12:46 am
Joachim wrote: ↑
Thu Feb 11, 2021 12:05 am
I obtained the .ovpn file from a Synology NAS configuration
Yikes .. is that a very old Synology NAS ?
-
Joachim
- OpenVpn Newbie
- Posts: 8
- Joined: Wed Feb 10, 2021 11:37 pm
Re: .ovpn file cannot be imported in Android, but works perfectly in Windows
Post
by Joachim » Thu Feb 11, 2021 1:25 am
No, it is a recent one (DS218). But I don’t think that this can have something to do with the error because the error comes immediately when I try to open the config file on Android (the app is clearly not taking the time to search for a server). So I would assume that there is some missing information in the file that is very important. But my VPN connection works perfect on Windows, which is really strange.
I forgot to mention that I used on Windows the software ‘OpenVPN 2.5.0’ from https://openvpn.net/community-downloads/. Is there a difference with the installer ‘OpenVPN Connect 3.2.2’ for Windows from https://openvpn.net/download-open-vpn/ ? The latter has the same name as the app for Android.
-
TinCanTech
- OpenVPN Protagonist
- Posts: 11142
- Joined: Fri Jun 03, 2016 1:17 pm
Re: .ovpn file cannot be imported in Android, but works perfectly in Windows
Post
by TinCanTech » Thu Feb 11, 2021 2:15 am
OpenVPN Connect is Closed source .. not on my radar. Try Arne Schwabe’s version.
-
Joachim
- OpenVpn Newbie
- Posts: 8
- Joined: Wed Feb 10, 2021 11:37 pm
Re: .ovpn file cannot be imported in Android, but works perfectly in Windows
Post
by Joachim » Thu Feb 11, 2021 7:06 pm
When I try to use Arne Schwabe’s version, I can choose to import the .ovpn file, but I thought that this file also contains the certificate. However, the app asks to import the certificate separately. Why is this, when it could just be read from the .ovpn? In OpenVPN 2.5.0 on Windows I just needed a .ovpn file.
Which ‘type’ should I choose in the app? Because I have indeed the certificate (same as in the .ovpn file) in a separate file with a .crt extension, but in most ‘type’ options in the app I need to choose multiple files. There is also an option ‘username/password’, but is that not always needed to connect to a VPN? For me this is the case on my computer. In the Windows version ‘OpenVPN Connect’ it is also needed to import the certificate as a separate file for some strange reason, but there also just one file is sufficient and the VPN works fine.
I am also unfamiliar with the terminology: CA certificate, cert certificate, client certificate, server certificate, root certificate, intermediate certificate. Which one is is the certificate from the .ovpn file? Is CA synonym for client certificate?
Just for my information: is there really no support platform for questions about OpenVPN Connect? This is quite confusing because the name of this subforum is ‘OpenVPN Connect (Android)’
-
Joachim
- OpenVpn Newbie
- Posts: 8
- Joined: Wed Feb 10, 2021 11:37 pm
Re: .ovpn file cannot be imported in Android, but works perfectly in Windows
Post
by Joachim » Thu Feb 11, 2021 9:10 pm
But as you can see from my code in the first message. The CA certificate is already inline. So I don’t understand the problem.
-
Joachim
- OpenVpn Newbie
- Posts: 8
- Joined: Wed Feb 10, 2021 11:37 pm
Re: .ovpn file cannot be imported in Android, but works perfectly in Windows
Post
by Joachim » Fri Feb 12, 2021 9:43 am
Thank you, that seems to be an interesting article about certificates.
Sorry, if my explanation was confusing. I will summerise it again.
In my first post I gave the .ovpn config file that has an inserted CA certificate. This worked perfectly on Windows OpenVPN 2.5.0 (open source software) to establish a complete functional VPN connection. So a really simple configuration.
Then, I tried to use the same .ovpn file to configure the Android OpenVPN Connect (closed source as you said), but then I got the error «Failed to parse profile: option_error: remote option not specified» (see also first message).
Then, you said you could not help me with the closed source Android version, so as you suggested I am now trying to use the open source Android version from Arne Schwabe.
But my question now is: which settings in that app should I choose so that it is sufficient to just import the .ovpn config file as given in my first post? Is there an easy configuration method as easy as for Windows OpenVPN 2.5.0? So with other words, is there a setting in Arne Schwabe’s app that prevents the recognition of the inline CA certificate from my .ovpn file?
Last edited by Joachim on Fri Feb 12, 2021 3:21 pm, edited 1 time in total.
-
Joachim
- OpenVpn Newbie
- Posts: 8
- Joined: Wed Feb 10, 2021 11:37 pm
Re: .ovpn file cannot be imported in Android, but works perfectly in Windows
Post
by Joachim » Fri Feb 12, 2021 2:56 pm
Wow, I finally found the SOLUTION!!! The same .ovpn config file works now for both Windows and Android!
I now totally understand why you couldn’t help me
Both OpenVPN Connect for Android and OpenVPN from Arne Schwabe apparently didn’t find any data in my .ovpn file. When I open my file in Windows with Notepad, I can perfectly see normal text in the .ovpn file. However, when I send the file to my phone via e-mail to my own e-mail address and I open the .ovpn file with a simple text editor, the file is blank! Of course the apps cannot detect any configurations from an unreadable file and give errors like ‘there is no remote chosen’ or ‘no CA certificate is present’.
I also did a separate test: I created a random .txt file on Windows with Notepad, then I sent it to my own e-mail and tried to open it with a texteditor. Now the file appeared not empty, but only some unreadable strange symbols were visible.
SOLUTION:
The problem is a very very very specific bug! When you send a simple text file like .txt or .ovpn with a mail address that is configured with IMAP in Microsoft Outlook 2019 to another (or your own) e-mail address that can be IMAP configured on the Gmail app on your Android phone, then the .txt attachment becomes corrupted upon opening. It becomes also unreadable in Windows when I would bring the file back to my Windows PC by transferring it via USB to my PC. So the file is permanantly corrupted.
When you would open the same received mail with another IMAP configured Android mail app, the file is not corrupted.
When the email sender uses the webmail interface of the email-provider instead of IMAP in Outlook, then there is also no problem when the receiver opens the attachment in the IMAP configured Android Gmail app.
When you use non-IMAP configured e-mail addresses as sender OR as receiver, there is also no problem.
In fact this bug should be send to both Google and Microsoft. Do you have connections?
I would never have encountered the problem if I would have just used a USB connection to transfer the file to my phone.
I am so happy my Open VPN finally works on Android! All this waste of time just because of a stupid mail bug that has nothing to do with OpenVPN
Last edited by Joachim on Fri Feb 12, 2021 5:20 pm, edited 2 times in total.
-
TinCanTech
- OpenVPN Protagonist
- Posts: 11142
- Joined: Fri Jun 03, 2016 1:17 pm
Re: .ovpn file cannot be imported in Android, but works perfectly in Windows
Post
by TinCanTech » Fri Feb 12, 2021 5:16 pm
Joachim wrote: ↑
Fri Feb 12, 2021 2:56 pm
when I send the file to my phone and I open the .ovpn file with a simple texteditor, it is blank!
I guess the way you send it to the phone is broken ..
-
Joachim
- OpenVpn Newbie
- Posts: 8
- Joined: Wed Feb 10, 2021 11:37 pm
Re: .ovpn file cannot be imported in Android, but works perfectly in Windows
Post
by Joachim » Fri Feb 12, 2021 5:27 pm
I was just editing my previous message with the solution, while you answered it So you can read the solution there. It was indeed the way I sent it to my phone that caused the file to be corrupted.
-
DanDewey
- OpenVpn Newbie
- Posts: 2
- Joined: Wed Aug 31, 2022 8:56 pm
Re: .ovpn file cannot be imported in Android, but works perfectly in Windows
Post
by DanDewey » Wed Aug 31, 2022 8:58 pm
Can I just say thanks for this advice I too was having the same issue where PC worked but android didn’t.
I also emailed the file, but following the advice here I saved into google drive then open on phone and it worked straight away no issues.
-
Pawel_71
- OpenVpn Newbie
- Posts: 1
- Joined: Wed Jan 11, 2023 3:54 pm
Re: .ovpn file cannot be imported in Android, but works perfectly in Windows
Post
by Pawel_71 » Wed Jan 11, 2023 4:01 pm
Hi mate.
I had the same problem. The solution was to install an older version of the software. The new version does not ask for permissions. I installed the old version, from 2021 — ver. 3.2.4., which asks for file permissions during installation. After its launch, the import of the profile took place without any problems. I downloaded the app from APK Mirror. After importing the profile, I updated the app. The profile works.
Simple solutions are the best
.
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and
privacy statement. We’ll occasionally send you account related emails.
Already on GitHub?
Sign in
to your account
Closed
Kevintjeb opened this issue
Jun 25, 2017
· 18 comments
Comments
ERROR
Error parsing OpenVPN profile: option_error: remote option not specified.
Installing PiVPN went smoothly, everything is working. Creating a profile also worked fine, but when I try to import it on my phone I get the error:
Error parsing OpenVPN profile: option_error: remote option not specified.
Now it seems that I am missing the remote option. But I double checked it and it is there. The IP is my public IP and the port is forwarded in my router.
Can you post the output of pivpn debug? Can you post the .ovpn file? Please censor the keys.
Maybe it is because of the android app. I just connected using my laptop with OpenVPN GUI and it worked fine. Do you still need the pivpn debug and .ovpn file?
I had this same problem when trying to connect with the «OpenVPN Connect» app on Android.
.ovpn file:
<ca>
-----BEGIN CERTIFICATE-----
REMOVED
-----END CERTIFICATE-----
</ca>
<cert>
-----BEGIN CERTIFICATE-----
REMOVED
-----END CERTIFICATE-----
</cert>
<key>
-----BEGIN ENCRYPTED PRIVATE KEY-----
REMOVED
-----END ENCRYPTED PRIVATE KEY-----
</key>
<tls-auth>
#
# 2048 bit OpenVPN static key
#
-----BEGIN OpenVPN Static key V1-----
REMOVED
-----END OpenVPN Static key V1-----
</tls-auth>
pivpn debug:
::: :::
:: PiVPN Debug ::
::: :::
:: Latest Commit ::
::: :::
commit 6ce39bfec399d9a8203409a108ef27f2ee29327a
Author: 0-kaladin <0.kaladin@gmail.com>
Date: Mon Feb 27 21:01:23 2017 -0500
Update README for IRC channel
Due to discontinuation of Google Spaces
::: :::
:: Recursive list of files in ::
:: /etc/openvpn/easy-rsa/pki ::
::: :::
/etc/openvpn/easy-rsa/pki/:
ca.crt
crl.pem
dh2048.pem
index.txt
index.txt.attr
index.txt.attr.old
index.txt.old
issued
Laptop.ovpn
Phone.ovpn
private
serial
serial.old
ta.key
Test.ovpn
/etc/openvpn/easy-rsa/pki/issued:
Laptop.crt
Phone.crt
server.crt
/etc/openvpn/easy-rsa/pki/private:
ca.key
Laptop.key
Phone.key
server.key
::: :::
:: Output of /etc/pivpn/* ::
::: :::
:: START /etc/pivpn/INSTALL_PORT ::
REMOVED
:: END /etc/pivpn/INSTALL_PORT ::
:: START /etc/pivpn/INSTALL_PROTO ::
udp
:: END /etc/pivpn/INSTALL_PROTO ::
:: START /etc/pivpn/INSTALL_USER ::
REMOVED:: END /etc/pivpn/INSTALL_USER ::
:: START /etc/pivpn/NO_UFW ::
0
:: END /etc/pivpn/NO_UFW ::
:: START /etc/pivpn/pivpnINTERFACE ::
eth0
:: END /etc/pivpn/pivpnINTERFACE ::
::: :::
:: /etc/openvpn/easy-rsa/pki/Default.txt ::
::: :::
::: :::
:: Debug Output Complete ::
::: :::
I also cannot connect from my Windows 7 laptop. It fails and says to check the log file. The log file says:
Mon Jun 26 15:31:49 2017 disabling NCP mode (--ncp-disable) because not in P2MP client or server mode
Options error: You must define TUN/TAP device (--dev)
Use --help for more information.
Thank you for any assistance you can provide!!
@redfast00 Any idea? I had this the first time I installed PiVPN aswell. But it got fixed when I installed it a second time. Now, the third time, it is back.
OpenVPN GUI on PC works fine with the same profile.
OpenVPN Connect does not work because of the remote option.
Can you post your .ovpn file?
Have you tried using OpenVPN for Android by Arne Schwabe? The ovpn looks okay.
@redfast00 I tried using the app OpenVPN for android but it does not work either. It adds the .ovpn file but when I click on the profile to start the connection it says I need to select a user certificate. But you saw it was all inside the .ovpn file.
Are there other clients I can try to use? I created new client profiles, all with the same error.
Did you ever find a resolution for this? I’m having the same issue on the iPhone app.
@InfoSecured I have not found a resolution. I did create a new .openvpn last week on the same install, that one worked like a charm. The thing I did differently is not having special characters in my .openvpn file password..
I had this issue with the Android app. I’d emailed the ovpn to myself to get it on to my phone. I tried again using the usb cable to get the opvn file on to my phone and it worked.
Strange thing is, I could import the ovpn file I’d emailed to myself on my mac and connect, so it could be something the gmail client on the phone does when it handles the file.
Nice jamie, same conclusion 

I had this issue with the Android app. I’d emailed the ovpn to myself to get it on to my phone. I tried again using the usb cable to get the opvn file on to my phone and it worked.
Strange thing is, I could import the ovpn file I’d emailed to myself on my mac and connect, so it could be something the gmail client on the phone does when it handles the file.
In 2020, still getting this on Windows and iPhone client
I Have The same error on iPhone
I resolved this by saving the .ovpn profile with CRLF instead of LF.
This looks like a parsing issue in the OpenVPN mobile client.
This error is not caused by problem with configuration file, but in way how you transfer ovpn file into your device. For e.g sending file by email from cmd causes interpretaion of this file and causes mess. The best way to verify is to to open file on device in any text editor. If it is not readable, openvpn will be not able to read it as well and will report an error during a import.
Solution is simple.
Just copy vpn configuration file through USB cable and try to open.Its working.
I tried to send config file through Email & Whats-up & It did not work. finally I plugged my android tab to pc and copied the vpn file to tablet internal memory.It worked.
Вчера обнаружил, что на мой домашний сервер пытаются подобрать пароль к RDP. Спросил наших безопасников с работы, да, порт сканировали, но пароль подбирают не они… Надо что-то делать с этим, и я даже знаю что.
Ударим шифрованием по злобным брутфорсерам! Ставим OpenVPN 2.5.1 сервер на Windows Server 2016.
- Встретимся с Easy-RSA 3.
- Решим неочевидный баг с директорией временных файлов.
- Освоим OpenVPN Connect, в том числе на Android.
- Запилим адаптер OpenVPN WinTun.
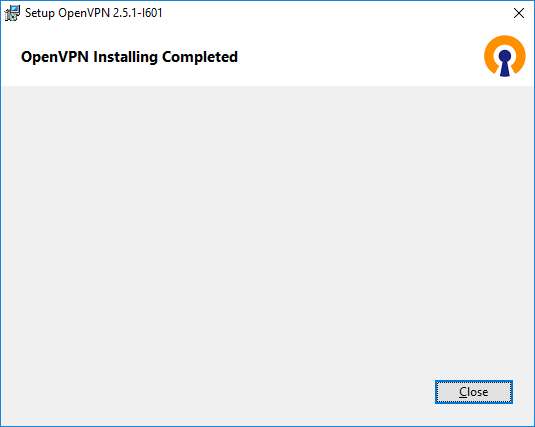
Установка OpenVPN Server
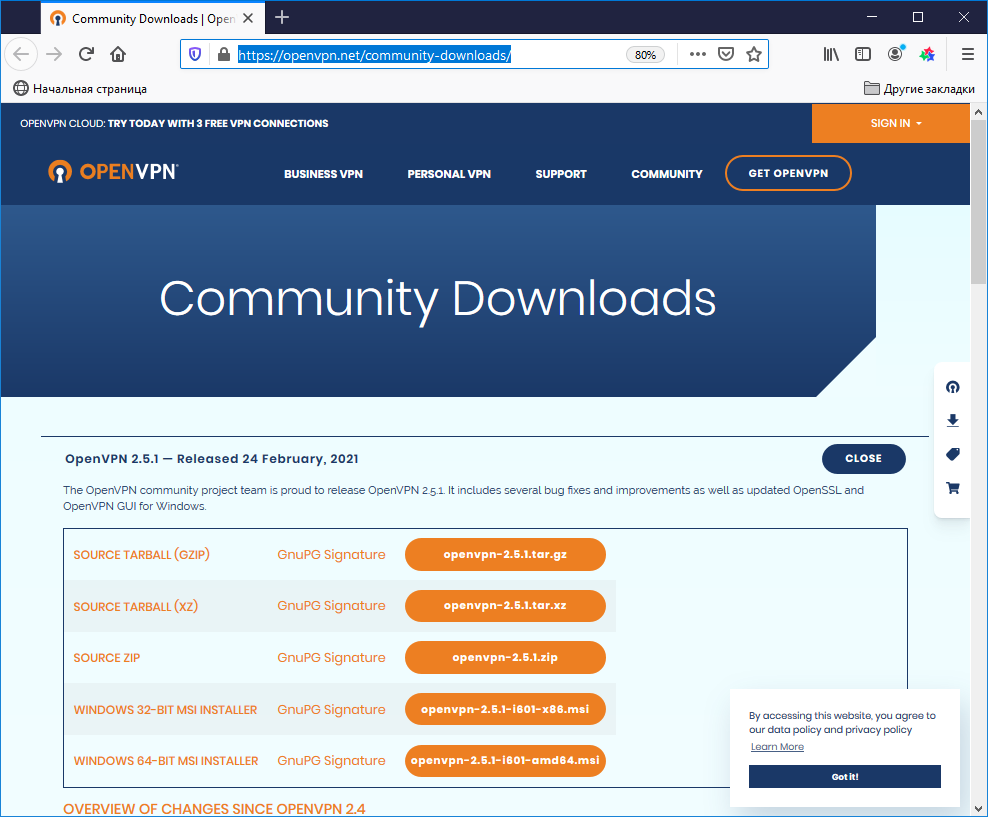
Скачиваем дистрибутив для установки OpenVPN:
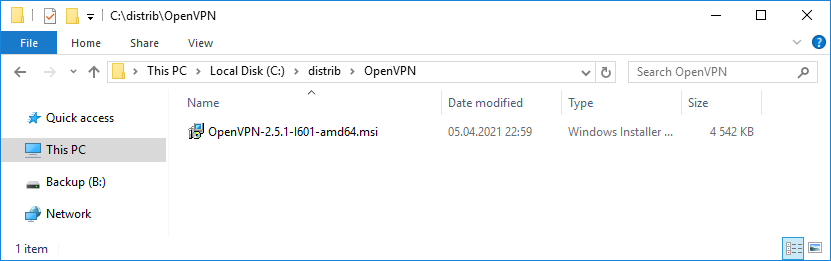
Доступна версия OpenVPN 2.5.1. Скачиваю Windows 64-bit MSI installer, файл OpenVPN-2.5.1-I601-amd64.msi.
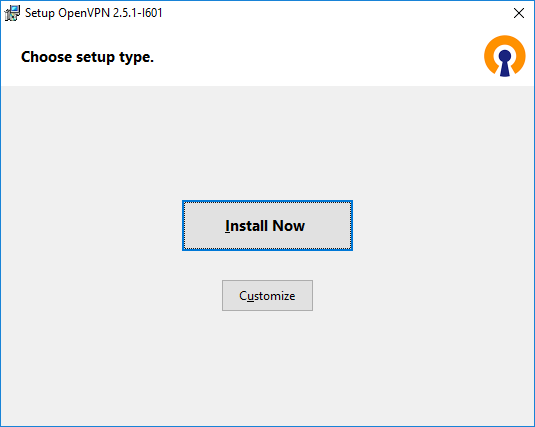
Запускаем инсталлятор OpenVPN.
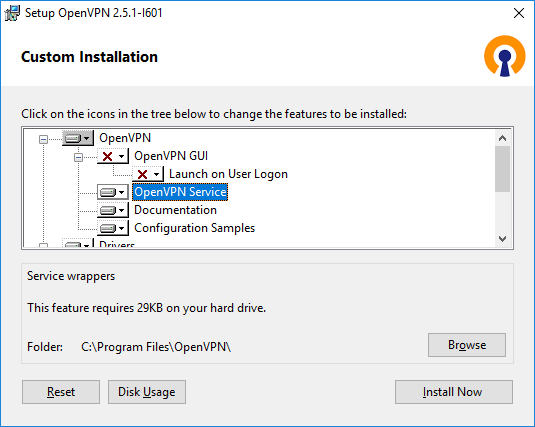
Открывается мастер установки, предлагают выбрать тип установки, естественно, нажимаем Customize. Установка по умолчанию нас не устроит.
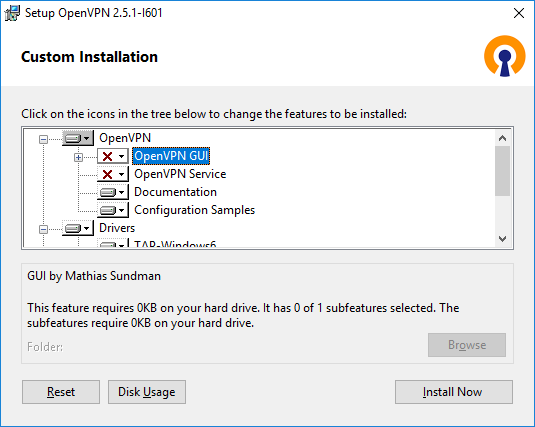
OpenVPN GUI отключаю. Мне нужно, чтобы OpenVPN на сервере работал автоматически.
