Содержание
- Re: Having trouble with connecting to database via kerberos
- Hyper-V Live Migration — The specified target is unknown or unreachable (0x80090303)
- Thread: GSSAPI / Kerberos Authentication
- GSSAPI / Kerberos Authentication
- Re: GSSAPI / Kerberos Authentication
- Re: GSSAPI / Kerberos Authentication
- Re: GSSAPI / Kerberos Authentication
- Re: GSSAPI / Kerberos Authentication
- Re: GSSAPI / Kerberos Authentication
- Re: GSSAPI / Kerberos Authentication
Re: Having trouble with connecting to database via kerberos
| From: | Dave Page |
|---|---|
| To: | «Haskin, Daniel J» |
| Cc: | «pgadmin-support(at)lists(dot)postgresql(dot)org» |
Subject: Re: Having trouble with connecting to database via kerberos Date: 2020-08-28 10:03:09 Message-ID: CA+OCxozf8nXX-6Loq5q0K=0SBqz0BP6pHZCUUHQCV_tSRUT-ZA@mail.gmail.com Views: Raw Message | Whole Thread | Download mbox | Resend email Thread: Lists: pgadmin-support
On Fri, Aug 28, 2020 at 9:59 AM Haskin, Daniel J wrote:
> Hello!
>
> I wonder if you folks can help me. I am having the hardest time location
> documentation on, or otherwise figuring out how to connect to a
> Kerberos-authenticated database using pgAdmin in Amazon RDS.
>
> I can connect to the database just fine with psql + kinit on linux, but
> the rest of my team is on Windows and pgAdmin.
>
> How, in general, do you connect to a Kerberos-authenticated database from
> pgAdmin on Windows? I haven’t been able to find the answer to this question.
>
> In particular, I am connecting to a 12.3 pgsql database hosted on amazon
> RDS. No matter what I try, whenever I try to auth via Kerberos, I get this
> error:
>
> SSPI continuation error: The specified target is unknown or unreachable
> (80090303)
>
> If I connect using a local pg user, the connection succeeds.
> If I connect using kinit + psql on linux, the connection succeeds.
> If I connect using the correct host endpoint, I get the error above.
> If I connect using the AWS alternative method described here[1] of
> connecting to ., I *still* get the error above.
>
> Is there anyone who can help?
>
> 1:
> https://docs.aws.amazon.com/AmazonRDS/latest/UserGuide/postgresql-kerberos-connecting.html
pgAdmin doesn’t (yet) officially support kerberos authentication. You can
use SSPI if you’re connecting from Windows to a Windows-hosted PostgreSQL
server in a domain or on a the same machine (I actually verified that works
yesterday), or you can in theory use GSSAPI to authenticate to a Linux
hosted server if you’re on a Linux client (I’m working on verifying that at
the moment).
Once I’ve got those scenarios working and verified, I’ll move on to
figuring out how to handle Windows/Mac clients connecting with GSSAPI.
Note that SSPI/GSSAPI will require that you’re running pgAdmin in Desktop
mode. It will not work in Server mode (because the server will typically be
running under a different user account). There’s a feature request for that
in the backlog.
Источник
Hyper-V Live Migration — The specified target is unknown or unreachable (0x80090303)

Полностью текст ошибок выглядит следующим образом:
Невозможно выполнить миграцию виртуальной машины KOM-AD01-PS02 на узел kom-ad01-vm08.holding.com в связи с проблемами несовместимости. The Virtual Machine Management Service failed to authenticate the connection for a Virtual Machine migration at the source host: The specified target is unknown or unreachable (0x80090303).
Невозможно выполнить миграцию виртуальной машины KOM-AD01-PS02 на узел kom-ad01-vm08.holding.com в связи с проблемами несовместимости. The Virtual Machine Management Service failed to establish a connection for a Virtual Machine migration with host ‘kom-ad01-vm08.holding.com’: The specified target is unknown or unreachable (0x80090303).