А OpenVPN Service, наоборот, включаю. OpenVPN у меня будет работать как служба Windows.
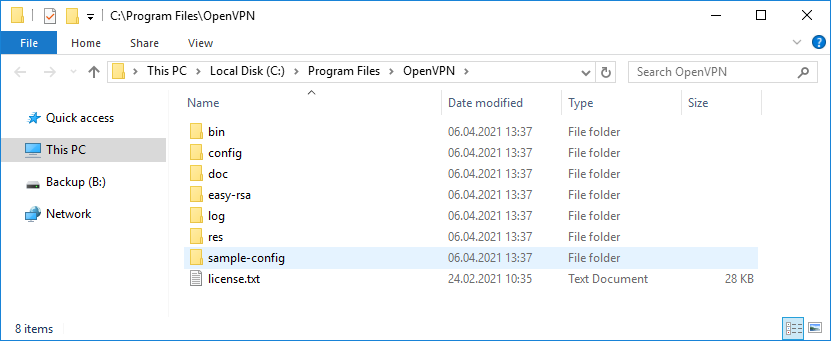
Документацию и примеры конфигурации оставляю. Конфигурационные примеры будут использоваться в качестве шаблонов.
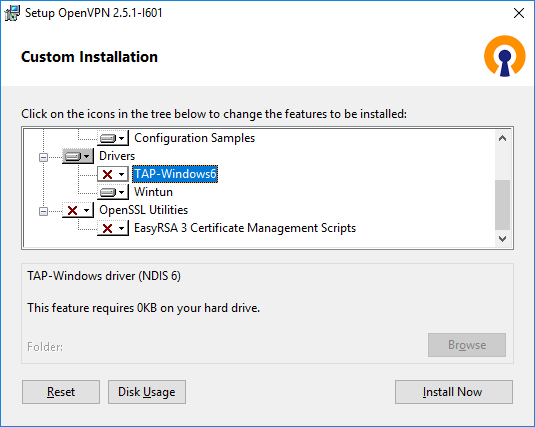
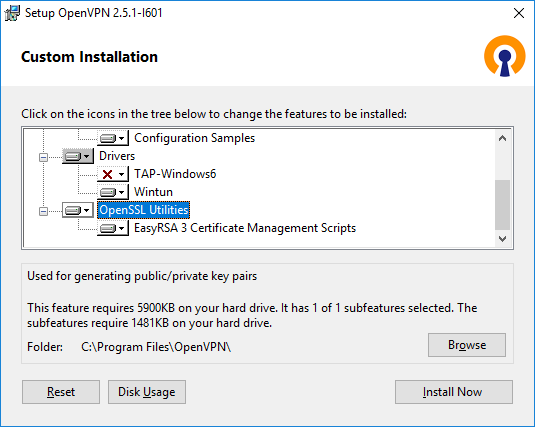
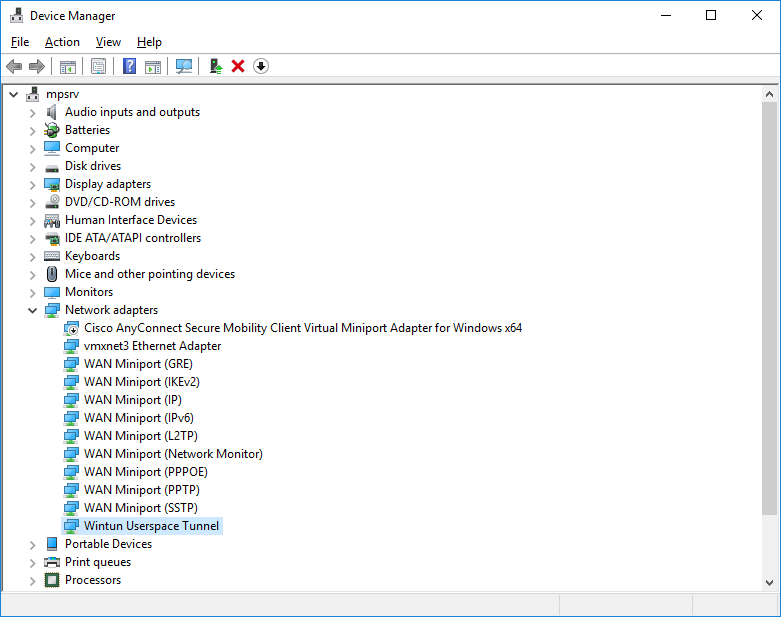
Начиная с версии OpenVPN 2.5 появилась поддержка драйвера WinTUN от разработчиков WireGuard. Говорят, что работает быстрее чем TAP-Windows6. Поэтому драйвер TAP-Windows6 отключаю и включаю Wintun.
ПРИМЕЧАНИЕ: для включения драйвера Wintun необходимо в файле конфигурации сервера включить параметр:
windows-driver wintun
Утилиты OpenSSL EasyRSA 3 Certificate Management Scripts включаю. Install Now.
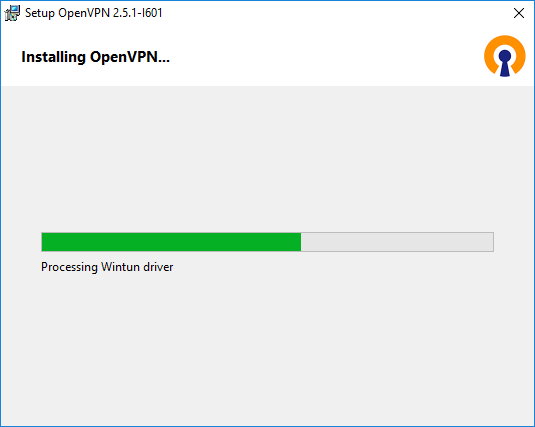
Начинается процесс установки OpenVPN.
Установка успешно завершена. Close.
Установка выполнена в директорию C:Program FilesOpenVPN.
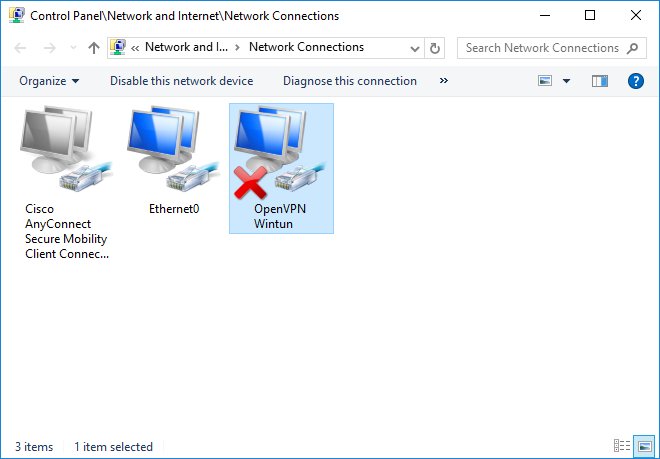
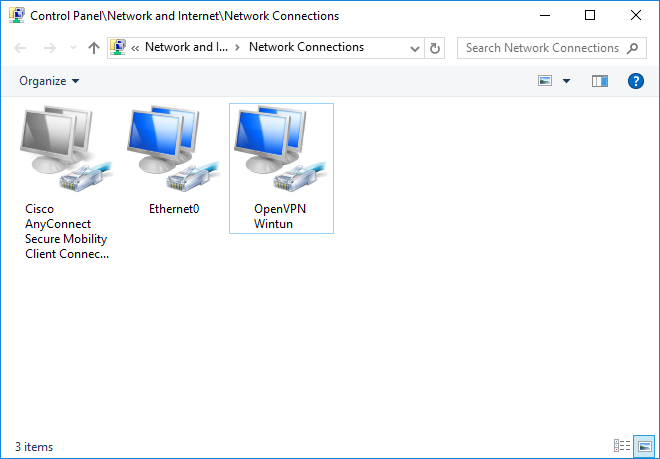
После установки у нас появляется новый сетевой адаптер Wintun Userspace Tunnel.
Адаптер отключён.
Создание ключей и сертификатов
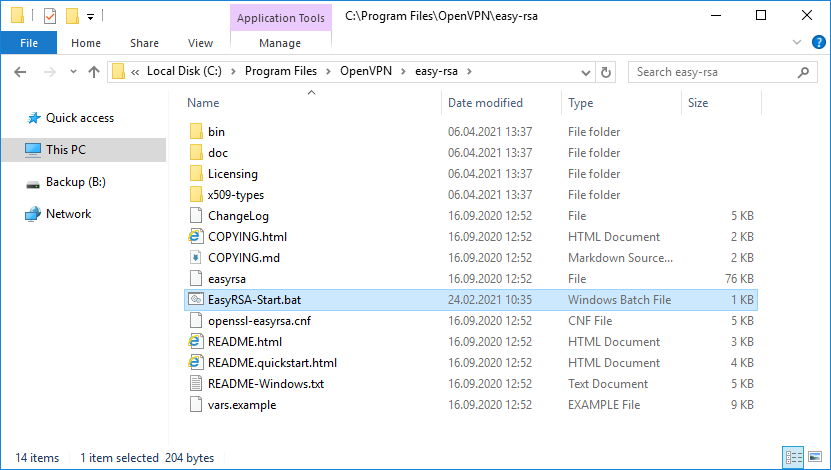
Запускаем командную строку под администратором и переходим в рабочую директорию C:Program FilesOpenVPNeasy-rsa.
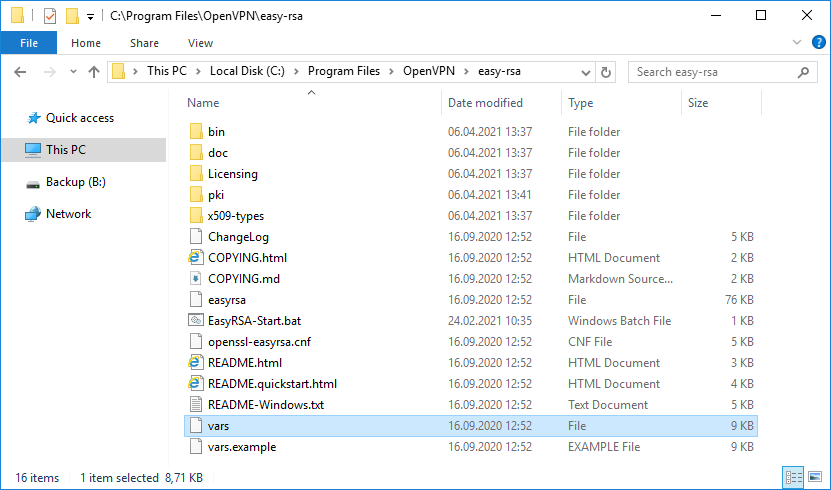
cd C:Program FilesOpenVPNeasy-rsaВ этой папке есть всё необходимое для генерации сертификатов.
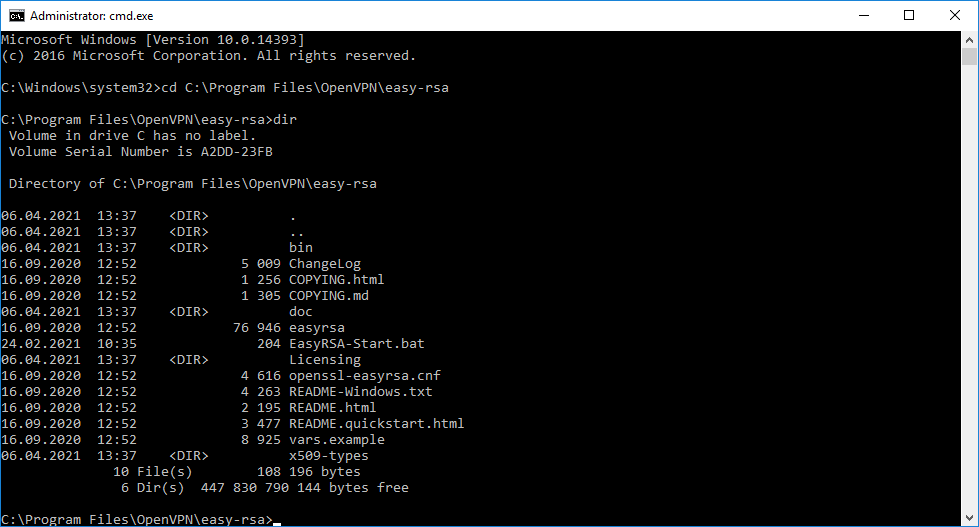
Для работы в Windows нас интересует файл EasyRSA-Start.bat.
Выполняем EasyRSA-Start.bat.
Запускается оболочка EasyRSA Shell.
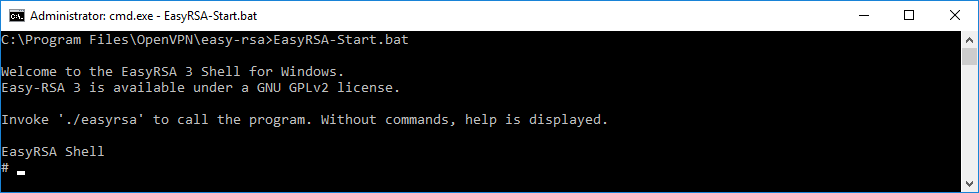
Инициализируем новую конфигурацию:
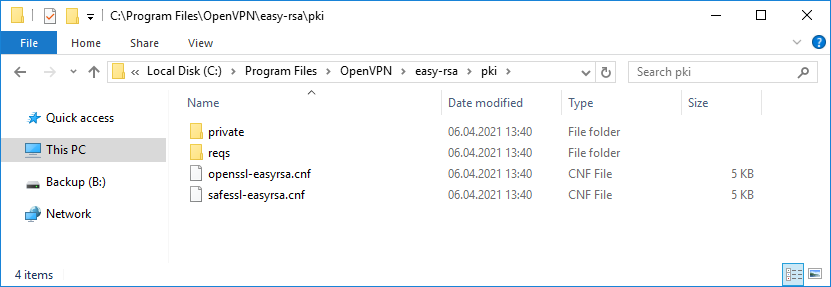
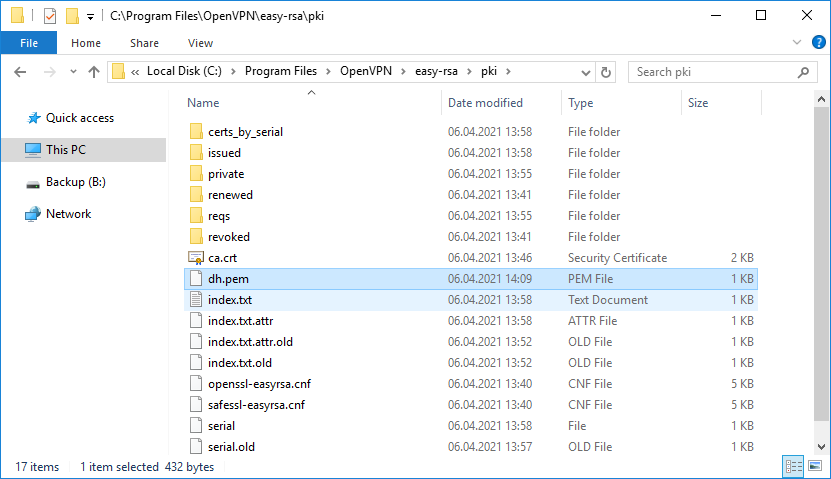
./easyrsa init-pkiПоявляется новая директория C:Program FilesOpenVPNeasy-rsapki.
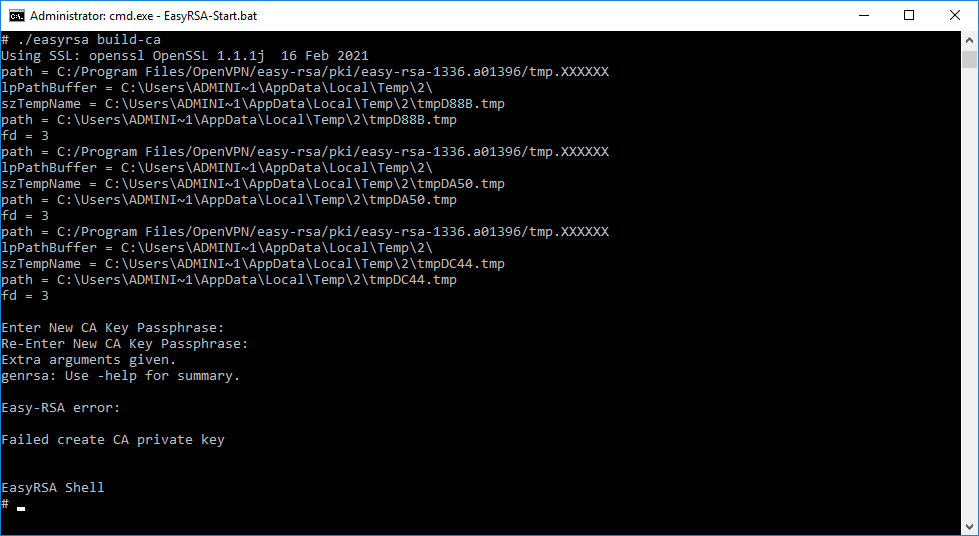
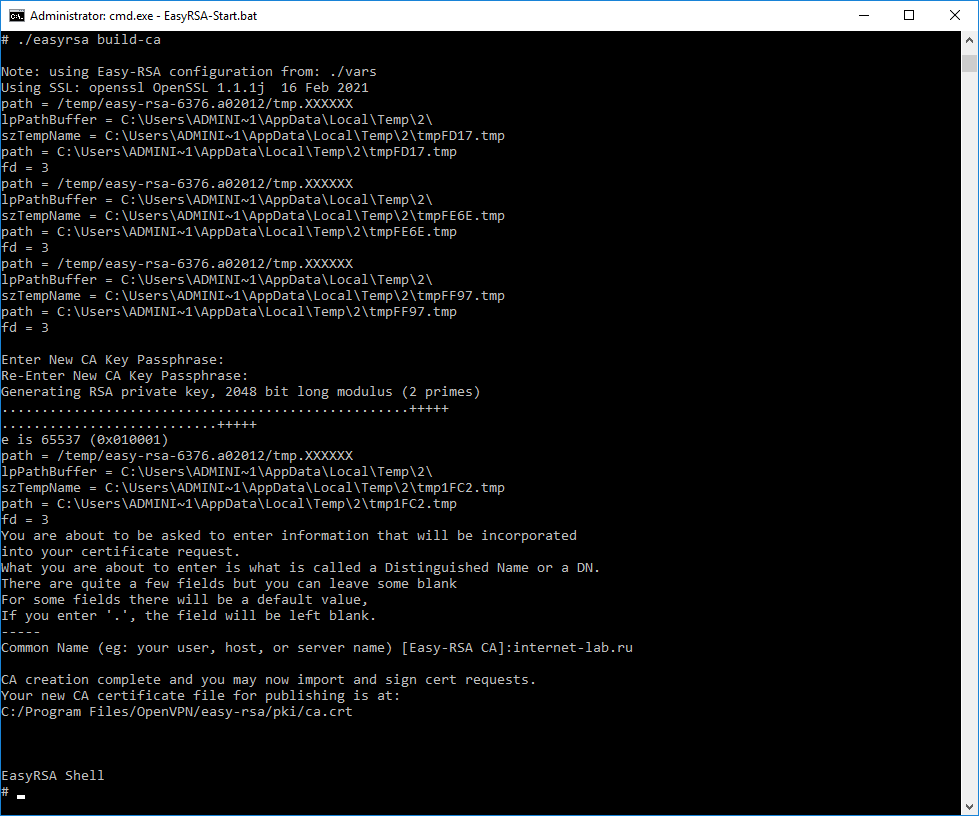
Генерируем ключ и сертификат центра сертификации. Внимание, сейчас мы наступим на грабли, исправим ошибку и снова вернёмся к генерации файлов для центра сертификации.
./easyrsa build-caНас попросят для раза ввести пароль. Придумываем и вводим.
Получаем ошибку.
Extra arguments given.
genrsa: Use -help for summary.Easy-RSA error:
Failed create CA private key
Исправим этот баг. Мне не совсем понятно, почему нельзя было всё сделать сразу по-человечески, чтобы люди не встречали эту ошибку. Копируем файл C:Program FilesOpenVPNeasy-rsavars.example, называем копию C:Program FilesOpenVPNeasy-rsavars.