Корнем проблемы оказалось отсутствие записей SPN связанных с службами роли Hyper-V, которые должны быть зарегистрированы для учетной записи компьютера – хоста виртуализации. Сверка SPN проблемного хоста (в нашем примере это KOM-AD01-VM08 ) с другим штатно функционирующим хостом виртуализации с помощью команды setspn –L показала соответствующий результат
Выполняем регистрацию недостающих записей SPN последовательностью команд:
После это работоспособность механизма миграции виртуальных машин на проблемный хост средствами VMM была восстановлена.
Интересно то, что эта заметка как и предыдущая описывает проблемы возникшие на одном и том же хосте виртуализации. Отличительным обстоятельством процедуры развёртывания этого хоста было то, что роль Hyper-V на этом сервере была включена до того, как сервер был введён в домен, что, как думается, и привело к возникновению описанных проблем.
Источник
Thread: GSSAPI / Kerberos Authentication
GSSAPI / Kerberos Authentication
I am currently trying to configure a Centos6.x – postgresql-9.3 server to authenticate using gssapi. I have several servers I have already configured and are working (a combination of Oracle Linux and Centos, all 6.x series with 9.2,3 or 4). Our company use vas for an interface to Kerberos, The errors I am getting are as follows:
]$ psql -hpglgisprtd001 -dpostgres
psql: GSSAPI continuation error: Unspecified GSS failure.В Minor code may provide more information
GSSAPI continuation error: Server not found in Kerberos database
or from a windows client
C:Userssweingar>psql -hpglgisprtd001.sempra.com -Usweingar
psql: SSPI continuation error: The specified target is unknown or unreachable
I see nothing worthwhile in the postgresql log, nor in /var/log/messages.В I have verified the dns record to my kdc works (or at least I can ping), I am sort of at a loss of where to look next.
Re: GSSAPI / Kerberos Authentication
I am currently trying to configure a Centos6.x – postgresql-9.3 server to authenticate using gssapi. I have several servers I have already configured and are working (a combination of Oracle Linux and Centos, all 6.x series with 9.2,3 or 4). Our company use vas for an interface to Kerberos, The errors I am getting are as follows:
]$ psql -hpglgisprtd001 -dpostgres
psql: GSSAPI continuation error: Unspecified GSS failure.В Minor code may provide more information
GSSAPI continuation error: Server not found in Kerberos database
or from a windows client
psql: SSPI continuation error: The specified target is unknown or unreachable
I see nothing worthwhile in the postgresql log, nor in /var/log/messages.В I have verified the dns record to my kdc works (or at least I can ping), I am sort of at a loss of where to look next.
Re: GSSAPI / Kerberos Authentication
The spn is POSTGRES/, as I set up different servers, the server in the spn changes of course. В The server name resolves, and if I do a klist on the keytab the realm matches.
I am thinking that it has to do with our “vas” & “vasd” systems and how it is configured. But I can’t really say.
From: Bear Giles [mailto:]
Sent: Thursday, June 2, 2016 3:44 PM
To: Weingartner, Steven <>
Cc:
Subject: Re: [ADMIN] GSSAPI / Kerberos Authentication
I was just looking at the Kerberos support. Is your server principal postgres/x.y.z@REALM, where x.y.z is the DNS name for your server? It probably won’t affect you but think it needs to be POSTGRES/x.y.z@REALM for windows networks.
I’ll have to check my notes for more details, e.g., I’m 99% sure it’s ‘postgres’ and not ‘postgresql’.
I know you need to use password authentication from the client — and the username has to be simple (bob@REALM, not bob/postgres@REALM). I’ll be submitting a patch to support a keytab file and compound principals when I have some free time.