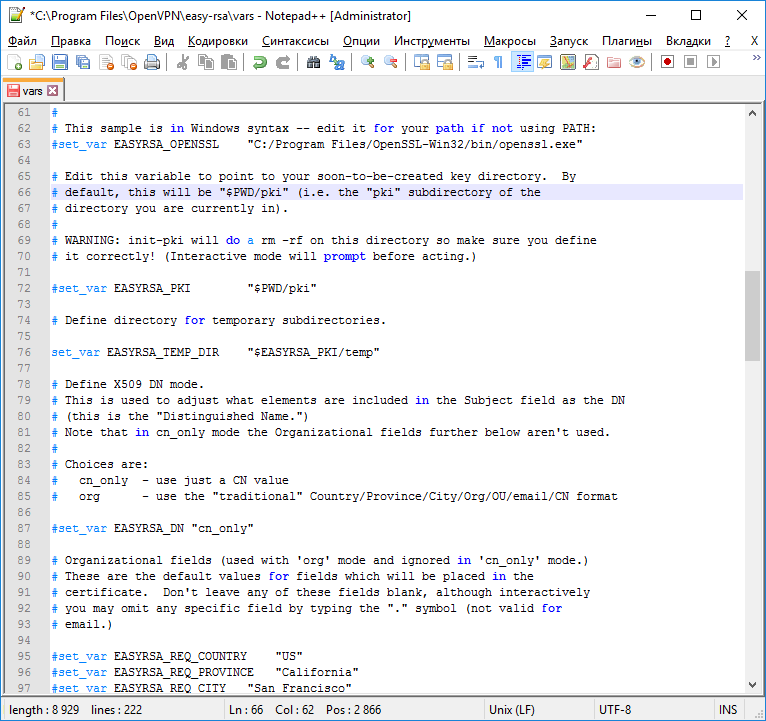
Редактируем C:Program FilesOpenVPNeasy-rsavars. В данном файле можно много чего прописать, но я не буду на этом сейчас останавливаться подробно. Находим строку:
#set_var EASYRSA_TEMP_DIR "$EASYRSA_PKI"И заменяем её на:
set_var EASYRSA_TEMP_DIR "$EASYRSA_PKI/temp"Собственно, ошибка и заключалась в том, что оболочка по какой-то причине не могла создать временный файл.
Генерируем ключ и сертификат центра сертификации:
./easyrsa build-caНас попросят для раза ввести пароль. Придумываем и вводим. После нас просят указать Common Name для центра сертификации, указываю «internet-lab.ru».
Операция проходит успешно.
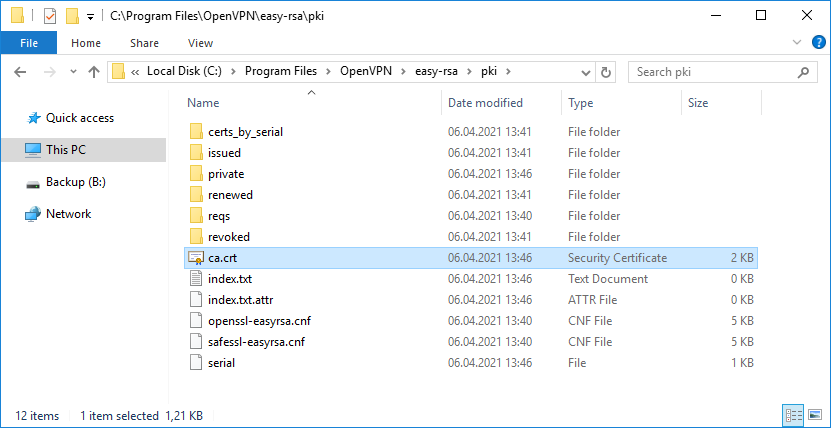
Создаётся сертификат центра сертификации:
- C:Program FilesOpenVPNeasy-rsapkica.crt
Сертификат создаётся на 10 лет, это значение можно переопределить в файле vars.
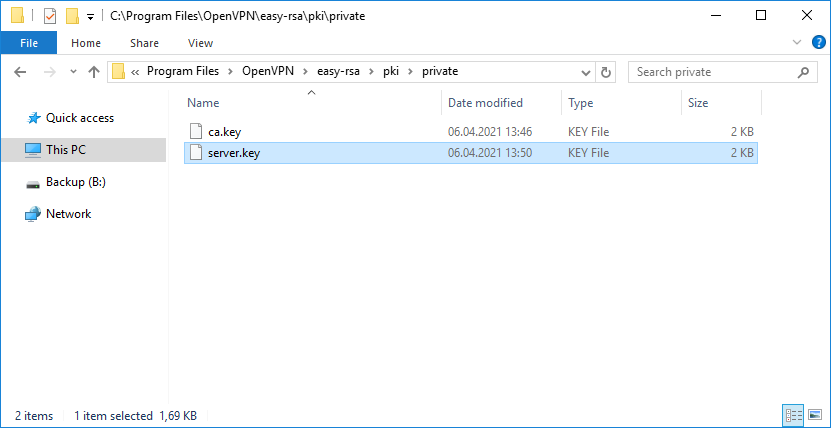
И ключ центра сертификации:
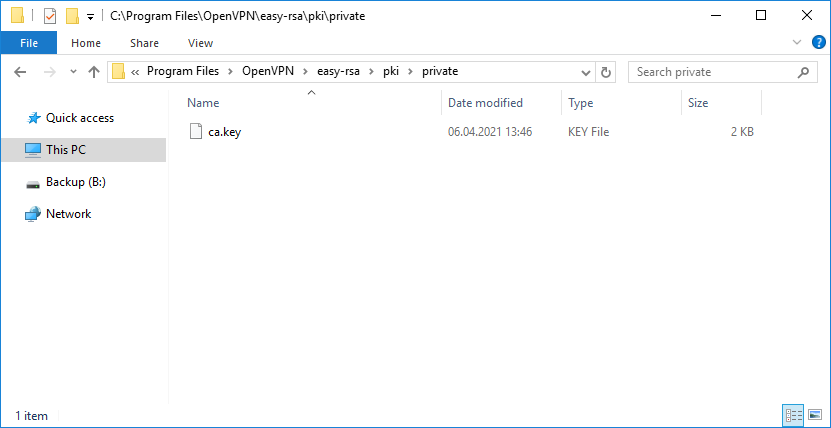
- C:Program FilesOpenVPNeasy-rsapkiprivateca.key
Ключ секретный, никому не показываем. он будет храниться на сервере.
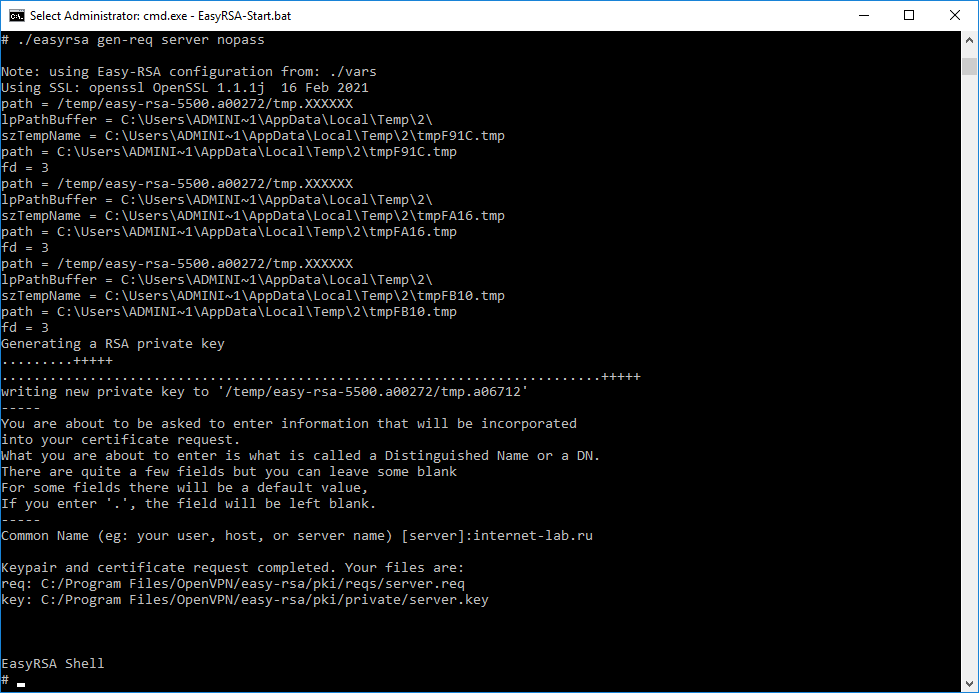
Генерируем ключ и запрос на сертификат сервера, назовём сервер именем «server«:
./easyrsa gen-req server nopassНас просят указать Common Name для сервера, указываю «internet-lab.ru».
Операция проходит успешно.
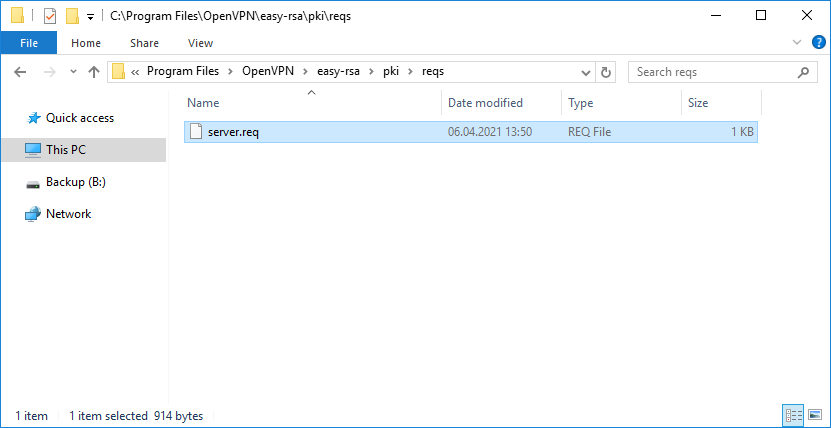
Создаётся запрос на сертификат сервера:
- C:Program FilesOpenVPNeasy-rsapkireqsserver.req
И ключ сервера:
- C:Program FilesOpenVPNeasy-rsapkiprivateserver.key
Ключ секретный, никому не показываем. он будет храниться на сервере.
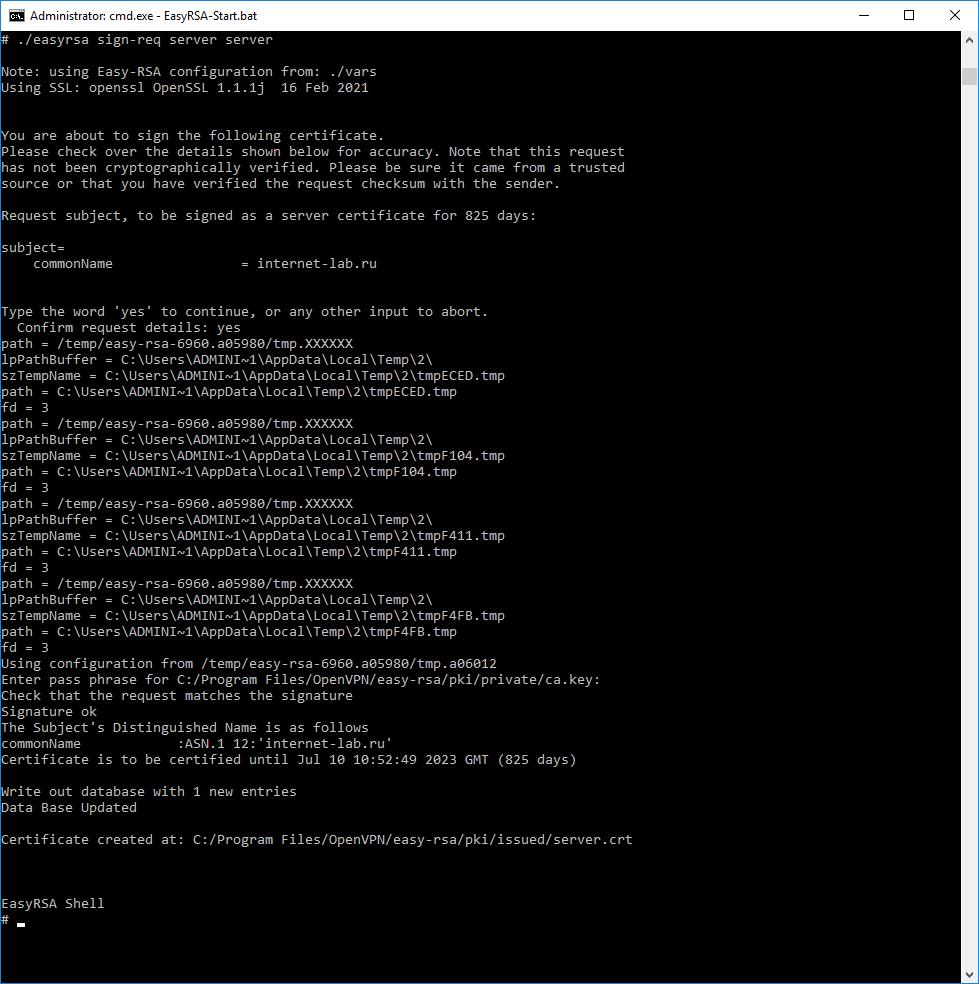
Для создания сертификата сервера нужно подписать запрос на сертификат:
./easyrsa sign-req server serverДля подписи нужно ввести слово «yes» и указать пароль от центра сертификации.
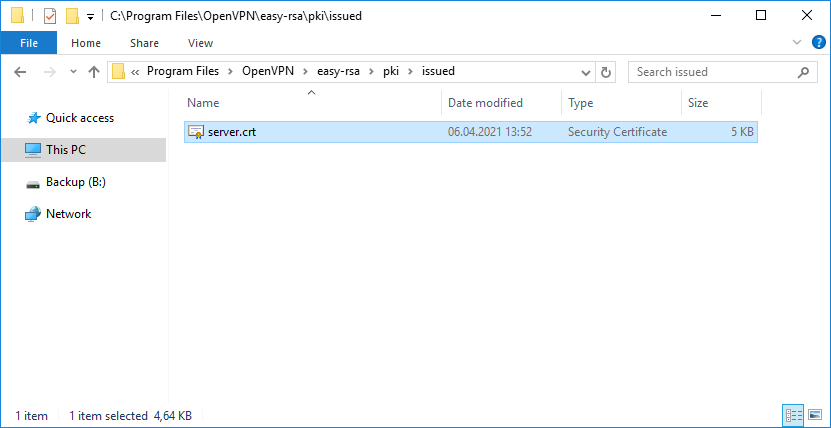
Создаётся сертификат сервера:
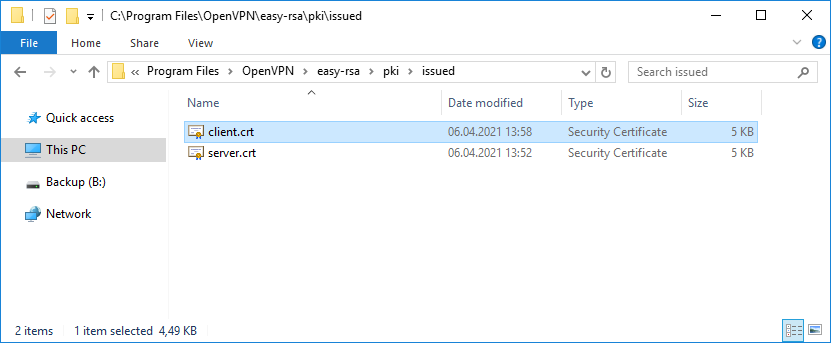
- C:Program FilesOpenVPNeasy-rsapkiissuedserver.crt
Сертификат сервера создаётся на 825 дней, это значение можно переопределить в файле vars.
Теперь создадим клиентский сертификат. По хорошему клиентский ключ следует запаролить, чтобы исключить утечку при передаче. Для этого есть несколько способов.
Первый
-
На клиентской машине генерируем запрос на сертификат клиента и ключ без пароля:
./easyrsa init-pki ./easyrsa gen-req client nopass - Переносим REQ файл запроса на сертификат клиента на машину с нашим CA, импортируем, подписываем, отсылаем сгенерированный сертификат CRT обратно клиенту:
./easyrsa import-req /path/to/client.req client ./easyrsa sign-req client client
Второй
-
а машине с CA генерируем сертификат клиента и ключ с паролем:
./easyrsa gen-req client ./easyrsa sign-req client client - Переносим файлы клиенту, сообщаем пароль. Клиент снимает пароль с полученного ключа:
openssl rsa -in client.key -out clientnew.key
Третий
Но поскольку я генерирую ключ сам для себя, то воспользуюсь небезопасным третьим способом.
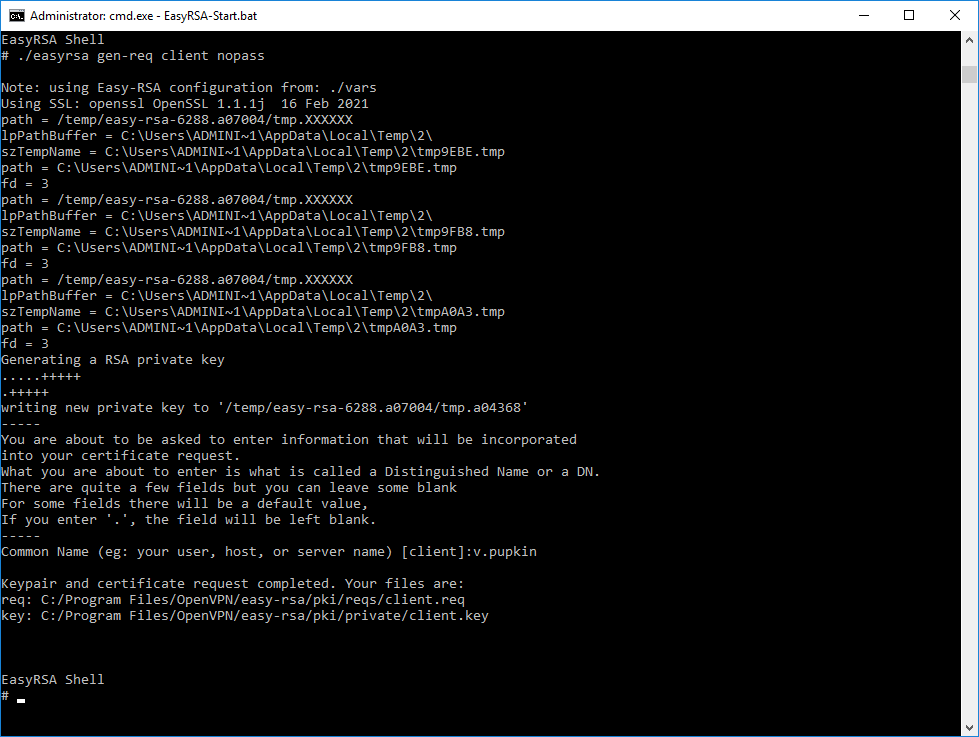
Генерируем ключ и запрос на сертификат клиента, назовём клиента именем «client«:
./easyrsa gen-req client nopassНас просят указать Common Name для клиента, указываю «v.pupkin».
Операция проходит успешно.
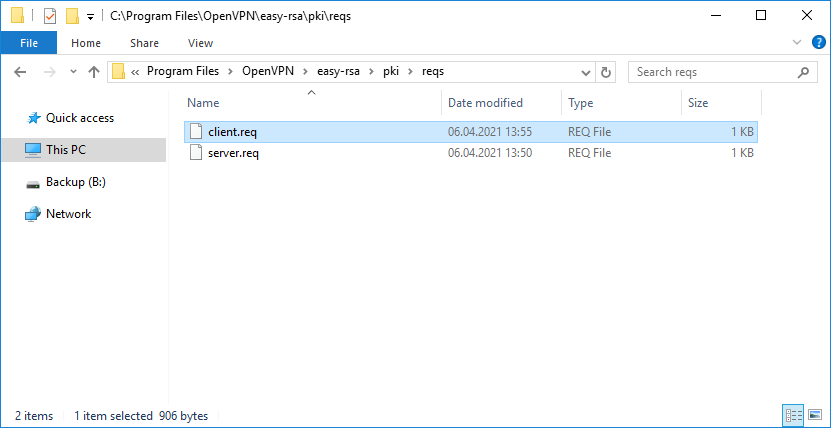
Создаётся запрос на сертификат клиента:
- C:Program FilesOpenVPNeasy-rsapkireqsclient.req
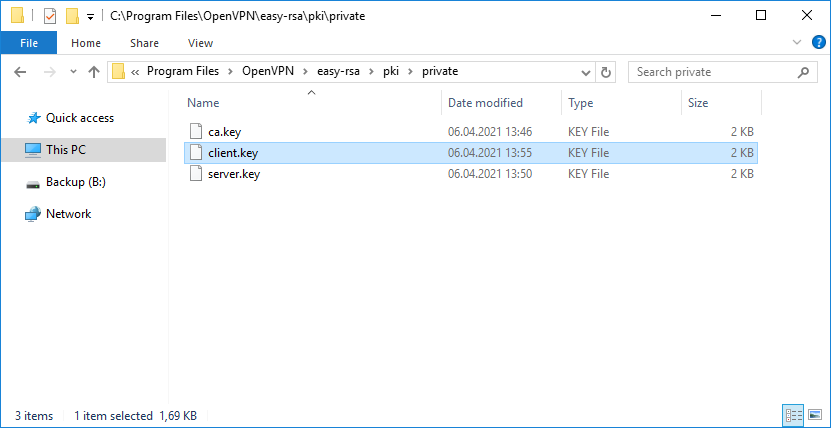
И ключ клиента:
- C:Program FilesOpenVPNeasy-rsapkiprivateclient.key
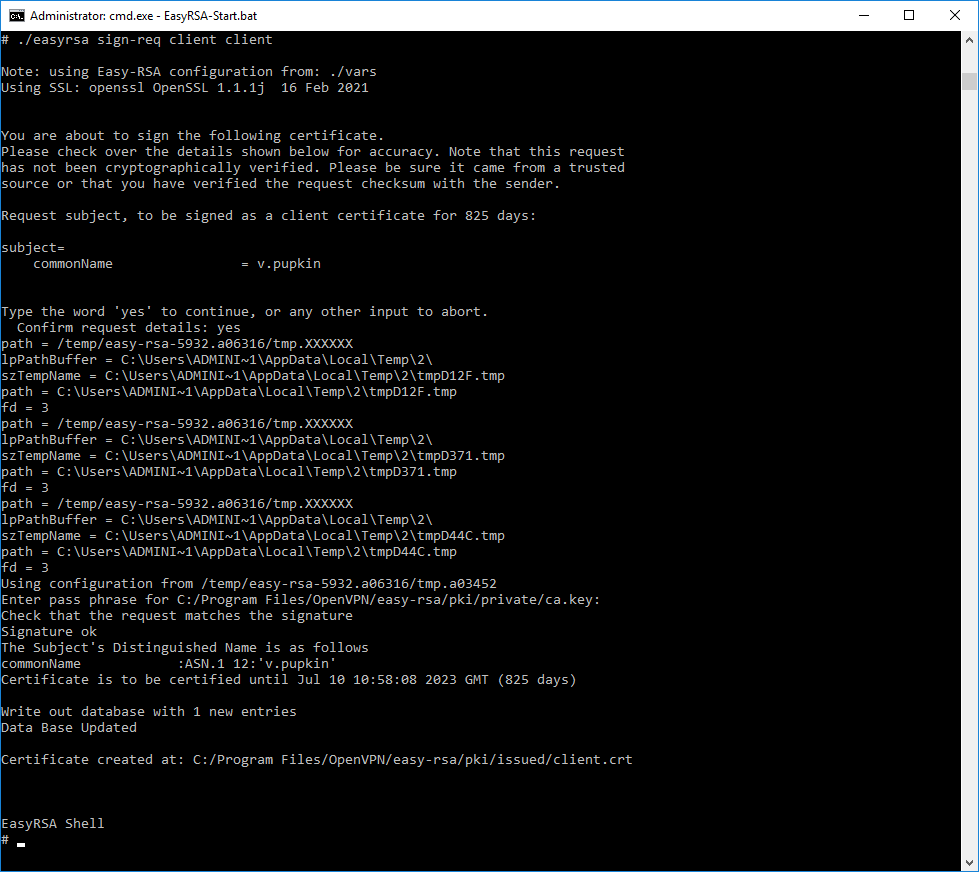
Для создания сертификата клиента нужно подписать запрос на сертификат:
./easyrsa sign-req client clientДля подписи нужно ввести слово «yes» и указать пароль от центра сертификации.