On Thu, Jun 2, 2016 at 4:23 PM, Weingartner, Steven wrote:
I am currently trying to configure a Centos6.x – postgresql-9.3 server to authenticate using gssapi. I have several servers I have already configured and are working (a combination of Oracle Linux and Centos, all 6.x series with 9.2,3 or 4). Our company use vas for an interface to Kerberos, The errors I am getting are as follows:
]$ psql -hpglgisprtd001 -dpostgres
psql: GSSAPI continuation error: Unspecified GSS failure.В Minor code may provide more information
GSSAPI continuation error: Server not found in Kerberos database
or from a windows client
psql: SSPI continuation error: The specified target is unknown or unreachable
I see nothing worthwhile in the postgresql log, nor in /var/log/messages.В I have verified the dns record to my kdc works (or at least I can ping), I am sort of at a loss of where to look next.
This email originated outside of Sempra Energy. Be cautious of attachments, web links, or requests for information.
Re: GSSAPI / Kerberos Authentication
The spn is POSTGRES/, as I set up different servers, the server in the spn changes of course.В The server name resolves, and if I do a klist on the keytab the realm matches.
I am thinking that it has to do with our “vas” & “vasd” systems and how it is configured. But I can’t really say.
From: Bear Giles [mailto: ]
Sent: Thursday, June 2, 2016 3:44 PM
To: Weingartner, Steven
Cc:
Subject: Re: [ADMIN] GSSAPI / Kerberos Authentication
I was just looking at the Kerberos support. Is your server principal postgres/x.y.z@REALM, where x.y.z is the DNS name for your server? It probably won’t affect you but think it needs to be POSTGRES/x.y.z@REALM for windows networks.
I’ll have to check my notes for more details, e.g., I’m 99% sure it’s ‘postgres’ and not ‘postgresql’.
I know you need to use password authentication from the client — and the username has to be simple (bob@REALM, not bob/postgres@REALM). I’ll be submitting a patch to support a keytab file and compound principals when I have some free time.
On Thu, Jun 2, 2016 at 4:23 PM, Weingartner, Steven wrote:
I am currently trying to configure a Centos6.x – postgresql-9.3 server to authenticate using gssapi. I have several servers I have already configured and are working (a combination of Oracle Linux and Centos, all 6.x series with 9.2,3 or 4). Our company use vas for an interface to Kerberos, The errors I am getting are as follows:
]$ psql -hpglgisprtd001 -dpostgres
psql: GSSAPI continuation error: Unspecified GSS failure.В Minor code may provide more information
GSSAPI continuation error: Server not found in Kerberos database
or from a windows client
psql: SSPI continuation error: The specified target is unknown or unreachable
I see nothing worthwhile in the postgresql log, nor in /var/log/messages.В I have verified the dns record to my kdc works (or at least I can ping), I am sort of at a loss of where to look next.
This email originated outside of Sempra Energy. Be cautious of attachments, web links, or requests for information.
Re: GSSAPI / Kerberos Authentication
Attachment
Re: GSSAPI / Kerberos Authentication
All,
* Bear Giles ( ) wrote:
> I remember reading comments in the code that case matters — postgres and
> POSTGRES are not the same — but I’m drawing a blank on the rest. I just
> started looking at the code myself though — others probably have more
> experience.
That’s correct, case absolutely matters and it needs to match.
There are options in postgresql.conf to control what’s expected.В This
is a source of common issue when coming from Windows clients to Linux
servers (or the other way around).
In particular, review section 19.3.3 of the 9.5 docs:
For the client side, review krbsrvname:
Check the klist from the client side and also look at the keytab that’s
on the server and what’s in the KDC database and make sure they all
match.В What the client asks for from the KDC needs to be what the KDC
has and what is installed in the keytab on the server for it all to
work.
Источник
Re: GSSAPI / Kerberos Authentication
| From: | «Weingartner, Steven» |
|---|---|
| To: | Bear Giles |
| Cc: | «pgsql-admin(at)postgresql(dot)org» |
Subject: Re: GSSAPI / Kerberos Authentication Date: 2016-06-02 22:49:41 Message-ID: 09818804b4f547eab26ee29fba47932f@MS-EX13RB-P007.corp.SE.sempra.com Views: Raw Message | Whole Thread | Download mbox | Resend email Thread: Lists: pgsql-admin
The spn is POSTGRES/pglgisprtd001(dot)sempra(dot)com(at)CORP(dot)SE(dot)SEMPRA(dot)COM , as I set up different servers, the server in the spn changes of course. The server name resolves, and if I do a klist on the keytab the realm matches.
I am thinking that it has to do with our “vas” & “vasd” systems and how it is configured. But I can’t really say.
From: Bear Giles [mailto:bgiles(at)coyotesong(dot)com]
Sent: Thursday, June 2, 2016 3:44 PM
To: Weingartner, Steven
Cc: pgsql-admin(at)postgresql(dot)org
Subject: Re: [ADMIN] GSSAPI / Kerberos Authentication
I was just looking at the Kerberos support. Is your server principal postgres/x(dot)y(dot)z(at)REALM , where x.y.z is the DNS name for your server? It probably won’t affect you but think it needs to be POSTGRES/x(dot)y(dot)z(at)REALM for windows networks.
I’ll have to check my notes for more details, e.g., I’m 99% sure it’s ‘postgres’ and not ‘postgresql’.
I know you need to use password authentication from the client — and the username has to be simple (bob(at)REALM, not bob/postgres(at)REALM). I’ll be submitting a patch to support a keytab file and compound principals when I have some free time.
On Thu, Jun 2, 2016 at 4:23 PM, Weingartner, Steven > wrote:
I am currently trying to configure a Centos6.x – postgresql-9.3 server to authenticate using gssapi. I have several servers I have already configured and are working (a combination of Oracle Linux and Centos, all 6.x series with 9.2,3 or 4). Our company use vas for an interface to Kerberos, The errors I am getting are as follows:
]$ psql -hpglgisprtd001 -dpostgres
psql: GSSAPI continuation error: Unspecified GSS failure. Minor code may provide more information
GSSAPI continuation error: Server not found in Kerberos database
or from a windows client
C:Userssweingar>psql -hpglgisprtd001.sempra.com -Usweingar
psql: SSPI continuation error: The specified target is unknown or unreachable
(80090303)
I see nothing worthwhile in the postgresql log, nor in /var/log/messages. I have verified the dns record to my kdc works (or at least I can ping), I am sort of at a loss of where to look next.
________________________________
This email originated outside of Sempra Energy. Be cautious of attachments, web links, or requests for information.
Источник
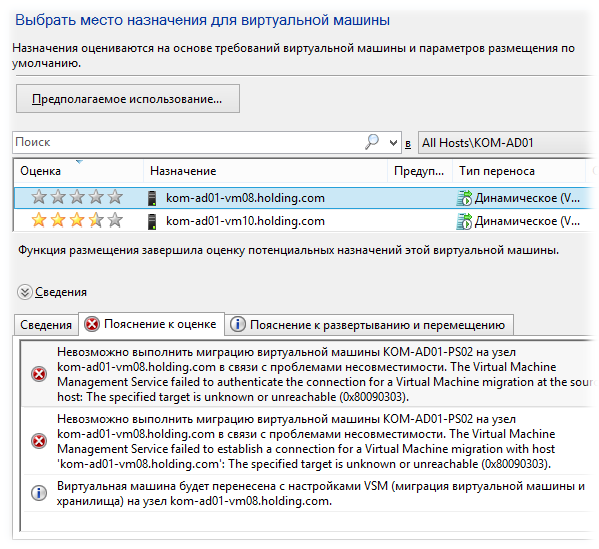
При попытке выполнить миграцию виртуальных машин на новый хост Hyper-V только что добавленный в System Center 2012 R2 Virtual Machine Manager (VMM) возникли ошибки на этапе предварительной проверки хоста на предмет возможности такого переноса. Как следствие мастер миграции VMM не позволял выполнить перенос виртуальных машин на проблемный хост.