Создаётся сертификат клиента:
- C:Program FilesOpenVPNeasy-rsapkiissuedclient.crt
Сертификат сервера создаётся на 825 дней, это значение можно переопределить в файле vars.
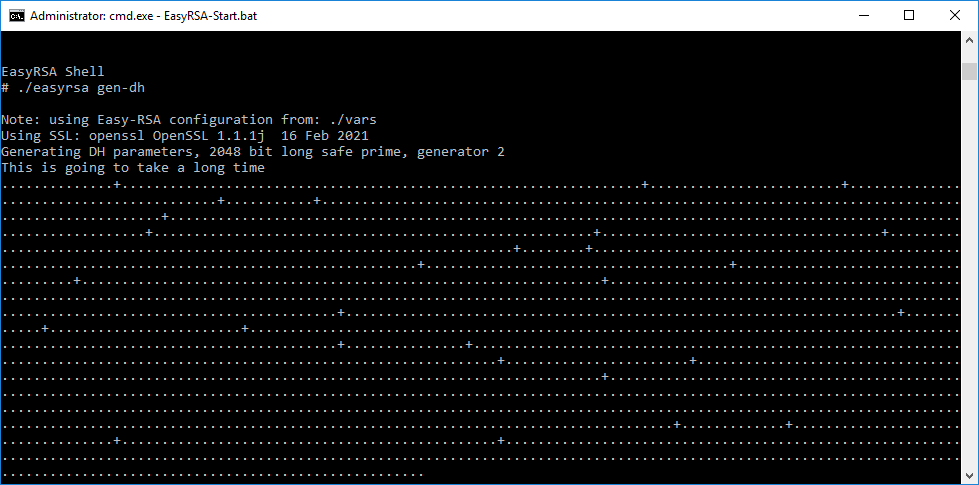
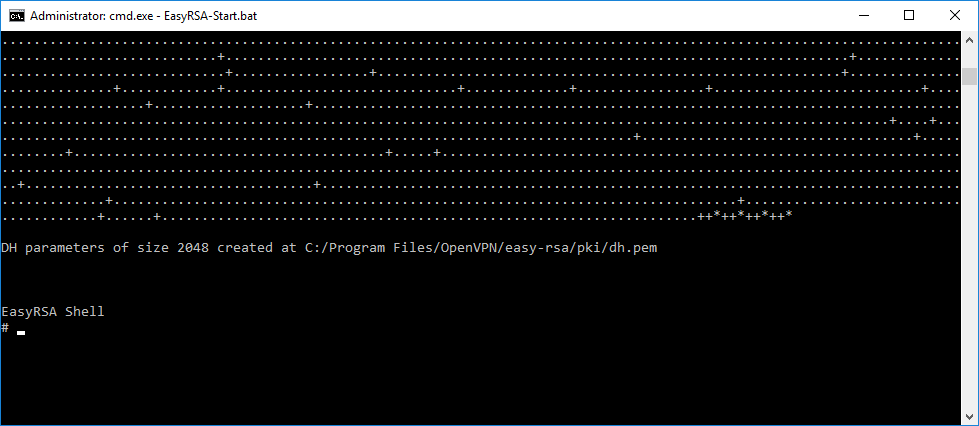
Генерируем ключ Диффи-Хеллмана:
./easyrsa gen-dhОперация займёт некоторое время.
Создаётся файл:
- C:Program FilesOpenVPNeasy-rsapkidh.pem
Я на сервере собираюсь использовать tls-auth для дополнительной проверки целостности, это обеспечит дополнительный уровень безопасности протокола SSL/TLS при создании соединения:
- Сканирование прослушиваемых VPN-сервером портов
- Инициация SSL/TLS-соединения несанкционированной машиной на раннем этапе
- DoS-атаки и флуд на порты OpenVPN
- Переполнение буфера SSL/TLS
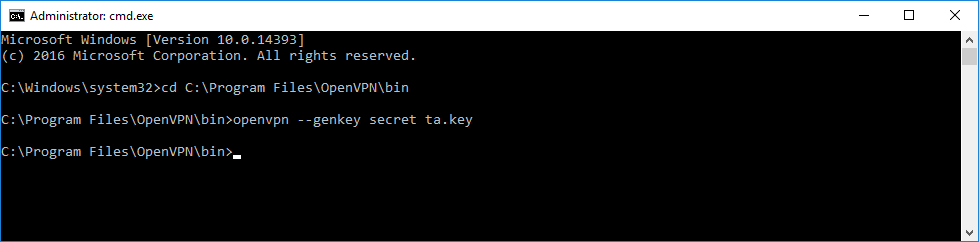
При использовании tls-auth на клиенте не понадобится ключ Диффи-Хеллмана, но пусть будет. Генерируем ключ tls-auth. Для этого запускаем командную строку под администратором и выполняем:
cd C:Program FilesOpenVPNbin
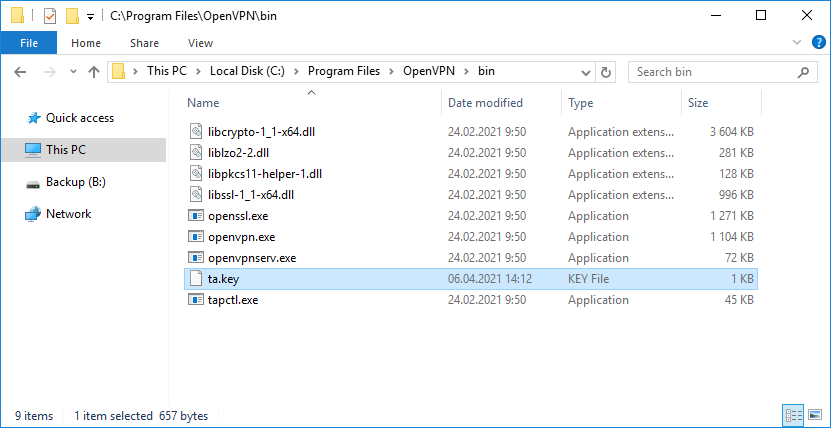
openvpn --genkey secret ta.keyВ папке C:Program FilesOpenVPNbin создаётся файл ta.key.
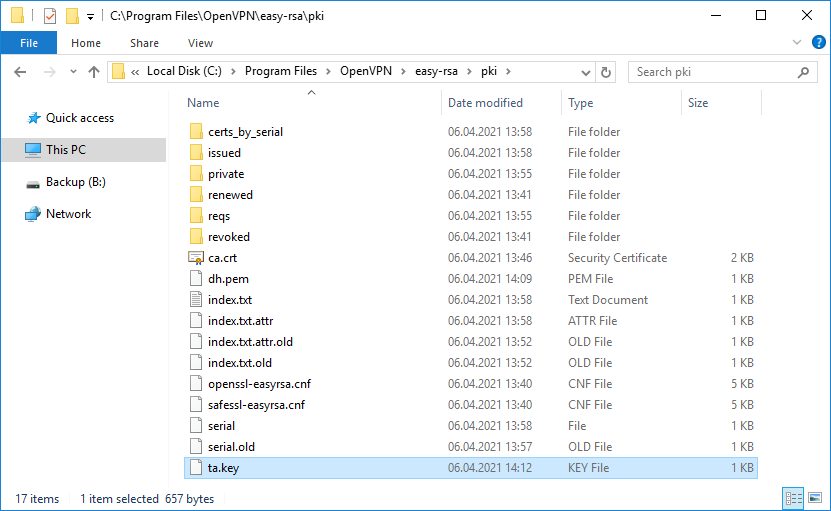
Переносим его в папку C:Program FilesOpenVPNeasy-rsapki.
Минимальный набор сертификатов сгенерирован.
Настройка OpenVPN сервера
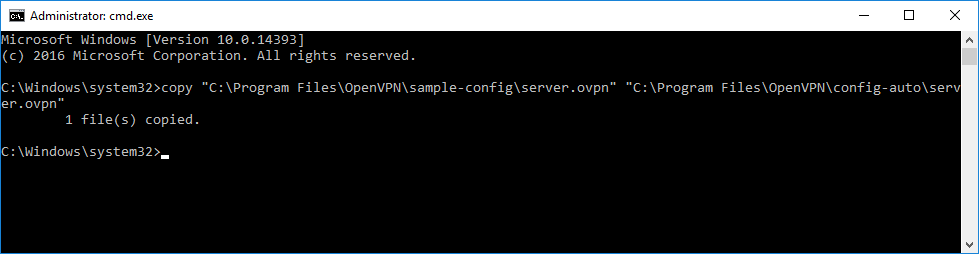
Создадим конфигурационный файл сервера C:Program FilesOpenVPNconfig-autoserver.ovpn:
copy "C:Program FilesOpenVPNsample-configserver.ovpn" "C:Program FilesOpenVPNconfig-autoserver.ovpn"Открываем блокнотом и редактируем:
notepad "C:Program FilesOpenVPNconfig-autoserver.ovpn"Лучше изучить конфигурационный файл, я предлагаю свой вариант конфига:
port 1194
proto tcp
dev tun
ca "C:\Program Files\OpenVPN\easy-rsa\pki\ca.crt"
cert "C:\Program Files\OpenVPN\easy-rsa\pki\issued\server.crt"
key "C:\Program Files\OpenVPN\easy-rsa\pki\private\server.key" # This file should be kept secret
dh "C:\Program Files\OpenVPN\easy-rsa\pki\dh.pem"
server 10.8.0.0 255.255.255.0
ifconfig-pool-persist ipp.txt
duplicate-cn
keepalive 10 120
tls-auth "C:\Program Files\OpenVPN\easy-rsa\pki\ta.key" 0 # This file is secret
cipher AES-256-GCM
persist-key
persist-tun
status "C:\Program Files\OpenVPN\log\status.log"
log "C:\Program Files\OpenVPN\log\openvpn.log"
verb 4
mute 20
windows-driver wintunУ меня здесь указаны пути к ключам и сертификатам, используется порт TCP 1194. Параметр duplicate-cn позволяет подключаться всем клиентам по одному общему сертификату, но это небезопасно и не рекомендуется. Используйте только в тестовых целях. Я использую для того, чтобы с помощью одного и того же сертификата подключиться к OpenVPN серверу и с клиентской машины и со смартфона. Параметр windows-driver wintun подключает использование драйвера WinTun. И что им стоило этот параметр указать в примере конфигурации? Остальное по умолчанию.
ВНИМАНИЕ: в конфигурационных файлах допускается в путях использование прямого слеша:
ca «C:/Program Files/OpenVPN/easy-rsa/pki/ca.crt»
или двойного обратного слеша:
ca «C:\Program Files\OpenVPN\easy-rsa\pki\ca.crt»
Запуск OpenVPN сервера
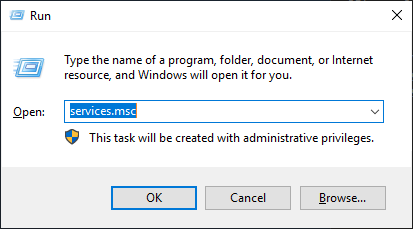
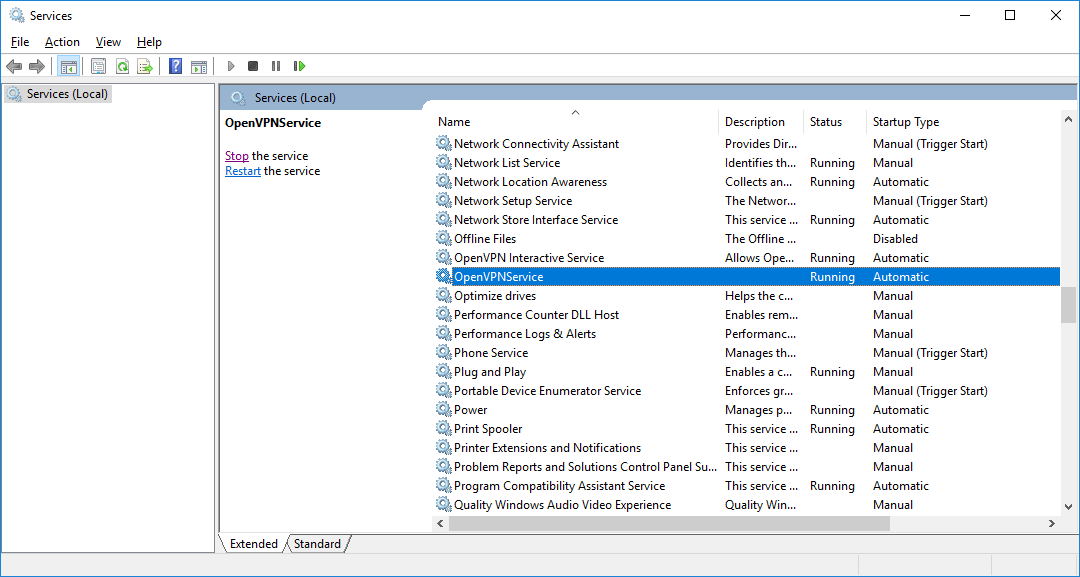
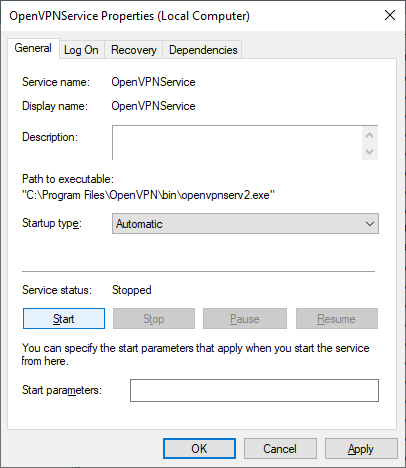
Переходим к службам:
services.mscНаходим службу OpenVPNService.
Настраиваем на автоматический запуск при загрузке сервера.
Запускаем (перезапускаем) службу.
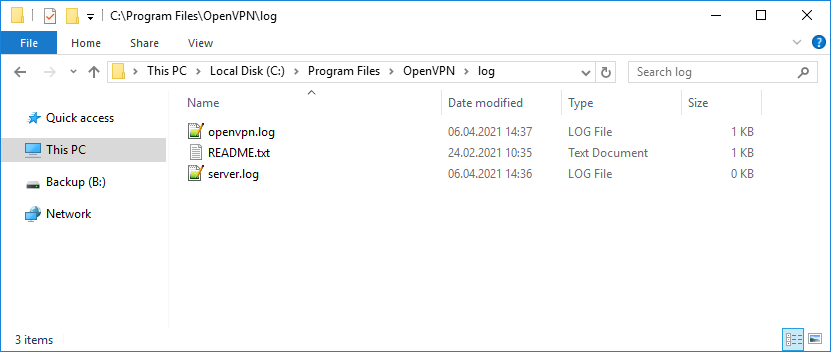
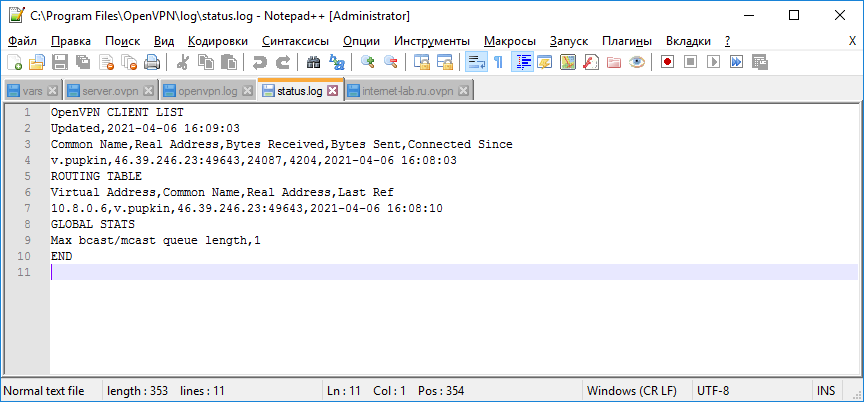
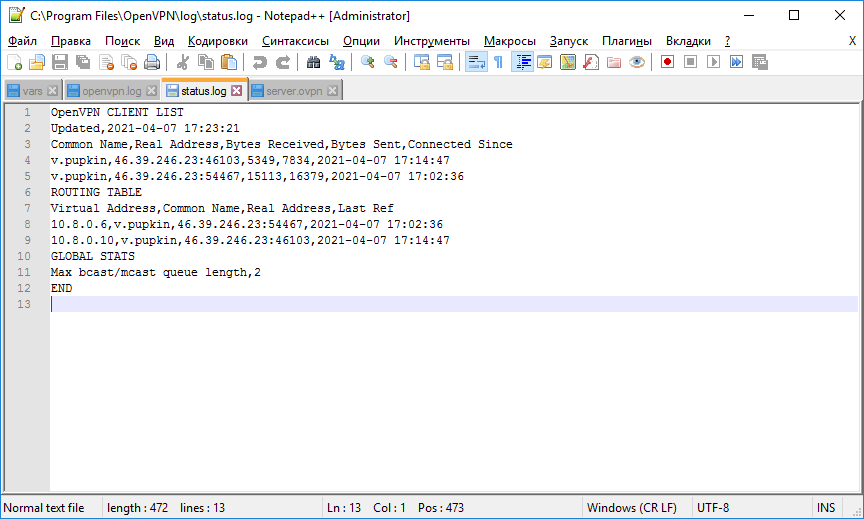
Согласно настройкам сервера в папке C:Program FilesOpenVPNlog должны появиться логи. Это один из инструментов администратора OpenVPN сервера.
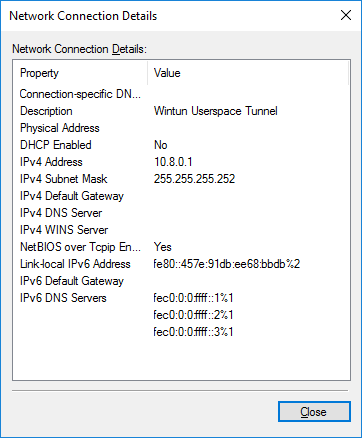
Активировался сетевой адаптер OpenVPN Wintun.
Согласно настройкам сервера IP адрес 10.8.0.1.
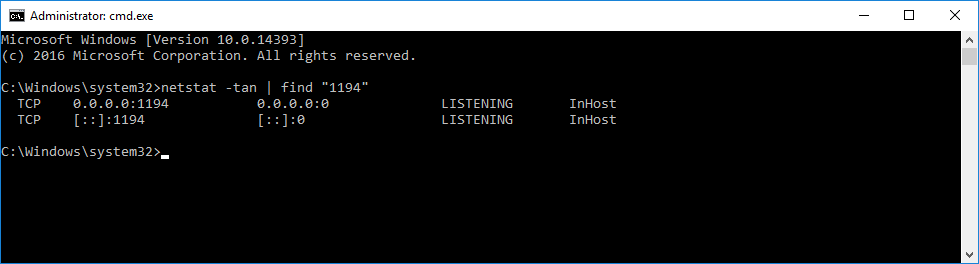
Проверяем поднялся ли порт tcp 1194:
netstat -tan | find "1194"Порт должен прослушиваться.