Полностью текст ошибок выглядит следующим образом:
Невозможно выполнить миграцию виртуальной машины KOM-AD01-PS02 на узел kom-ad01-vm08.holding.com в связи с проблемами несовместимости. The Virtual Machine Management Service failed to authenticate the connection for a Virtual Machine migration at the source host: The specified target is unknown or unreachable (0x80090303).
Невозможно выполнить миграцию виртуальной машины KOM-AD01-PS02 на узел kom-ad01-vm08.holding.com в связи с проблемами несовместимости. The Virtual Machine Management Service failed to establish a connection for a Virtual Machine migration with host ‘kom-ad01-vm08.holding.com’: The specified target is unknown or unreachable (0x80090303).
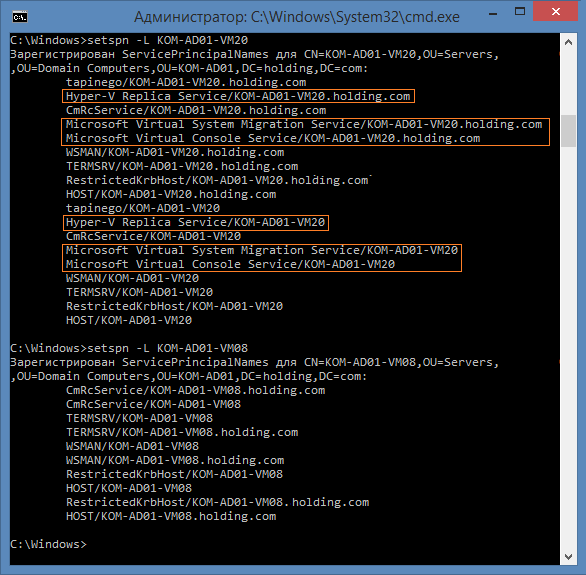
Корнем проблемы оказалось отсутствие записей SPN связанных с службами роли Hyper-V, которые должны быть зарегистрированы для учетной записи компьютера – хоста виртуализации. Сверка SPN проблемного хоста (в нашем примере это KOM-AD01-VM08) с другим штатно функционирующим хостом виртуализации с помощью команды setspn –L показала соответствующий результат
Выполняем регистрацию недостающих записей SPN последовательностью команд:
setspn -S "Hyper-V Replica Service/KOM-AD01-VM08" KOM-AD01-VM08 setspn -S "Hyper-V Replica Service/KOM-AD01-VM08.holding.com" KOM-AD01-VM08 setspn -S "Microsoft Virtual System Migration Service/KOM-AD01-VM08" KOM-AD01-VM08 setspn -S "Microsoft Virtual System Migration Service/KOM-AD01-VM08.holding.com" KOM-AD01-VM08 setspn -S "Microsoft Virtual Console Service/KOM-AD01-VM08" KOM-AD01-VM08 setspn -S "Microsoft Virtual Console Service/KOM-AD01-VM08.holding.com" KOM-AD01-VM08
После это работоспособность механизма миграции виртуальных машин на проблемный хост средствами VMM была восстановлена.
Интересно то, что эта заметка как и предыдущая описывает проблемы возникшие на одном и том же хосте виртуализации. Отличительным обстоятельством процедуры развёртывания этого хоста было то, что роль Hyper-V на этом сервере была включена до того, как сервер был введён в домен, что, как думается, и привело к возникновению описанных проблем.
On Fri, Aug 28, 2020 at 11:03 AM Dave Page <dpage(at)pgadmin(dot)org> wrote:
> Hi
>
> On Fri, Aug 28, 2020 at 9:59 AM Haskin, Daniel J <DHaskin(at)verisk(dot)com>
> wrote:
>
>> Hello!
>>
>> I wonder if you folks can help me. I am having the hardest time location
>> documentation on, or otherwise figuring out how to connect to a
>> Kerberos-authenticated database using pgAdmin in Amazon RDS.
>>
>> I can connect to the database just fine with psql + kinit on linux, but
>> the rest of my team is on Windows and pgAdmin.
>>
>> How, in general, do you connect to a Kerberos-authenticated database from
>> pgAdmin on Windows? I haven’t been able to find the answer to this question.
>>
>> In particular, I am connecting to a 12.3 pgsql database hosted on amazon
>> RDS. No matter what I try, whenever I try to auth via Kerberos, I get this
>> error:
>>
>> SSPI continuation error: The specified target is unknown or unreachable
>> (80090303)
>>
>> If I connect using a local pg user, the connection succeeds.
>> If I connect using kinit + psql on linux, the connection succeeds.
>> If I connect using the correct host endpoint, I get the error above.
>> If I connect using the AWS alternative method described here[1] of
>> connecting to <endpoint>.<aws-ad-domain>, I *still* get the error above.
>>
>> Is there anyone who can help?
>>
>> 1:
>> https://docs.aws.amazon.com/AmazonRDS/latest/UserGuide/postgresql-kerberos-connecting.html
>
>
> pgAdmin doesn’t (yet) officially support kerberos authentication. You can
> use SSPI if you’re connecting from Windows to a Windows-hosted PostgreSQL
> server in a domain or on a the same machine (I actually verified that works
> yesterday), or you can in theory use GSSAPI to authenticate to a Linux
> hosted server if you’re on a Linux client (I’m working on verifying that at
> the moment).
>
> Once I’ve got those scenarios working and verified, I’ll move on to
> figuring out how to handle Windows/Mac clients connecting with GSSAPI.
>
> Note that SSPI/GSSAPI will require that you’re running pgAdmin in Desktop
> mode. It will not work in Server mode (because the server will typically be
> running under a different user account). There’s a feature request for that
> in the backlog.
>
FYI, I’ve also confirmed that Linux — Linux works with GSSAPI.
—
Dave Page
Blog: http://pgsnake.blogspot.com
Twitter: @pgsnake
EDB: http://www.enterprisedb.com
@andrewpong Hi, Andrew. This is my first time using pi_web_api_client to connect the PI-Server.
client = PIWebApiClient(
baseUrl=baseUrl,
useKerberos=True,
username=username,
password=password,
verifySsl=False
)
client.home.get()I also got the GSSError when I tried to connect PI-Server on Windows. I saw your comment said that this error would be received on Windows but it works on MacOS.
May I ask which path should I put the CA on MacOS/Linux when I try to connect PI-Server?GSSError Traceback (most recent call last)
C:ProgramDataAnaconda3libsite-packagesrequests_kerberoskerberos_.py in generate_request_header(self, response, host, is_preemptive)
229 result = kerberos.authGSSClientStep(self.context[host],
—> 230 negotiate_resp_value)
231GSSError: SSPI: InitializeSecurityContext: �����εL�k�F�쪺���w�ؼ�
During handling of the above exception, another exception occurred:
KerberosExchangeError Traceback (most recent call last)
in ()
1 # Get the home infomation of the client
—-> 2 client.home.get()C:ProgramDataAnaconda3libsite-packagesosisoftpidevclubpiwebapiapihome_api.py in get(self, **kwargs)
27 return self.get_with_http_info(**kwargs)
28 else:
—> 29 (data) = self.get_with_http_info(**kwargs)
30 return data
31C:ProgramDataAnaconda3libsite-packagesosisoftpidevclubpiwebapiapihome_api.py in get_with_http_info(self, **kwargs)
80 _preload_content =params.get(‘_preload_content’, True),
81 _request_timeout=params.get(‘_request_timeout’),
—> 82 collection_formats =collection_formats)
83C:ProgramDataAnaconda3libsite-packagesosisoftpidevclubpiwebapiapi_client.py in call_api(self, resource_path, method, path_params, query_params, header_params, body, post_params, files, response_type, callback, _return_http_data_only, collection_formats, _preload_content, _request_timeout)