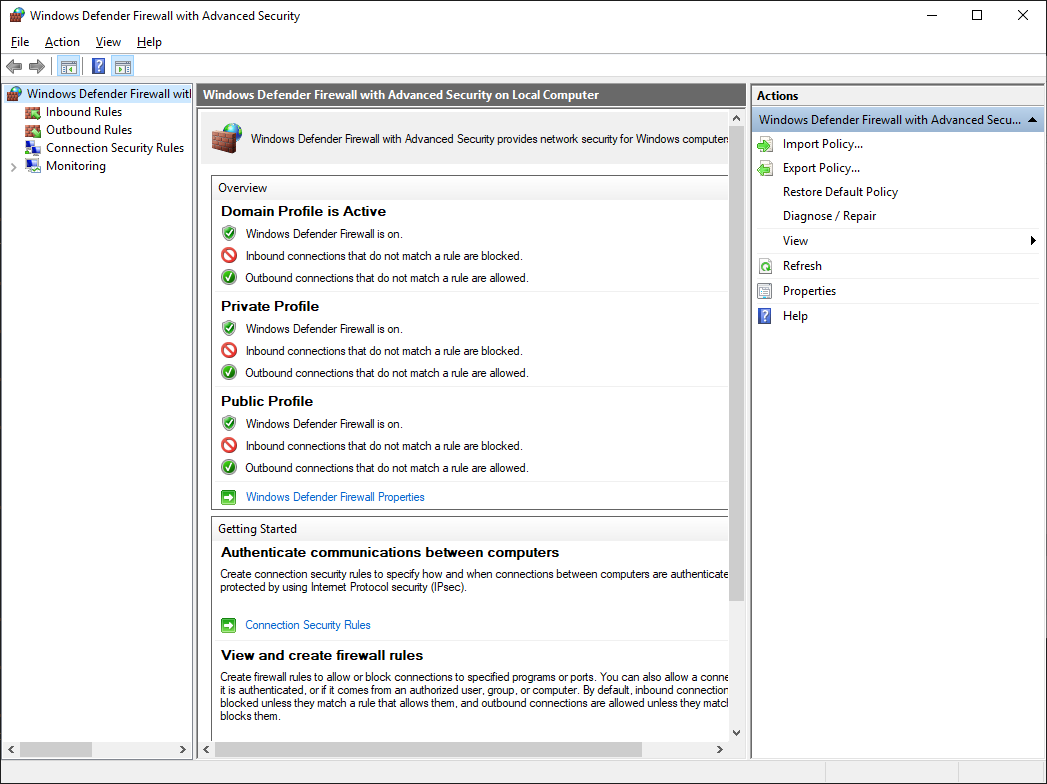
Настройка firewall
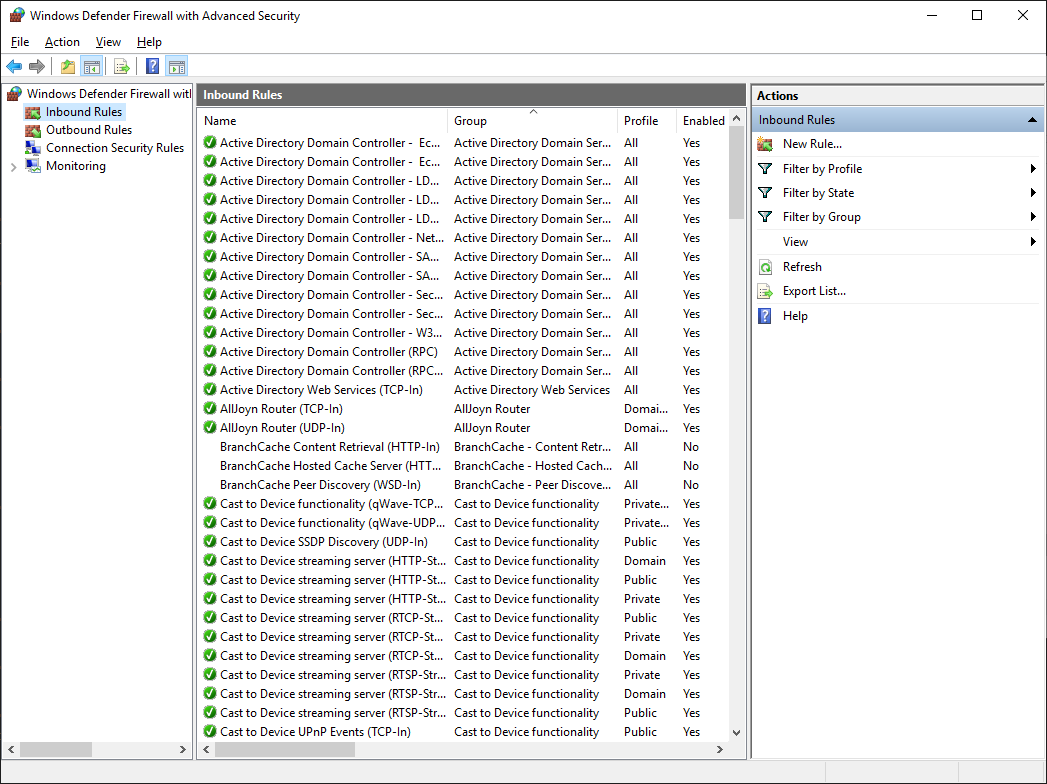
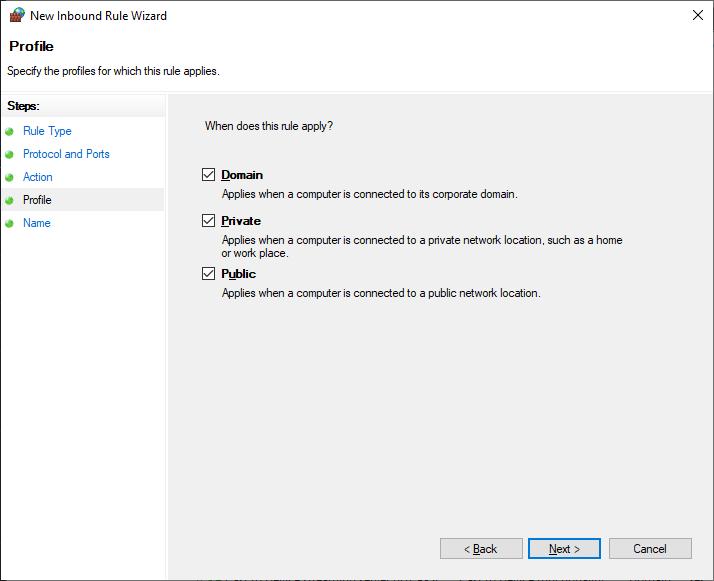
Теперь нужно настроить firewall. Открываем Windows Defender Firewall with Advanced Security.
Переходим в Inbound Rules.
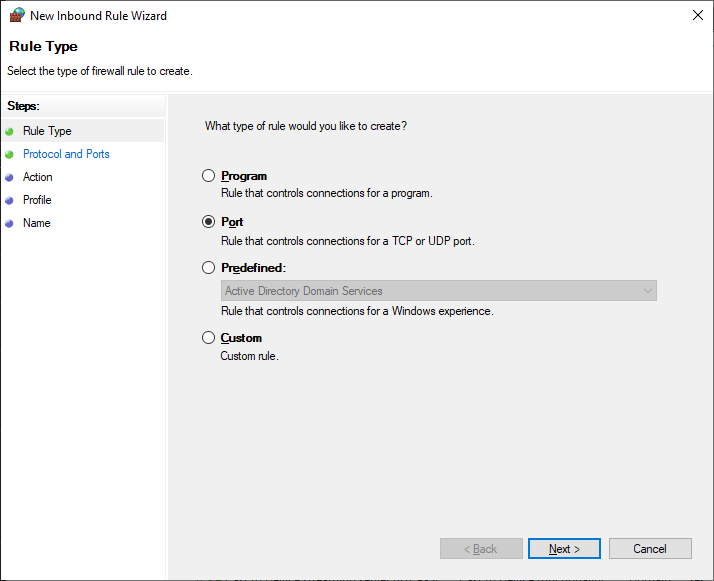
Создаём правило — New Rule…
Тип правила — Port. Next.
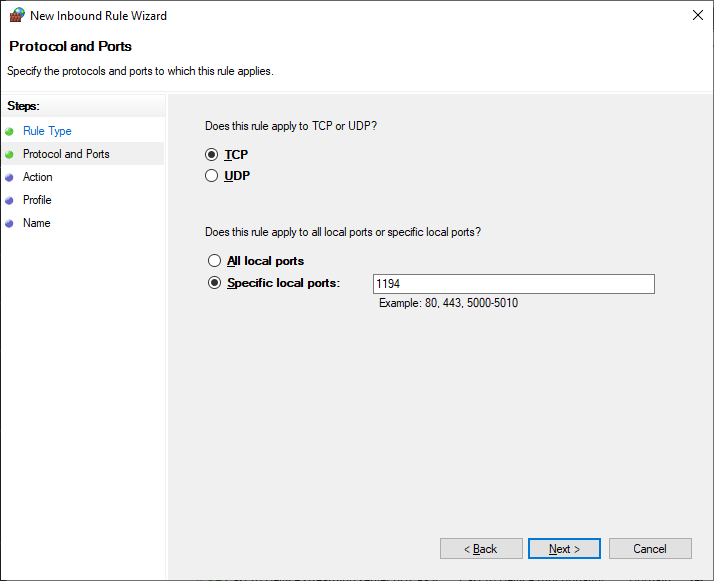
Протоколы и порты — TCP 1194. Как в настройках сервера. Next.
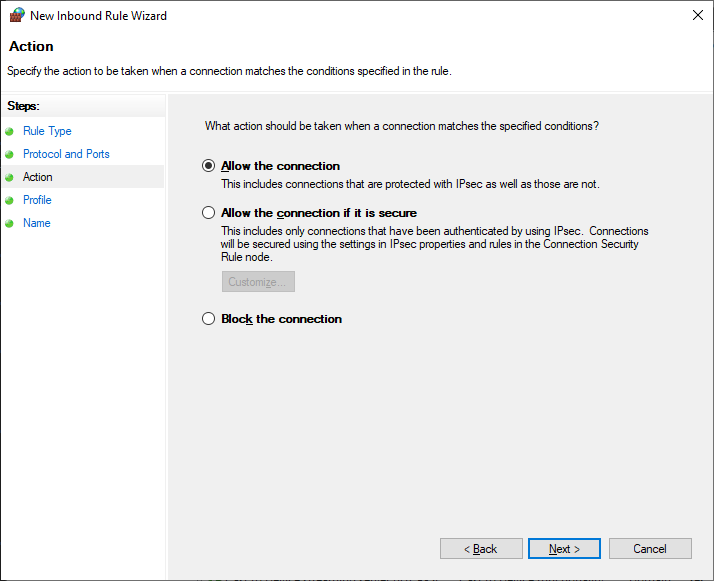
Действия — Allow the connection. Next.
Для всех сетей. Next.
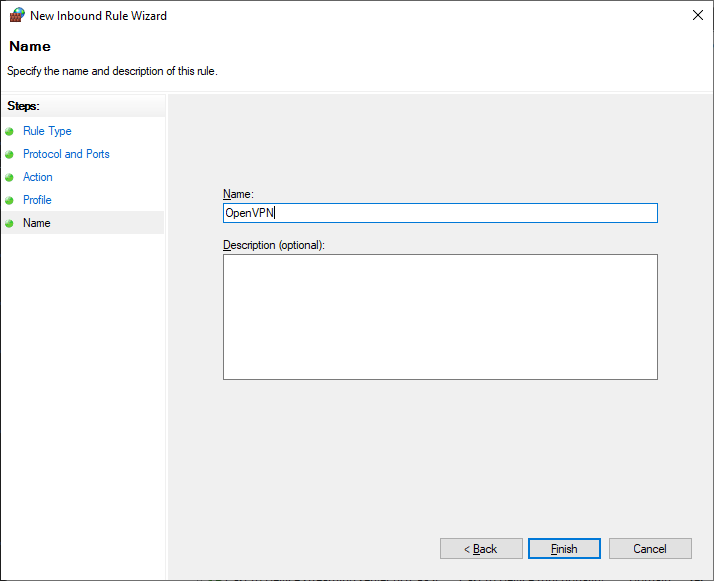
Указываем название правила — OpenVPN. Next.
Правило создано, теперь firewall не блокирует входящие TCP соединения на 1194 порту.
Настройка OpenVPN клиента на ПК Windows
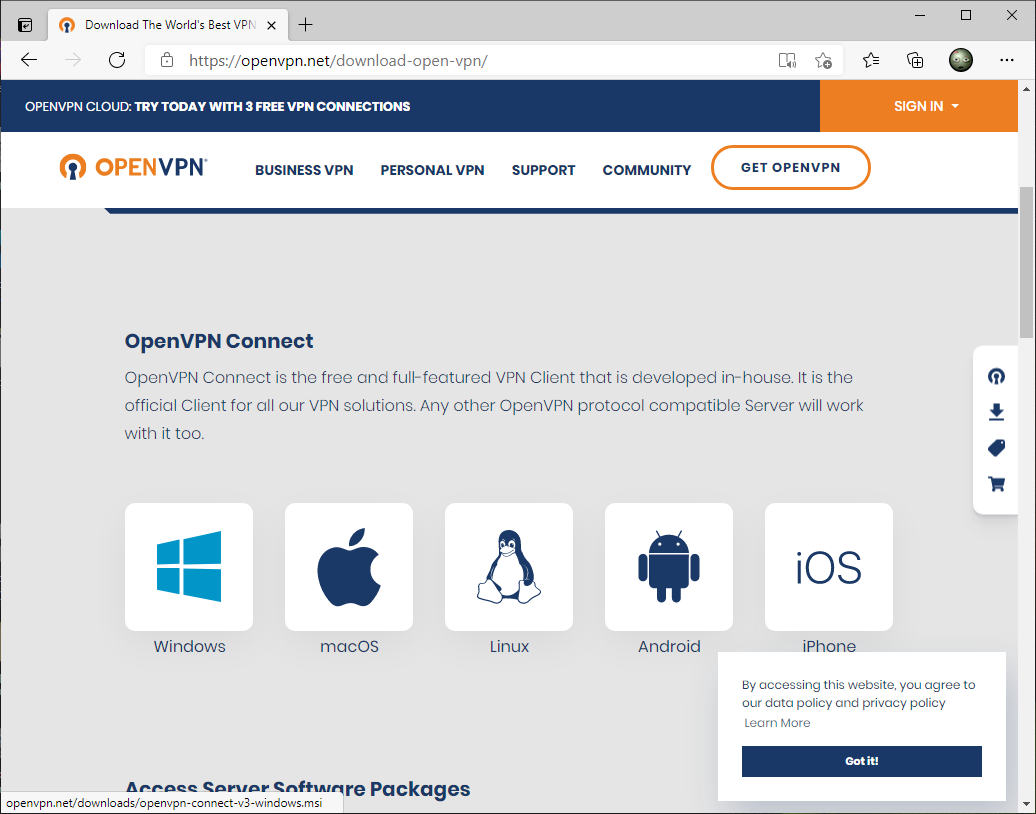
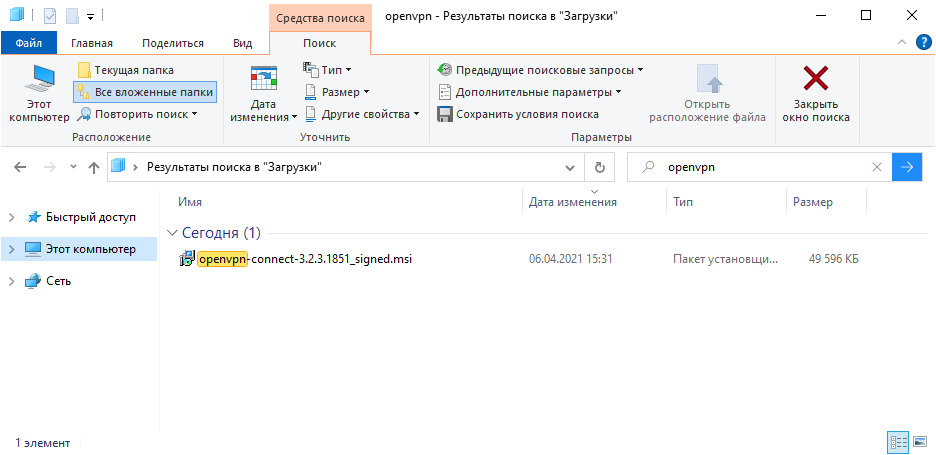
На компьютере клиента устанавливаем OpenVPN Connect.
Я скачиваю версию для Windows.
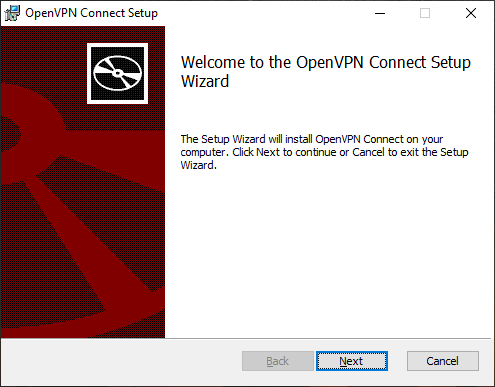
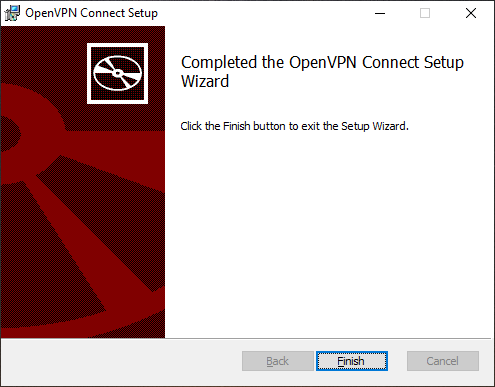
Запускаем установку.
Next.
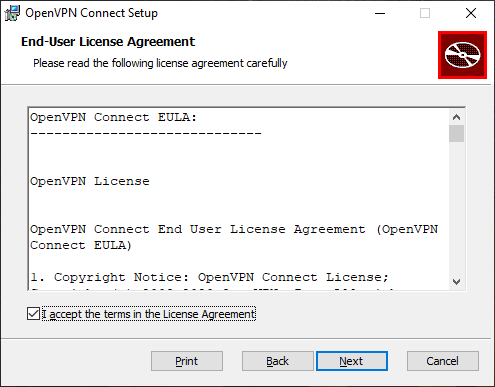
Принимаем лицензионное соглашение. Next.
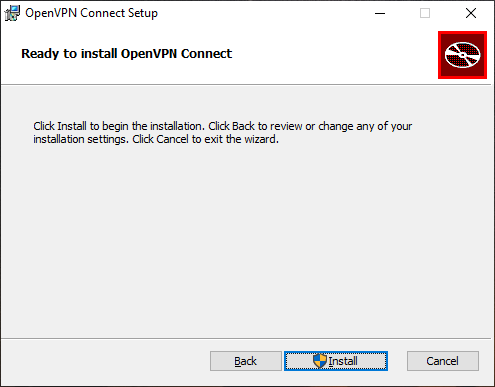
Install.
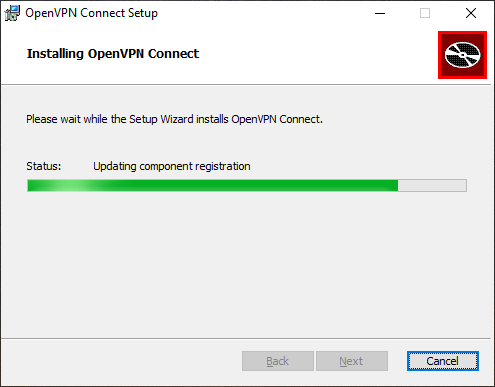
OpenVPN Connect устанавливается.
Установка завершена. Finish.
На рабочем столе появляется иконка OpenVPN Connect.
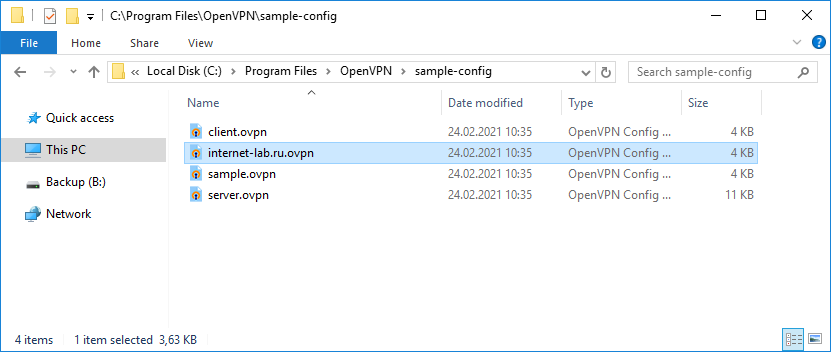
На сервере файл примера конфигурации client.ovpn копируем как internet-lab.ru.ovpn.
И редактируем:
client
dev tun
proto tcp
remote internet-lab.ru 1194
resolv-retry infinite
nobind
persist-key
persist-tun
ca ca.crt
cert client.crt
key client.key
remote-cert-tls server
tls-auth ta.key 1
cipher AES-256-GCM
verb 0
connect-retry-max 25
Здесь нужно указать протокол, порт адрес сервера и прочие параметры. Пути к ключам и сертификатам относительные.