309 body, post_params, files,
310 response_type, callback,
—> 311 _return_http_data_only, collection_formats, _preload_content, _request_timeout)
312 else:
313 thread = threading.Thread(target=self.__call_api,C:ProgramDataAnaconda3libsite-packagesosisoftpidevclubpiwebapiapi_client.py in __call_api(self, resource_path, method, path_params, query_params, header_params, body, post_params, files, response_type, callback, _return_http_data_only, collection_formats, _preload_content, _request_timeout)
137 query_params=query_params,
138 headers=header_params,
—> 139 body=body)
140
141 return_data = response_dataC:ProgramDataAnaconda3libsite-packagesosisoftpidevclubpiwebapiapi_client.py in request(self, method, url, query_params, headers, body)
327 body=body,
328 query_params=query_params,
—> 329 headers=headers)
330
331C:ProgramDataAnaconda3libsite-packagesosisoftpidevclubpiwebapirest.py in send_request(self, url, method, body, headers, query_params)
55
56 if method == «GET»:
—> 57 response = requests.get(url, auth=self.auth, headers=headers, verify=self.verifySsl)
58 elif method == «HEAD»:
59 response = requests.head(url, auth=self.auth, headers=headers, verify=self.verifySsl)C:ProgramDataAnaconda3libsite-packagesrequestsapi.py in get(url, params, **kwargs)
70
71 kwargs.setdefault(‘allow_redirects’, True)
—> 72 return request(‘get’, url, params=params, **kwargs)
73
74C:ProgramDataAnaconda3libsite-packagesrequestsapi.py in request(method, url, **kwargs)
56 # cases, and look like a memory leak in others.
57 with sessions.Session() as session:
—> 58 return session.request(method=method, url=url, **kwargs)
59
60C:ProgramDataAnaconda3libsite-packagesrequestssessions.py in request(self, method, url, params, data, headers, cookies, files, auth, timeout, allow_redirects, proxies, hooks, stream, verify, cert, json)
496 hooks=hooks,
497 )
—> 498 prep = self.prepare_request(req)
499
500 proxies = proxies or {}C:ProgramDataAnaconda3libsite-packagesrequestssessions.py in prepare_request(self, request)
439 auth=merge_setting(auth, self.auth),
440 cookies=merged_cookies,
—> 441 hooks=merge_hooks(request.hooks, self.hooks),
442 )
443 return pC:ProgramDataAnaconda3libsite-packagesrequestsmodels.py in prepare(self, method, url, headers, files, data, params, auth, cookies, hooks, json)
311 self.prepare_cookies(cookies)
312 self.prepare_body(data, files, json)
—> 313 self.prepare_auth(auth, url)
314
315 # Note that prepare_auth must be last to enable authentication schemesC:ProgramDataAnaconda3libsite-packagesrequestsmodels.py in prepare_auth(self, auth, url)
542
543 # Allow auth to make its changes.
—> 544 r = auth(self)
545
546 # Update self to reflect the auth changes.C:ProgramDataAnaconda3libsite-packagesrequests_kerberoskerberos_.py in call(self, request)
435 host = urlparse(request.url).hostname
436
—> 437 auth_header = self.generate_request_header(None, host, is_preemptive=True)
438
439 log.debug(«HTTPKerberosAuth: Preemptive Authorization header: {0}».format(auth_header))C:ProgramDataAnaconda3libsite-packagesrequests_kerberoskerberos_.py in generate_request_header(self, response, host, is_preemptive)
242 «generate_request_header(): {0} failed:».format(kerb_stage))
243 log.exception(error)
—> 244 raise KerberosExchangeError(«%s failed: %s» % (kerb_stage, str(error.args)))
245
246 except EnvironmentError as error:KerberosExchangeError: authGSSClientStep() failed: (‘SSPI: InitializeSecurityContext: �����εL�k�F�쪺���w�ؼ�rn’,)
Same problem, could you resolve?