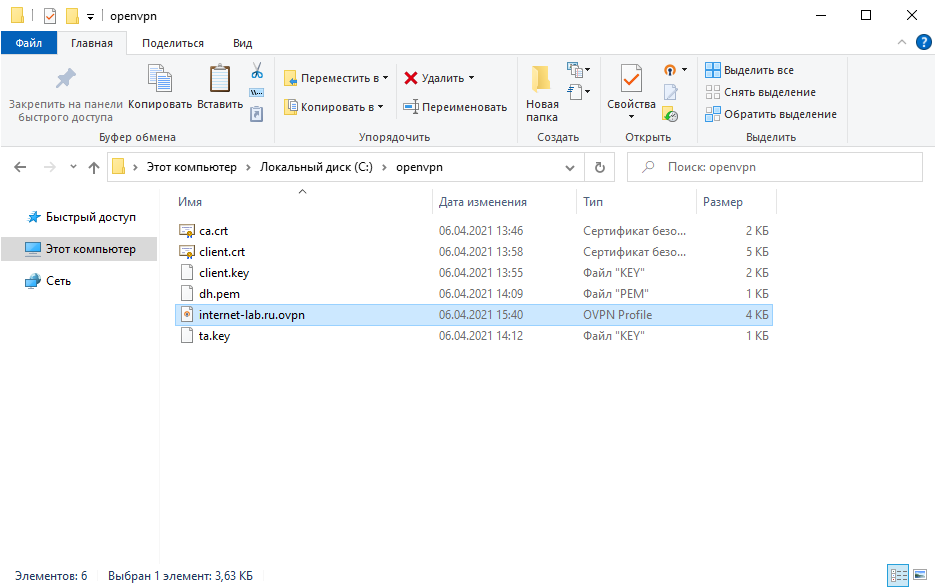
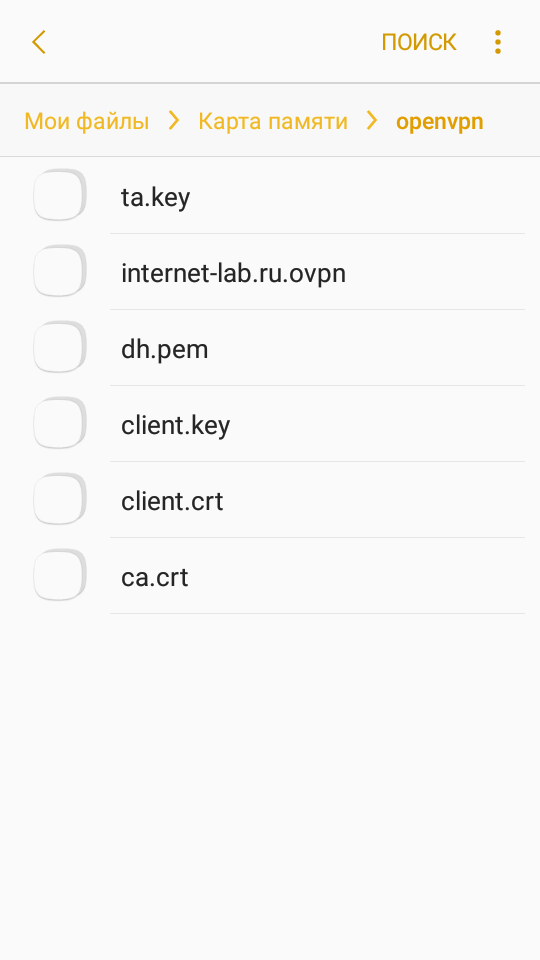
Создаём директорию, например, C:openvpn. Копируем в неё с сервера файлы:
- ca.crt
- client.crt
- client.key
- dh.pem
- ta.key
- internet-lab.ru.ovpn
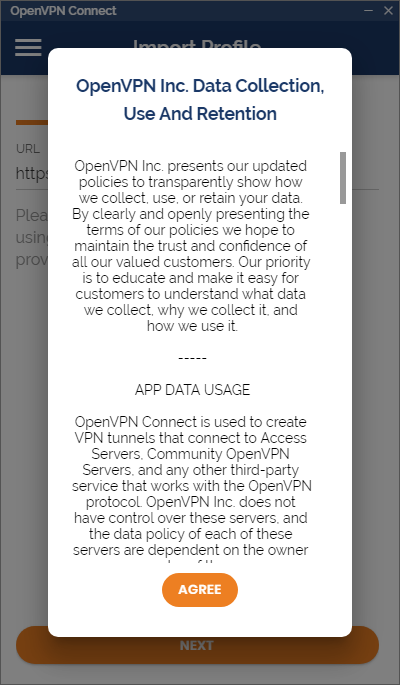
Запускаем OpenVPN Connect.
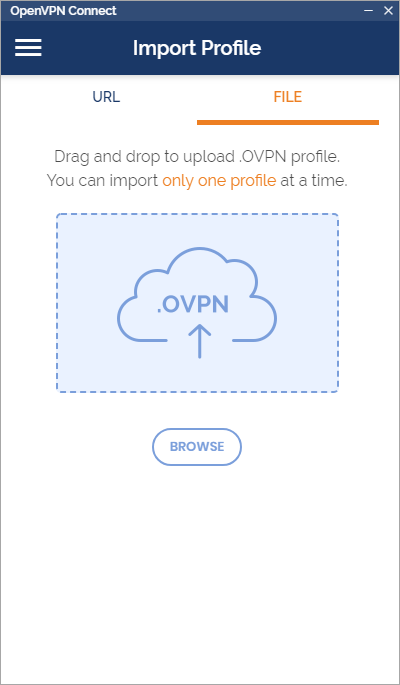
Agree. Переключаемся на File.
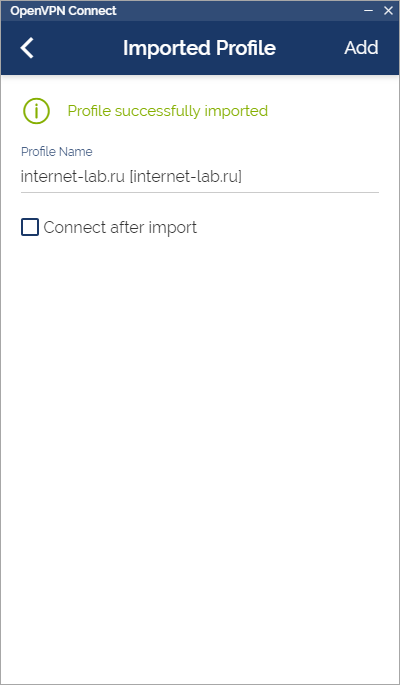
Перетаскиваем мышкой в окно файл C:openvpninternet-lab.ru.ovpn, или указываем через кнопку Browse.
Ставим галку «Connect after import».
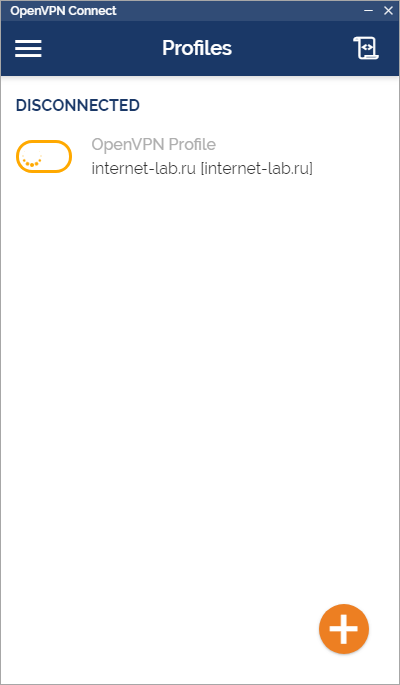
Коннектимся.
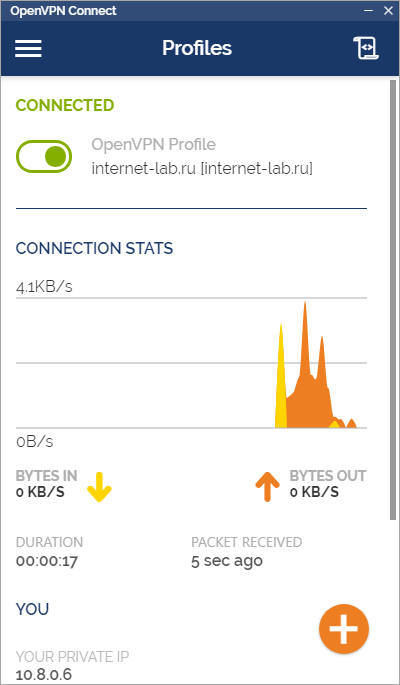
Соединение с OpenVPN сервером установлено.
В логах сервера видим, что соединился юзер v.pupkin.
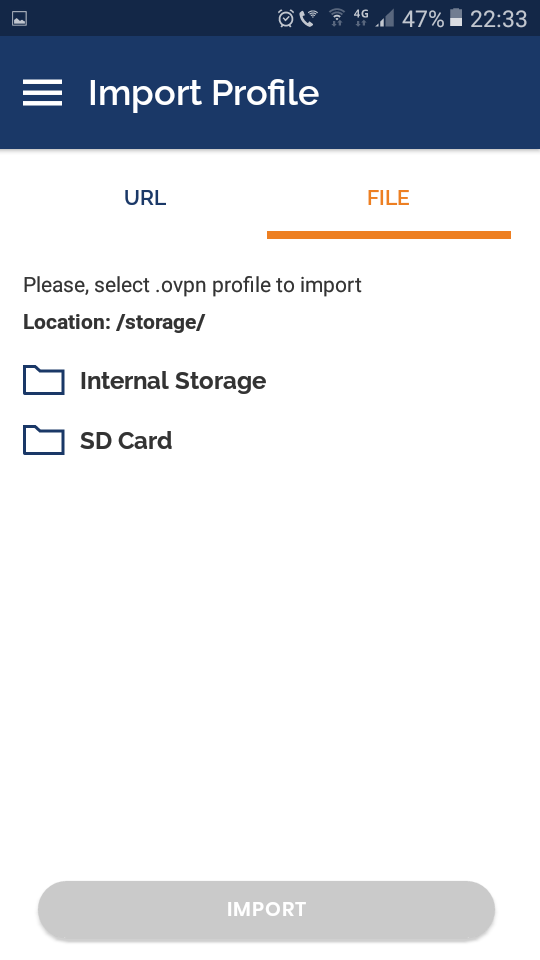
Настройка OpenVPN клиента на смартфоне Android
Копируем на телефон все те же файлы, что и для клиента.
Устанавливаем приложение OpenVPN Connect.
Запускаем.
Agree.
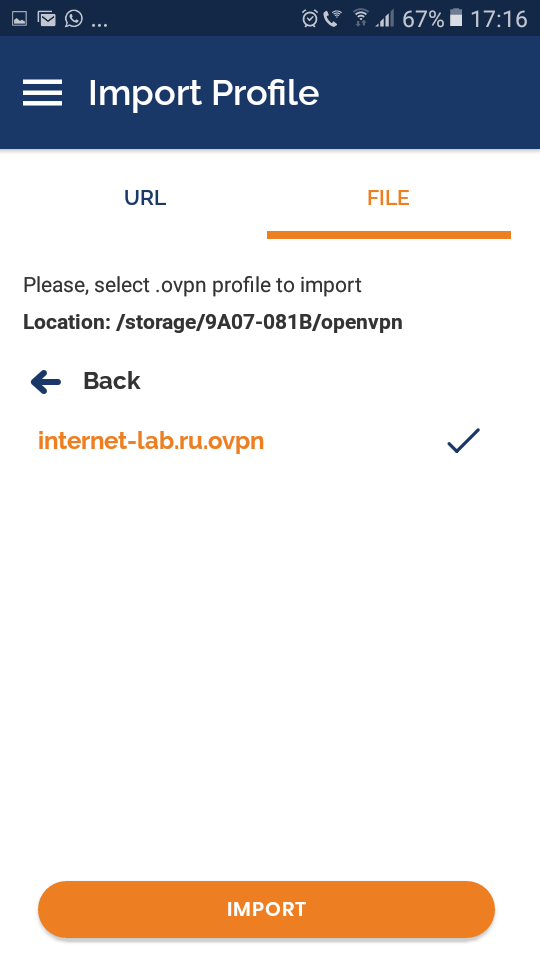
Выбираем File. Указываем путь к файлу internet-lab.ru.ovpn.
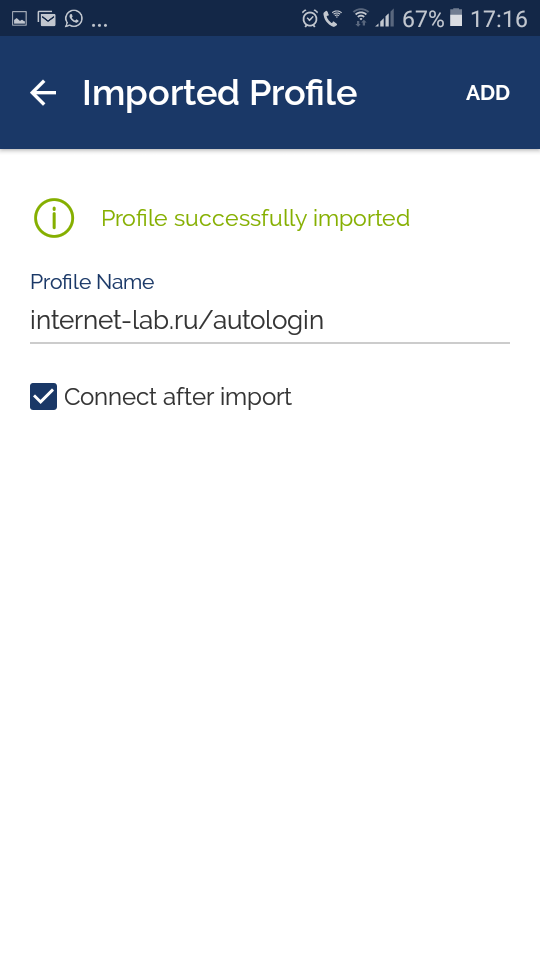
Import.
Ставим галку «Connect after import».
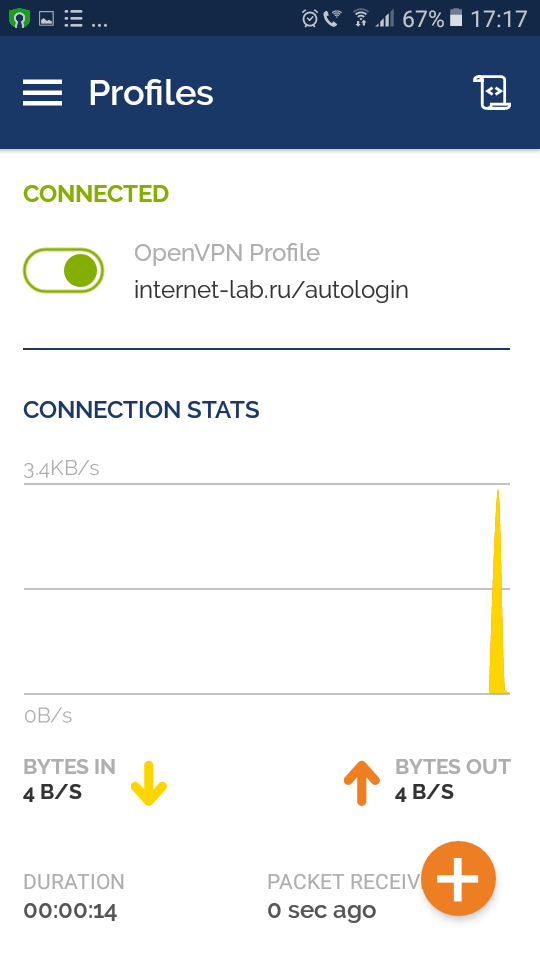
Соединение с OpenVPN сервером установлено.
В логах сервера видим, что соединился второй юзер v.pupkin.
Отзыв сертификата
cd C:Program FilesOpenVPNeasy-rsa
EasyRSA-Start.bat
./easyrsa revoke clientСсылки
Установка OpenVPN сервера на Windows
Recommend Projects
-
React
A declarative, efficient, and flexible JavaScript library for building user interfaces.
-
Vue.js
🖖 Vue.js is a progressive, incrementally-adoptable JavaScript framework for building UI on the web.
-
Typescript
TypeScript is a superset of JavaScript that compiles to clean JavaScript output.
-
TensorFlow
An Open Source Machine Learning Framework for Everyone
-
Django
The Web framework for perfectionists with deadlines.
-
Laravel
A PHP framework for web artisans
-
D3
Bring data to life with SVG, Canvas and HTML. 📊📈🎉
Recommend Topics
-
javascript
JavaScript (JS) is a lightweight interpreted programming language with first-class functions.
-
web
Some thing interesting about web. New door for the world.
-
server
A server is a program made to process requests and deliver data to clients.
-
Machine learning
Machine learning is a way of modeling and interpreting data that allows a piece of software to respond intelligently.
-
Visualization
Some thing interesting about visualization, use data art
-
Game
Some thing interesting about game, make everyone happy.
Recommend Org
-
Facebook
We are working to build community through open source technology. NB: members must have two-factor auth.
-
Microsoft
Open source projects and samples from Microsoft.
-
Google
Google ❤️ Open Source for everyone.
-
Alibaba
Alibaba Open Source for everyone
-
D3
Data-Driven Documents codes.
-
Tencent
China tencent open source team.
Looks like you’re using OpenVPN Connect on Windows and I assume it’s version 3.In that version TAP is no longer supported. You should use TUN mode.
I believe OpenVPN Community Edition 2.5 (https://openvpn.net/community-downloads/ Opens a new window) still supports TAP.
Better option is to just turn off TAP altogether if you can in the Netgear. The screenshot above does not seem to suggest a way to only configure TUN. Perhaps in Advanced settings you can do such a thing?
You can look at modifying the generated openvpn configuration file and see about removing the TAP portions. The ovpn file is usually just a text file you can edit in Notepad.
Was this post helpful?
thumb_up
thumb_down
OP
RDB001
This person is a verified professional.
Verify your account
to enable IT peers to see that you are a professional.
jalapeno
Looks like you’re using OpenVPN Connect on Windows and I assume it’s version 3.In that version TAP is no longer supported. You should use TUN mode.
I believe OpenVPN Community Edition 2.5 (https://openvpn.net/community-downloads/ Opens a new window) still supports TAP.
Better option is to just turn off TAP altogether if you can in the Netgear. The screenshot above does not seem to suggest a way to only configure TUN. Perhaps in Advanced settings you can do such a thing?
You can look at modifying the generated openvpn configuration file and see about removing the TAP portions. The ovpn file is usually just a text file you can edit in Notepad.
It looks like the TAP can not be disabled through the interface. I will attempt to download version 2.5 to see if I can get this to work. If that doesn’t work, what steps would need to be taken to remove the openvpn configuration files?
Was this post helpful?
thumb_up
thumb_down
OP
RDB001
This person is a verified professional.
Verify your account
to enable IT peers to see that you are a professional.
jalapeno
Here is the error I am receiving when using version 2.5:
2021-02-23 09:35:59 WARNING: Compression for receiving enabled. Compression has been used in the past to break encryption. Sent packets are not compressed unless «allow-compression yes» is also set.
2021-02-23 09:35:59 us=883743 DEPRECATED OPTION: —cipher set to ‘AES-128-CBC’ but missing in —data-ciphers (AES-256-GCM:AES-128-GCM). Future OpenVPN version will ignore —cipher for cipher negotiations. Add ‘AES-128-CBC’ to —data-ciphers or change —cipher ‘AES-128-CBC’ to —data-ciphers-fallback ‘AES-128-CBC’ to silence this warning.
Options error: —ca fails with ‘ca.crt’: No such file or directory (errno=2)
Options error: —cert fails with ‘client.crt’: No such file or directory (errno=2)
2021-02-23 09:35:59 us=884706 WARNING: cannot stat file ‘client.key’: No such file or directory (errno=2)
Options error: —key fails with ‘client.key’: No such file or directory (errno=2)
Options error: Please correct these errors.
Use —help for more information.
Was this post helpful?
thumb_up
thumb_down
OP
RDB001
This person is a verified professional.
Verify your account
to enable IT peers to see that you are a professional.
jalapeno
Additionally,
The config files are in the directory of:
C:Program filesOpenVPNconfig
Was this post helpful?
thumb_up
thumb_down
OP
RDB001
This person is a verified professional.
Verify your account
to enable IT peers to see that you are a professional.
jalapeno
Which in turns gives this result:
Was this post helpful?
thumb_up
thumb_down
OP
RDB001
This person is a verified professional.
Verify your account
to enable IT peers to see that you are a professional.
jalapeno
The client.opvn extension file:
client
dev tap
proto udp
dev-node NETGEAR-VPN
remote x.x.x.x (MY IP) 12974
resolv-retry infinite
nobind
persist-key
persist-tun
ca ca.crt
cert client.crt
key client.key
cipher AES-128-CBC
comp-lzo
verb 5
Was this post helpful?
thumb_up
thumb_down
Try just changing «tap» to «tun» and update the port number in the «remote» line from 12974 to the TUN port shown in your Netgear config.
The other errors about missing files are curious because you are showing those files exist in the same folder. Or did you move the files into there after you showed the error log? The last screenshot tells you to check the client.log file — what does that contain?
1 found this helpful
thumb_up
thumb_down
Have you opened the appropriate ports in the client firewall?
Also, try entering the appropriate path to the certs in the config. Examples (notice the double slashes):
ca «C:\Program Files\OpenVPN\config\ca.crt»
cert «C:\Program Files\OpenVPN\config\MRdesktop.crt»
key «C:\Program Files\OpenVPN\config\MRdesktop.key»
1 found this helpful
thumb_up
thumb_down
OP
RDB001
This person is a verified professional.
Verify your account
to enable IT peers to see that you are a professional.
jalapeno
GerardBeekmans wrote:
Try just changing «tap» to «tun» and update the port number in the «remote» line from 12974 to the TUN port shown in your Netgear config.
The other errors about missing files are curious because you are showing those files exist in the same folder. Or did you move the files into there after you showed the error log? The last screenshot tells you to check the client.log file — what does that contain?
Okay I replaced tap with tun and changed the port to 12973 and I am getting a bit further but am running into a TLS handshake issue.
2021-02-23 11:15:58 WARNING: Compression for receiving enabled. Compression has been used in the past to break encryption. Sent packets are not compressed unless «allow-compression yes» is also set.
2021-02-23 11:15:58 us=108749 DEPRECATED OPTION: —cipher set to ‘AES-128-CBC’ but missing in —data-ciphers (AES-256-GCM:AES-128-GCM). Future OpenVPN version will ignore —cipher for cipher negotiations. Add ‘AES-128-CBC’ to —data-ciphers or change —cipher ‘AES-128-CBC’ to —data-ciphers-fallback ‘AES-128-CBC’ to silence this warning.
2021-02-23 11:15:58 us=109744 Current Parameter Settings:
2021-02-23 11:15:58 us=109744 config = ‘client.ovpn’
2021-02-23 11:15:58 us=109744 mode = 0
2021-02-23 11:15:58 us=109744 show_ciphers = DISABLED
2021-02-23 11:15:58 us=109744 show_digests = DISABLED
2021-02-23 11:15:58 us=109744 show_engines = DISABLED
2021-02-23 11:15:58 us=109744 genkey = DISABLED
2021-02-23 11:15:58 us=109744 genkey_filename = ‘[UNDEF]’
2021-02-23 11:15:58 us=109744 key_pass_file = ‘[UNDEF]’
2021-02-23 11:15:58 us=109744 show_tls_ciphers = DISABLED
2021-02-23 11:15:58 us=109744 connect_retry_max = 0
2021-02-23 11:15:58 us=109744 Connection profiles [0]:
2021-02-23 11:15:58 us=109744 proto = udp
2021-02-23 11:15:58 us=109744 local = ‘[UNDEF]’
2021-02-23 11:15:58 us=109744 local_port = ‘[UNDEF]’
2021-02-23 11:15:58 us=109744 remote = ‘MYIP’
2021-02-23 11:15:58 us=109744 remote_port = ‘12973’
2021-02-23 11:15:58 us=109744 remote_float = DISABLED
2021-02-23 11:15:58 us=109744 bind_defined = DISABLED
2021-02-23 11:15:58 us=109744 bind_local = DISABLED
2021-02-23 11:15:58 us=109744 bind_ipv6_only = DISABLED
2021-02-23 11:15:58 us=109744 connect_retry_seconds = 5
2021-02-23 11:15:58 us=109744 connect_timeout = 120
2021-02-23 11:15:58 us=109744 socks_proxy_server = ‘[UNDEF]’
2021-02-23 11:15:58 us=109744 socks_proxy_port = ‘[UNDEF]’
2021-02-23 11:15:58 us=109744 tun_mtu = 1500
2021-02-23 11:15:58 us=109744 tun_mtu_defined = ENABLED
2021-02-23 11:15:58 us=109744 link_mtu = 1500
2021-02-23 11:15:58 us=109744 link_mtu_defined = DISABLED
2021-02-23 11:15:58 us=109744 tun_mtu_extra = 0
2021-02-23 11:15:58 us=109744 tun_mtu_extra_defined = DISABLED
2021-02-23 11:15:58 us=109744 mtu_discover_type = -1
2021-02-23 11:15:58 us=109744 fragment = 0
2021-02-23 11:15:58 us=109744 mssfix = 1450
2021-02-23 11:15:58 us=109744 explicit_exit_notification = 0
2021-02-23 11:15:58 us=109744 tls_auth_file = ‘[UNDEF]’
2021-02-23 11:15:58 us=109744 key_direction = not set
2021-02-23 11:15:58 us=109744 tls_crypt_file = ‘[UNDEF]’
2021-02-23 11:15:58 us=109744 tls_crypt_v2_file = ‘[UNDEF]’
2021-02-23 11:15:58 us=109744 Connection profiles END
2021-02-23 11:15:58 us=109744 remote_random = DISABLED
2021-02-23 11:15:58 us=109744 ipchange = ‘[UNDEF]’
2021-02-23 11:15:58 us=109744 dev = ‘tun’
2021-02-23 11:15:58 us=109744 dev_type = ‘[UNDEF]’
2021-02-23 11:15:58 us=109744 dev_node = ‘NETGEAR-VPN’
2021-02-23 11:15:58 us=109744 lladdr = ‘[UNDEF]’
2021-02-23 11:15:58 us=109744 topology = 1
2021-02-23 11:15:58 us=109744 ifconfig_local = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 ifconfig_remote_netmask = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 ifconfig_noexec = DISABLED
2021-02-23 11:15:58 us=110741 ifconfig_nowarn = DISABLED
2021-02-23 11:15:58 us=110741 ifconfig_ipv6_local = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 ifconfig_ipv6_netbits = 0
2021-02-23 11:15:58 us=110741 ifconfig_ipv6_remote = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 shaper = 0
2021-02-23 11:15:58 us=110741 mtu_test = 0
2021-02-23 11:15:58 us=110741 mlock = DISABLED
2021-02-23 11:15:58 us=110741 keepalive_ping = 0
2021-02-23 11:15:58 us=110741 keepalive_timeout = 0
2021-02-23 11:15:58 us=110741 inactivity_timeout = 0
2021-02-23 11:15:58 us=110741 ping_send_timeout = 0
2021-02-23 11:15:58 us=110741 ping_rec_timeout = 0
2021-02-23 11:15:58 us=110741 ping_rec_timeout_action = 0
2021-02-23 11:15:58 us=110741 ping_timer_remote = DISABLED
2021-02-23 11:15:58 us=110741 remap_sigusr1 = 0
2021-02-23 11:15:58 us=110741 persist_tun = ENABLED
2021-02-23 11:15:58 us=110741 persist_local_ip = DISABLED
2021-02-23 11:15:58 us=110741 persist_remote_ip = DISABLED
2021-02-23 11:15:58 us=110741 persist_key = ENABLED
2021-02-23 11:15:58 us=110741 passtos = DISABLED
2021-02-23 11:15:58 us=110741 resolve_retry_seconds = 1000000000
2021-02-23 11:15:58 us=110741 resolve_in_advance = DISABLED
2021-02-23 11:15:58 us=110741 username = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 groupname = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 chroot_dir = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 cd_dir = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 writepid = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 up_script = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 down_script = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 down_pre = DISABLED
2021-02-23 11:15:58 us=110741 up_restart = DISABLED
2021-02-23 11:15:58 us=110741 up_delay = DISABLED
2021-02-23 11:15:58 us=110741 daemon = DISABLED
2021-02-23 11:15:58 us=110741 inetd = 0
2021-02-23 11:15:58 us=110741 log = ENABLED
2021-02-23 11:15:58 us=110741 suppress_timestamps = DISABLED
2021-02-23 11:15:58 us=110741 machine_readable_output = DISABLED
2021-02-23 11:15:58 us=110741 nice = 0
2021-02-23 11:15:58 us=110741 verbosity = 5
2021-02-23 11:15:58 us=110741 mute = 0
2021-02-23 11:15:58 us=110741 gremlin = 0
2021-02-23 11:15:58 us=110741 status_file = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 status_file_version = 1
2021-02-23 11:15:58 us=110741 status_file_update_freq = 60
2021-02-23 11:15:58 us=110741 occ = ENABLED
2021-02-23 11:15:58 us=110741 rcvbuf = 0
2021-02-23 11:15:58 us=110741 sndbuf = 0
2021-02-23 11:15:58 us=110741 sockflags = 0
2021-02-23 11:15:58 us=110741 fast_io = DISABLED
2021-02-23 11:15:58 us=110741 comp.alg = 2
2021-02-23 11:15:58 us=110741 comp.flags = 1
2021-02-23 11:15:58 us=110741 route_script = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 route_default_gateway = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 route_default_metric = 0
2021-02-23 11:15:58 us=110741 route_noexec = DISABLED
2021-02-23 11:15:58 us=110741 route_delay = 5
2021-02-23 11:15:58 us=110741 route_delay_window = 30
2021-02-23 11:15:58 us=110741 route_delay_defined = ENABLED
2021-02-23 11:15:58 us=110741 route_nopull = DISABLED
2021-02-23 11:15:58 us=110741 route_gateway_via_dhcp = DISABLED
2021-02-23 11:15:58 us=110741 allow_pull_fqdn = DISABLED
2021-02-23 11:15:58 us=110741 Pull filters:
2021-02-23 11:15:58 us=110741 ignore «route-method»
2021-02-23 11:15:58 us=110741 management_addr = ‘127.0.0.1’
2021-02-23 11:15:58 us=110741 management_port = ‘25340’
2021-02-23 11:15:58 us=110741 management_user_pass = ‘stdin’
2021-02-23 11:15:58 us=110741 management_log_history_cache = 250
2021-02-23 11:15:58 us=110741 management_echo_buffer_size = 100
2021-02-23 11:15:58 us=110741 management_write_peer_info_file = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 management_client_user = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 management_client_group = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 management_flags = 6
2021-02-23 11:15:58 us=110741 shared_secret_file = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 key_direction = not set
2021-02-23 11:15:58 us=110741 ciphername = ‘AES-128-CBC’
2021-02-23 11:15:58 us=110741 ncp_enabled = ENABLED
2021-02-23 11:15:58 us=110741 ncp_ciphers = ‘AES-256-GCM:AES-128-GCM:AES-128-CBC’
2021-02-23 11:15:58 us=110741 authname = ‘SHA1’
2021-02-23 11:15:58 us=110741 prng_hash = ‘SHA1’
2021-02-23 11:15:58 us=110741 prng_nonce_secret_len = 16
2021-02-23 11:15:58 us=110741 keysize = 0
2021-02-23 11:15:58 us=110741 engine = DISABLED
2021-02-23 11:15:58 us=110741 replay = ENABLED
2021-02-23 11:15:58 us=110741 mute_replay_warnings = DISABLED
2021-02-23 11:15:58 us=110741 replay_window = 64
2021-02-23 11:15:58 us=110741 replay_time = 15
2021-02-23 11:15:58 us=110741 packet_id_file = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 test_crypto = DISABLED
2021-02-23 11:15:58 us=110741 tls_server = DISABLED
2021-02-23 11:15:58 us=110741 tls_client = ENABLED
2021-02-23 11:15:58 us=110741 ca_file = ‘ca.crt’
2021-02-23 11:15:58 us=110741 ca_path = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 dh_file = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 cert_file = ‘client.crt’
2021-02-23 11:15:58 us=110741 extra_certs_file = ‘[UNDEF]’
2021-02-23 11:15:58 us=110741 priv_key_file = ‘client.key’
2021-02-23 11:15:58 us=110741 pkcs12_file = ‘[UNDEF]’
2021-02-23 11:15:58 us=111738 cryptoapi_cert = ‘[UNDEF]’
2021-02-23 11:15:58 us=111738 cipher_list = ‘[UNDEF]’
2021-02-23 11:15:58 us=111738 cipher_list_tls13 = ‘[UNDEF]’
2021-02-23 11:15:58 us=111738 tls_cert_profile = ‘[UNDEF]’
2021-02-23 11:15:58 us=111738 tls_verify = ‘[UNDEF]’
2021-02-23 11:15:58 us=111738 tls_export_cert = ‘[UNDEF]’
2021-02-23 11:15:58 us=111738 verify_x509_type = 0
2021-02-23 11:15:58 us=111738 verify_x509_name = ‘[UNDEF]’
2021-02-23 11:15:58 us=111738 crl_file = ‘[UNDEF]’
2021-02-23 11:15:58 us=111738 ns_cert_type = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_ku[i] = 0
2021-02-23 11:15:58 us=111738 remote_cert_eku = ‘[UNDEF]’
2021-02-23 11:15:58 us=111738 ssl_flags = 0
2021-02-23 11:15:58 us=111738 tls_timeout = 2
2021-02-23 11:15:58 us=111738 renegotiate_bytes = -1
2021-02-23 11:15:58 us=111738 renegotiate_packets = 0
2021-02-23 11:15:58 us=111738 renegotiate_seconds = 3600
2021-02-23 11:15:58 us=111738 handshake_window = 60
2021-02-23 11:15:58 us=111738 transition_window = 3600
2021-02-23 11:15:58 us=111738 single_session = DISABLED
2021-02-23 11:15:58 us=111738 push_peer_info = DISABLED
2021-02-23 11:15:58 us=111738 tls_exit = DISABLED
2021-02-23 11:15:58 us=111738 tls_crypt_v2_metadata = ‘[UNDEF]’
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_protected_authentication = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_private_mode = 00000000
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_cert_private = DISABLED
2021-02-23 11:15:58 us=111738 pkcs11_pin_cache_period = -1
2021-02-23 11:15:58 us=111738 pkcs11_id = ‘[UNDEF]’
2021-02-23 11:15:58 us=111738 pkcs11_id_management = DISABLED
2021-02-23 11:15:58 us=111738 server_network = 0.0.0.0
2021-02-23 11:15:58 us=111738 server_netmask = 0.0.0.0
2021-02-23 11:15:58 us=111738 server_network_ipv6 = ::
2021-02-23 11:15:58 us=111738 server_netbits_ipv6 = 0
2021-02-23 11:15:58 us=111738 server_bridge_ip = 0.0.0.0
2021-02-23 11:15:58 us=111738 server_bridge_netmask = 0.0.0.0
2021-02-23 11:15:58 us=111738 server_bridge_pool_start = 0.0.0.0
2021-02-23 11:15:58 us=111738 server_bridge_pool_end = 0.0.0.0
2021-02-23 11:15:58 us=111738 ifconfig_pool_defined = DISABLED
2021-02-23 11:15:58 us=111738 ifconfig_pool_start = 0.0.0.0
2021-02-23 11:15:58 us=111738 ifconfig_pool_end = 0.0.0.0
2021-02-23 11:15:58 us=112736 ifconfig_pool_netmask = 0.0.0.0
2021-02-23 11:15:58 us=112736 ifconfig_pool_persist_filename = ‘[UNDEF]’
2021-02-23 11:15:58 us=112736 ifconfig_pool_persist_refresh_freq = 600
2021-02-23 11:15:58 us=112736 ifconfig_ipv6_pool_defined = DISABLED
2021-02-23 11:15:58 us=112736 ifconfig_ipv6_pool_base = ::
2021-02-23 11:15:58 us=112736 ifconfig_ipv6_pool_netbits = 0
2021-02-23 11:15:58 us=112736 n_bcast_buf = 256
2021-02-23 11:15:58 us=112736 tcp_queue_limit = 64
2021-02-23 11:15:58 us=112736 real_hash_size = 256
2021-02-23 11:15:58 us=112736 virtual_hash_size = 256
2021-02-23 11:15:58 us=112736 client_connect_script = ‘[UNDEF]’
2021-02-23 11:15:58 us=112736 learn_address_script = ‘[UNDEF]’
2021-02-23 11:15:58 us=112736 client_disconnect_script = ‘[UNDEF]’
2021-02-23 11:15:58 us=112736 client_config_dir = ‘[UNDEF]’
2021-02-23 11:15:58 us=112736 ccd_exclusive = DISABLED
2021-02-23 11:15:58 us=112736 tmp_dir = ‘C:UsersitAppDataLocalTemp’
2021-02-23 11:15:58 us=112736 push_ifconfig_defined = DISABLED
2021-02-23 11:15:58 us=112736 push_ifconfig_local = 0.0.0.0
2021-02-23 11:15:58 us=112736 push_ifconfig_remote_netmask = 0.0.0.0
2021-02-23 11:15:58 us=112736 push_ifconfig_ipv6_defined = DISABLED
2021-02-23 11:15:58 us=112736 push_ifconfig_ipv6_local = ::/0
2021-02-23 11:15:58 us=112736 push_ifconfig_ipv6_remote = ::
2021-02-23 11:15:58 us=112736 enable_c2c = DISABLED
2021-02-23 11:15:58 us=112736 duplicate_cn = DISABLED
2021-02-23 11:15:58 us=112736 cf_max = 0
2021-02-23 11:15:58 us=112736 cf_per = 0
2021-02-23 11:15:58 us=112736 max_clients = 1024
2021-02-23 11:15:58 us=112736 max_routes_per_client = 256
2021-02-23 11:15:58 us=112736 auth_user_pass_verify_script = ‘[UNDEF]’
2021-02-23 11:15:58 us=112736 auth_user_pass_verify_script_via_file = DISABLED
2021-02-23 11:15:58 us=112736 auth_token_generate = DISABLED
2021-02-23 11:15:58 us=112736 auth_token_lifetime = 0
2021-02-23 11:15:58 us=112736 auth_token_secret_file = ‘[UNDEF]’
2021-02-23 11:15:58 us=112736 vlan_tagging = DISABLED
2021-02-23 11:15:58 us=112736 vlan_accept = all
2021-02-23 11:15:58 us=112736 vlan_pvid = 1
2021-02-23 11:15:58 us=112736 client = ENABLED
2021-02-23 11:15:58 us=112736 pull = ENABLED
2021-02-23 11:15:58 us=112736 auth_user_pass_file = ‘[UNDEF]’
2021-02-23 11:15:58 us=112736 show_net_up = DISABLED
2021-02-23 11:15:58 us=112736 route_method = 3
2021-02-23 11:15:58 us=112736 block_outside_dns = DISABLED
2021-02-23 11:15:58 us=112736 ip_win32_defined = DISABLED
2021-02-23 11:15:58 us=112736 ip_win32_type = 3
2021-02-23 11:15:58 us=112736 dhcp_masq_offset = 0
2021-02-23 11:15:58 us=112736 dhcp_lease_time = 31536000
2021-02-23 11:15:58 us=112736 tap_sleep = 0
2021-02-23 11:15:58 us=112736 dhcp_options = DISABLED
2021-02-23 11:15:58 us=112736 dhcp_renew = DISABLED
2021-02-23 11:15:58 us=112736 dhcp_pre_release = DISABLED
2021-02-23 11:15:58 us=112736 domain = ‘[UNDEF]’
2021-02-23 11:15:58 us=112736 netbios_scope = ‘[UNDEF]’
2021-02-23 11:15:58 us=112736 netbios_node_type = 0
2021-02-23 11:15:58 us=112736 disable_nbt = DISABLED
2021-02-23 11:15:58 us=112736 OpenVPN 2.5.0 x86_64-w64-mingw32 [SSL (OpenSSL)] [LZO] [LZ4] [PKCS11] [AEAD] built on Oct 28 2020
2021-02-23 11:15:58 us=112736 Windows version 10.0 (Windows 10 or greater) 64bit
2021-02-23 11:15:58 us=112736 library versions: OpenSSL 1.1.1h 22 Sep 2020, LZO 2.10
Enter Management Password:
2021-02-23 11:15:58 us=113734 MANAGEMENT: TCP Socket listening on [AF_INET]127.0.0.1:25340
2021-02-23 11:15:58 us=113734 Need hold release from management interface, waiting…
2021-02-23 11:15:58 us=585474 MANAGEMENT: Client connected from [AF_INET]127.0.0.1:25340
2021-02-23 11:15:58 us=696210 MANAGEMENT: CMD ‘state on’
2021-02-23 11:15:58 us=696210 MANAGEMENT: CMD ‘log all on’
2021-02-23 11:15:58 us=875747 MANAGEMENT: CMD ‘echo all on’
2021-02-23 11:15:58 us=877747 MANAGEMENT: CMD ‘bytecount 5’
2021-02-23 11:15:58 us=879737 MANAGEMENT: CMD ‘hold off’
2021-02-23 11:15:58 us=881731 MANAGEMENT: CMD ‘hold release’
2021-02-23 11:15:58 us=881731 WARNING: No server certificate verification method has been enabled. See http://openvpn.net/howto.html#mitm Opens a new window for more info.
2021-02-23 11:15:58 us=884676 LZO compression initializing
2021-02-23 11:15:58 us=884676 Control Channel MTU parms [ L:1622 D:1212 EF:38 EB:0 ET:0 EL:3 ]
2021-02-23 11:15:58 us=884676 Data Channel MTU parms [ L:1622 D:1450 EF:122 EB:406 ET:0 EL:3 ]
2021-02-23 11:15:58 us=884676 Local Options String (VER=V4): ‘V4,dev-type tun,link-mtu 1558,tun-mtu 1500,proto UDPv4,comp-lzo,cipher AES-128-CBC,auth SHA1,keysize 128,key-method 2,tls-client’
2021-02-23 11:15:58 us=884676 Expected Remote Options String (VER=V4): ‘V4,dev-type tun,link-mtu 1558,tun-mtu 1500,proto UDPv4,comp-lzo,cipher AES-128-CBC,auth SHA1,keysize 128,key-method 2,tls-server’
2021-02-23 11:15:58 us=884676 TCP/UDP: Preserving recently used remote address: [AF_INET]MYIP:12973
2021-02-23 11:15:58 us=884676 Socket Buffers: R=[65536->65536] S=[65536->65536]
2021-02-23 11:15:58 us=884676 UDP link local: (not bound)
2021-02-23 11:15:58 us=884676 UDP link remote: [AF_INET]MYIP:12973
2021-02-23 11:15:58 us=884676 MANAGEMENT: >STATE:1614100558,WAIT,,,,,,
Was this post helpful?
thumb_up
thumb_down
I see some warnings in that log but no showstoppers. Last line shows your openvpn client is in a waiting state. Does the Netgear show you anything useful like an incoming connection?
1 found this helpful
thumb_up
thumb_down
Check this link that’s embedded in the log: http://openvpn.net/howto.html#mitm Opens a new window . The How To can answer a lot of questions.
1 found this helpful
thumb_up
thumb_down
OP
RDB001
This person is a verified professional.
Verify your account
to enable IT peers to see that you are a professional.
jalapeno
It now works in V 3.3. Changing the tap to tun and the port number resolved this issue.
Was this post helpful?
thumb_up
thumb_down
Содержание
- OpenVPN Support Forum
- Unrecognized option or missing or extra parameter(s) in data-ciphers (2.4.7)
- Unrecognized option or missing or extra parameter(s) in data-ciphers (2.4.7)
- OpenVPN Support Forum
- Unrecognized or missing parameters error
- Unrecognized or missing parameters error
- OpenVPN Support Forum
- Options error: Unrecognized option or missing or extra parameter(s) in client.ovpn:88: ca (2.5.7)
- Options error: Unrecognized option or missing or extra parameter(s) in client.ovpn:88: ca (2.5.7)
- OpenVPN Support Forum
- Options error: Unrecognized option or missing or extra parameter(s)
- Options error: Unrecognized option or missing or extra parameter(s)
OpenVPN Support Forum
Community Support Forum
Post by jmovpn » Tue Dec 22, 2020 4:12 am
Edit: First off, I just realized this is the wrong forum for this post, but I don’t see how to delete it. so I apologize up front for the incorrect post location.
Hello, so I used the pfSense openVPN wizard to create a VPN server and export a client ovpn file. I can connect just fine on my phone’s OpenVPN client so I know the server is set up okay, but the issue is trying to use the same ovpn profile on my Ubuntu 20.04 laptop.
When I try to connect using the OpenVPN client on Ubuntu, I get this:
I tried Googling this, and it seems like the issue here is that the ovpn profile might be using encryption ciphers that aren’t compatible with OpenVPN version 2.4.7, and that the client export tool in pfSense is using OpenVPN 2.5.0.
However, I’m not smart enough on how to set the server up to be compatible with 2.4.7, or edit the ovpn file to be compatible with 2.4.7. I saw a couple of random forum posts that talked about changing the «data-ciphers» line in the ovpn file to add ciphers that are compatible with 2.4.7, but it didn’t work. I don’t remember the site, and I’ve already deleted the file so I don’t remember exactly what they suggested, but it was something along the lines of «data-ciphers AES-128-CBC:AES-128-GCM»
The ovpn file is below:
I’ve also tried to install 2.5.0 on my laptop, but I’m having several issues with that which I won’t go into detail with unless someone thinks it’ll help. The default openvpn version in the Ubuntu 20.04 repo is 2.4.7, so I’m stuck on this for the time being.
Anyone run into this before or know how to fix this?
Источник
OpenVPN Support Forum
Community Support Forum
Unrecognized or missing parameters error
Unrecognized or missing parameters error
Post by HipNuts » Wed Nov 22, 2017 2:42 pm
Here’s my config text. Been jacking with this for awhile and I’m still not sure whats wrong. Any help would be appreciated
##############################################
# Sample client-side OpenVPN 2.0 config file #
# for connecting to multi-client server. #
# #
# This configuration can be used by multiple #
# clients, however each client should have #
# its own cert and key files. #
# #
# On Windows, you might want to rename this #
# file so it has a .ovpn extension #
##############################################
# Specify that we are a client and that we
# will be pulling certain config file directives
# from the server.
client
# Use the same setting as you are using on
# the server.
# On most systems, the VPN will not function
# unless you partially or fully disable
# the firewall for the TUN/TAP interface.
;dev tap
dev tun
# Windows needs the TAP-Win32 adapter name
# from the Network Connections panel
# if you have more than one. On XP SP2,
# you may need to disable the firewall
# for the TAP adapter.
;dev-node MyTap
# Are we connecting to a TCP or
# UDP server? Use the same setting as
# on the server.
;proto tcp
proto udp
# The hostname/IP and port of the server.
# You can have multiple remote entries
# to load balance between the servers.
remote 104.190.204.139 1194
;remote my-server-2 1194
# Choose a random host from the remote
# list for load-balancing. Otherwise
# try hosts in the order specified.
;remote-random
# Keep trying indefinitely to resolve the
# host name of the OpenVPN server. Very useful
# on machines which are not permanently connected
# to the internet such as laptops.
resolv-retry infinite
# Most clients don’t need to bind to
# a specific local port number.
nobind
# Downgrade privileges after initialization (non-Windows only)
;user nobody
;group nobody
# Try to preserve some state across restarts.
persist-key
persist-tun
# If you are connecting through an
# HTTP proxy to reach the actual OpenVPN
# server, put the proxy server/IP and
# port number here. See the man page
# if your proxy server requires
# authentication.
;http-proxy-retry # retry on connection failures
;http-proxy [proxy server] [proxy port #]
# Wireless networks often produce a lot
# of duplicate packets. Set this flag
# to silence duplicate packet warnings.
;mute-replay-warnings
# SSL/TLS parms.
# See the server config file for more
# description. It’s best to use
# a separate .crt/.key file pair
# for each client. A single ca
# file can be used for all clients.
ca c:\Program Files/OpenVPN/config/ca.crt
cert c:\Program Files/OpenVPN/config/townsen01.crt
key c:\Program Files/OpenVPN/config/townsen01.key
# Verify server certificate by checking
# that the certicate has the nsCertType
# field set to «server». This is an
# important precaution to protect against
# a potential attack discussed here:
# http://openvpn.net/howto.html#mitm
#
# To use this feature, you will need to generate
# your server certificates with the nsCertType
# field set to «server». The build-key-server
# script in the easy-rsa folder will do this.
ns-cert-type server
# If a tls-auth key is used on the server
# then every client must also have the key.
;tls-auth ta.key 1
# Select a cryptographic cipher.
# If the cipher option is used on the server
# then you must also specify it here.
cipher AES-256-CBC
# Enable compression on the VPN link.
# Don’t enable this unless it is also
# enabled in the server config file.
;comp-lzo
# Set log file verbosity.
verb 3
# Silence repeating messages
;mute 20
Источник
OpenVPN Support Forum
Community Support Forum
Options error: Unrecognized option or missing or extra parameter(s) in client.ovpn:88: ca (2.5.7)
Options error: Unrecognized option or missing or extra parameter(s) in client.ovpn:88: ca (2.5.7)
Post by TeddyBear6264 » Sun Jul 03, 2022 10:34 pm
Hello, I am trying to set up a VPN on my Personal PC using OVPN and have been following this guide :
I got stuck at Part 5B,
After i Edited the client config on the Client PC, and tired to connect, errors that i cannot make sense of occurs, i have followed everything correctly
I am attaching images of the error, the client log and the client config itself.
it says there are unrecognizes or missing or extra params but there is nothing there and im very confused as to where the issue is.
(if you cant see the images, right click and open them in a new tab please)
Client Config :
##############################################
# Sample client-side OpenVPN 2.0 config file #
# for connecting to multi-client server. #
# #
# This configuration can be used by multiple #
# clients, however each client should have #
# its own cert and key files. #
# #
# On Windows, you might want to rename this #
# file so it has a .ovpn extension #
##############################################
# Specify that we are a client and that we
# will be pulling certain config file directives
# from the server.
client
# Use the same setting as you are using on
# the server.
# On most systems, the VPN will not function
# unless you partially or fully disable
# the firewall for the TUN/TAP interface.
;dev tap
dev tun
# Windows needs the TAP-Win32 adapter name
# from the Network Connections panel
# if you have more than one. On XP SP2,
# you may need to disable the firewall
# for the TAP adapter.
;dev-node MyTap
# Are we connecting to a TCP or
# UDP server? Use the same setting as
# on the server.
;proto tcp
proto udp
# The hostname/IP and port of the server.
# You can have multiple remote entries
# to load balance between the servers.
remote 185.210.137.214 1194
;remote my-server-2 1194
# Choose a random host from the remote
# list for load-balancing. Otherwise
# try hosts in the order specified.
;remote-random
# Keep trying indefinitely to resolve the
# host name of the OpenVPN server. Very useful
# on machines which are not permanently connected
# to the internet such as laptops.
resolv-retry infinite
# Most clients don’t need to bind to
# a specific local port number.
nobind
# Downgrade privileges after initialization (non-Windows only)
;user nobody
;group nobody
# Try to preserve some state across restarts.
persist-key
persist-tun
# If you are connecting through an
# HTTP proxy to reach the actual OpenVPN
# server, put the proxy server/IP and
# port number here. See the man page
# if your proxy server requires
# authentication.
;http-proxy-retry # retry on connection failures
;http-proxy [proxy server] [proxy port #]
# Wireless networks often produce a lot
# of duplicate packets. Set this flag
# to silence duplicate packet warnings.
;mute-replay-warnings
# SSL/TLS parms.
# See the server config file for more
# description. It’s best to use
# a separate .crt/.key file pair
# for each client. A single ca
# file can be used for all clients.
ca “C:\Program Files\OpenVPN\config\ca.crt”
cert “C:\Program Files\OpenVPN\config\CLIENT.crt”
key “C:\Program Files\OpenVPN\config\CLIENT.key”
# Verify server certificate by checking that the
# certificate has the correct key usage set.
# This is an important precaution to protect against
# a potential attack discussed here:
# http://openvpn.net/howto.html#mitm
#
# To use this feature, you will need to generate
# your server certificates with the keyUsage set to
# digitalSignature, keyEncipherment
# and the extendedKeyUsage to
# serverAuth
# EasyRSA can do this for you.
remote-cert-tls server
# If a tls-auth key is used on the server
# then every client must also have the key.
tls-auth “C:\Program Files\OpenVPN\config\tls-auth.key” 1
# Select a cryptographic cipher.
# If the cipher option is used on the server
# then you must also specify it here.
# Note that v2.4 client/server will automatically
# negotiate AES-256-GCM in TLS mode.
# See also the data-ciphers option in the manpage
cipher AES-256-CBC
# Enable compression on the VPN link.
# Don’t enable this unless it is also
# enabled in the server config file.
#comp-lzo
# Set log file verbosity.
verb 3
# Silence repeating messages
;mute 20
Can someone help me find the issue and resort this?
Источник
OpenVPN Support Forum
Community Support Forum
Options error: Unrecognized option or missing or extra parameter(s)
Options error: Unrecognized option or missing or extra parameter(s)
Post by net.admin » Mon Oct 02, 2017 1:25 pm
This is my first setup that isn’t point to point and I’m receiving the following error which I can’t seem to find the cause of. This is a test on the same network, no routers or firewalls (software included) are in play.
I’m receiving the following error in the log — this is the entire log:
Options error: Unrecognized option or missing or extra parameter(s) in client1.ovpn:10: ca (2.4.4)
Use —help for more information.
Things I’ve tried:
Checked the client / server config’s for obvious error.
Recreate the certificates.
Figure I’m either doing something significantly wrong or missing something. Either way, putting up my hand and asking for a little assistance.
Client on Windows 10:
[oconf=]
client
dev tun
proto udp
remote server-ip 1194
resolv-retry infinite
nobind
persist-key
persist-tun
ca C:\Program Files\OpenVPN\config\ca.crt
cert C:\Program Files\OpenVPN\config\client1.crt
key C:\Program Files\OpenVPN\config\client1.key
tls-auth ta.key 1
verb 6
mute 20
[/oconf]
Server on Windows 7:
[oconf=]
#################################################
# Sample OpenVPN 2.0 config file for #
# multi-client server. #
# #
# This file is for the server side #
# of a many-clients one-server #
# OpenVPN configuration. #
# #
# OpenVPN also supports #
# single-machine single-machine #
# configurations (See the Examples page #
# on the web site for more info). #
# #
# This config should work on Windows #
# or Linux/BSD systems. Remember on #
# Windows to quote pathnames and use #
# double backslashes, e.g.: #
# «C:\Program Files\OpenVPN\config\foo.key» #
# #
# Comments are preceded with ‘#’ or ‘;’ #
#################################################
# Which local IP address should OpenVPN
# listen on? (optional)
;local a.b.c.d
# Which TCP/UDP port should OpenVPN listen on?
# If you want to run multiple OpenVPN instances
# on the same machine, use a different port
# number for each one. You will need to
# open up this port on your firewall.
port 1194
# TCP or UDP server?
;proto tcp
proto udp
# «dev tun» will create a routed IP tunnel,
# «dev tap» will create an ethernet tunnel.
# Use «dev tap0» if you are ethernet bridging
# and have precreated a tap0 virtual interface
# and bridged it with your ethernet interface.
# If you want to control access policies
# over the VPN, you must create firewall
# rules for the the TUN/TAP interface.
# On non-Windows systems, you can give
# an explicit unit number, such as tun0.
# On Windows, use «dev-node» for this.
# On most systems, the VPN will not function
# unless you partially or fully disable
# the firewall for the TUN/TAP interface.
;dev tap
dev tun
# Windows needs the TAP-Win32 adapter name
# from the Network Connections panel if you
# have more than one. On XP SP2 or higher,
# you may need to selectively disable the
# Windows firewall for the TAP adapter.
# Non-Windows systems usually don’t need this.
;dev-node MyTap
# SSL/TLS root certificate (ca), certificate
# (cert), and private key (key). Each client
# and the server must have their own cert and
# key file. The server and all clients will
# use the same ca file.
#
# See the «easy-rsa» directory for a series
# of scripts for generating RSA certificates
# and private keys. Remember to use
# a unique Common Name for the server
# and each of the client certificates.
#
# Any X509 key management system can be used.
# OpenVPN can also use a PKCS #12 formatted key file
# (see «pkcs12» directive in man page).
ca «C:\Program Files\OpenVPN\config\ca.crt
cert «C:\Program Files\OpenVPN\config\server.crt
key «C:\Program Files\OpenVPN\config\server.key
# This file should be kept secret
# Diffie hellman parameters.
# Generate your own with:
# openssl dhparam -out dh2048.pem 2048
dh «C:\Program Files\OpenVPN\config\dh4096.pem
# Network topology
# Should be subnet (addressing via IP)
# unless Windows clients v2.0.9 and lower have to
# be supported (then net30, i.e. a /30 per client)
# Defaults to net30 (not recommended)
;topology subnet
# Configure server mode and supply a VPN subnet
# for OpenVPN to draw client addresses from.
# The server will take 10.8.0.1 for itself,
# the rest will be made available to clients.
# Each client will be able to reach the server
# on 10.8.0.1. Comment this line out if you are
# ethernet bridging. See the man page for more info.
server 10.8.0.0 255.255.255.0
# Maintain a record of client virtual IP address
# associations in this file. If OpenVPN goes down or
# is restarted, reconnecting clients can be assigned
# the same virtual IP address from the pool that was
# previously assigned.
ifconfig-pool-persist ipp.txt
# Configure server mode for ethernet bridging.
# You must first use your OS’s bridging capability
# to bridge the TAP interface with the ethernet
# NIC interface. Then you must manually set the
# IP/netmask on the bridge interface, here we
# assume 10.8.0.4/255.255.255.0. Finally we
# must set aside an IP range in this subnet
# (start=10.8.0.50 end=10.8.0.100) to allocate
# to connecting clients. Leave this line commented
# out unless you are ethernet bridging.
;server-bridge 10.8.0.4 255.255.255.0 10.8.0.50 10.8.0.100
# Configure server mode for ethernet bridging
# using a DHCP-proxy, where clients talk
# to the OpenVPN server-side DHCP server
# to receive their IP address allocation
# and DNS server addresses. You must first use
# your OS’s bridging capability to bridge the TAP
# interface with the ethernet NIC interface.
# Note: this mode only works on clients (such as
# Windows), where the client-side TAP adapter is
# bound to a DHCP client.
;server-bridge
# Push routes to the client to allow it
# to reach other private subnets behind
# the server. Remember that these
# private subnets will also need
# to know to route the OpenVPN client
# address pool (10.8.0.0/255.255.255.0)
# back to the OpenVPN server.
;push «route 192.168.10.0 255.255.255.0»
;push «route 192.168.20.0 255.255.255.0»
# To assign specific IP addresses to specific
# clients or if a connecting client has a private
# subnet behind it that should also have VPN access,
# use the subdirectory «ccd» for client-specific
# configuration files (see man page for more info).
# EXAMPLE: Suppose the client
# having the certificate common name «Thelonious»
# also has a small subnet behind his connecting
# machine, such as 192.168.40.128/255.255.255.248.
# First, uncomment out these lines:
;client-config-dir ccd
;route 192.168.40.128 255.255.255.248
# Then create a file ccd/Thelonious with this line:
# iroute 192.168.40.128 255.255.255.248
# This will allow Thelonious’ private subnet to
# access the VPN. This example will only work
# if you are routing, not bridging, i.e. you are
# using «dev tun» and «server» directives.
# EXAMPLE: Suppose you want to give
# Thelonious a fixed VPN IP address of 10.9.0.1.
# First uncomment out these lines:
;client-config-dir ccd
;route 10.9.0.0 255.255.255.252
# Then add this line to ccd/Thelonious:
# ifconfig-push 10.9.0.1 10.9.0.2
# Suppose that you want to enable different
# firewall access policies for different groups
# of clients. There are two methods:
# (1) Run multiple OpenVPN daemons, one for each
# group, and firewall the TUN/TAP interface
# for each group/daemon appropriately.
# (2) (Advanced) Create a script to dynamically
# modify the firewall in response to access
# from different clients. See man
# page for more info on learn-address script.
;learn-address ./script
# If enabled, this directive will configure
# all clients to redirect their default
# network gateway through the VPN, causing
# all IP traffic such as web browsing and
# and DNS lookups to go through the VPN
# (The OpenVPN server machine may need to NAT
# or bridge the TUN/TAP interface to the internet
# in order for this to work properly).
;push «redirect-gateway def1 bypass-dhcp»
# Certain Windows-specific network settings
# can be pushed to clients, such as DNS
# or WINS server addresses. CAVEAT:
# http://openvpn.net/faq.html#dhcpcaveats
# The addresses below refer to the public
# DNS servers provided by opendns.com.
;push «dhcp-option DNS 208.67.222.222»
;push «dhcp-option DNS 208.67.220.220»
# Uncomment this directive to allow different
# clients to be able to «see» each other.
# By default, clients will only see the server.
# To force clients to only see the server, you
# will also need to appropriately firewall the
# server’s TUN/TAP interface.
;client-to-client
# Uncomment this directive if multiple clients
# might connect with the same certificate/key
# files or common names. This is recommended
# only for testing purposes. For production use,
# each client should have its own certificate/key
# pair.
#
# IF YOU HAVE NOT GENERATED INDIVIDUAL
# CERTIFICATE/KEY PAIRS FOR EACH CLIENT,
# EACH HAVING ITS OWN UNIQUE «COMMON NAME»,
# UNCOMMENT THIS LINE OUT.
;duplicate-cn
# The keepalive directive causes ping-like
# messages to be sent back and forth over
# the link so that each side knows when
# the other side has gone down.
# Ping every 10 seconds, assume that remote
# peer is down if no ping received during
# a 120 second time period.
keepalive 10 120
# For extra security beyond that provided
# by SSL/TLS, create an «HMAC firewall»
# to help block DoS attacks and UDP port flooding.
#
# Generate with:
# openvpn —genkey —secret ta.key
#
# The server and each client must have
# a copy of this key.
# The second parameter should be ‘0’
# on the server and ‘1’ on the clients.
tls-auth ta.key 0
# This file is secret
# Select a cryptographic cipher.
# This config item must be copied to
# the client config file as well.
# Note that v2.4 client/server will automatically
# negotiate AES-256-GCM in TLS mode.
# See also the ncp-cipher option in the manpage
cipher AES-256-CBC
# Enable compression on the VPN link and push the
# option to the client (v2.4+ only, for earlier
# versions see below)
;compress lz4-v2
;push «compress lz4-v2»
# For compression compatible with older clients use comp-lzo
# If you enable it here, you must also
# enable it in the client config file.
;comp-lzo
# The maximum number of concurrently connected
# clients we want to allow.
;max-clients 100
# It’s a good idea to reduce the OpenVPN
# daemon’s privileges after initialization.
#
# You can uncomment this out on
# non-Windows systems.
;user nobody
;group nobody
# The persist options will try to avoid
# accessing certain resources on restart
# that may no longer be accessible because
# of the privilege downgrade.
persist-key
persist-tun
# Output a short status file showing
# current connections, truncated
# and rewritten every minute.
status openvpn-status.log
# By default, log messages will go to the syslog (or
# on Windows, if running as a service, they will go to
# the «Program FilesOpenVPNlog» directory).
# Use log or log-append to override this default.
# «log» will truncate the log file on OpenVPN startup,
# while «log-append» will append to it. Use one
# or the other (but not both).
;log openvpn.log
;log-append openvpn.log
# Set the appropriate level of log
# file verbosity.
#
# 0 is silent, except for fatal errors
# 4 is reasonable for general usage
# 5 and 6 can help to debug connection problems
# 9 is extremely verbose
verb 6
# Silence repeating messages. At most 20
# sequential messages of the same message
# category will be output to the log.
;mute 20
# Notify the client that when the server restarts so it
# can automatically reconnect.
explicit-exit-notify 1
[/oconf]
Источник