Overview of the problem
When using Python to connect to z/OSMF, you might see the following errors:
«certificate verify failed: self signed certificate in certificate chain»
OR
«certificate verify failed: unable to get local issuer certificate»
This might be caused either by server configuration or Python configuration. In this article, we assume you use a self-signed CA certificate in z/OSMF. We will guide you step by step to workaround the certification error. You can choose either workaround if you wish.
- Workaround 1: verify = False
- Workaround 2: verify = CAfile (Specify a certificate in the PARM)
- Workaround 3: verify = True (Update key store in Python)
self signed certificate
If your z/OSMF was configured with self signed certificate, the python3 output error is:
certificate verify failed: self signed certificate in certificate chain
- Workaround 1: verify = False
Setting verify = False will skip SSL certificate verification.
- Workaround 2: verify = CAfile (Specify a certificate in the PARM)
The CAfile must be set to the CA certificate Bundle, if you set it as the server certificate, you will get the above error.
- Workaround 3: Verify = True (Update key store in Python)
The default value for parameter verify is True. Python 3.6+ installer has its own default certificate store for verifying SSL connections. The system certificate store will not be used any more. To use default certificate store, python library certifi must be installed in advance, you can use command «pip3 install certifi» to install it. Python default certificate store was in cacert.pem file, you can get it by
>>> import certifi
>>> certifi.where()
‘/Library/Frameworks/Python.framework/Versions/3.9/lib/python3.9/site-packages/certifi/cacert.pem’
If you get the above error, it means that your CA certificate was not included in cacert.pem, please use below command to add it:
For Mac or Linux:
$ cat [full path of your-cacert.pem] >> [full path of cacert.pem]
For Windows:
C:type [full path of your-cacert.pem] >> [full path of cacert.pem]
CA signed certificate
If your z/OSMF was configured with CA signed certificate, the python3 output error is:
certificate verify failed: unable to get local issuer certificate
- Workaround 1: verify = False
Setting verify = False will skip SSL certificate verification.
- Workaround 2: verify = CAfile (Specify a certificate in the PARM)
The CAfile is a CA certificate Bundle, it must be the Root CA certificate. If it is not a Root CA certificate, the above error will be showed.
- Workaround 3: Verify = True (Update key store in Python)
The default value for parameter verify is True. Python 3.6+ installer has its own default certificate store for verifying SSL connections. The system certificate store will not be used any more. To use default certificate store, python library certifi must be installed in advance, you can use command “pip3 install certifi”to install it. Python default certificate store was in cacert.pem file, you can get it by
>>> import certifi
>>> certifi.where()
‘/Library/Frameworks/Python.framework/Versions/3.9/lib/python3.9/site-packages/certifi/cacert.pem’
If you get the above error, it means that your Root CA certificate was not included in cacert.pem, please use below command to add it:
For Mac or Linux:
$ cat [full path of your-Root-cacert.pem] >> [full path of cacert.pem]
For Windows:
C:type [full path of your-Root-cacert.pem] >> [full path of cacert.pem]
How to export z/OSMF CA certificate
- Export CA certificate from z/OS
1. RACDCERT EXPORT(LABEL(‘zOSMFCA’)) DSN(‘IBMUSER.CACERT.IBMUSER.CRT’) FORMAT(CERTDER) CERTAUTH
Where:
- zOSMF is the label of the CA certificate.
- IBMUSER.CACERT.IBMUSER.CRT is the data set that will contain the client certificate. RACF command will auto-create this dataset
- CERTDER indicates that certificate is in DER format
2. Download the CA certificate from z/OS
3. Convert to PEM format
openssl x509 -in zOSMFCA.crt -inform der -outform pem -out zOSMFCA.pem
Здравствуйте!
Подскажите по OpenVPN
Есть 2 компа на Win 10 (Прости Господи!)
При попытке подключения с одного к другому вылетает такая ошибка:
VERIFY ERROR: depth=1, error=self signed certificate in certificate chain: C=RU, ST=Moscow, L=Moscow, O=Organization, OU=*****.ddns.net, CN=KEYCN, name=KEYNAME, emailAddress=***@***.ru
Конфиг клиента:
client
dev tun
cipher AES-256-CBC
proto tcp
remote ddddd.ddns.net 41416
resolv-retry 30
verb 3
ca ca.crt
cert user1.crt
key user1.key Конфиг сервера:
proto tcp
port 41416
dev tun
dev-node "VPN Server"
dh "C:\Program Files\OpenVPN\ssl\dh1024.pem"
ca "C:\Program Files\OpenVPN\ssl\ca.crt"
cert "C:\Program Files\OpenVPN\ssl\cert.crt"
key "C:\Program Files\OpenVPN\ssl\cert.key"
server 192.168.5.0 255.255.255.0
max-clients 32
keepalive 10 120
client-to-client
mssfix 0
cipher AES-256-CBC
status "C:\Program Files\OpenVPN\log\status.log"
log "C:\Program Files\OpenVPN\log\openvpn.log"
verb 5
mute 5Лог на клиенте:
Sun Nov 26 19:22:05 2017 OpenVPN 2.4.4 x86_64-w64-mingw32 [SSL (OpenSSL)] [LZO] [LZ4] [PKCS11] [AEAD] built on Sep 26 2017
Sun Nov 26 19:22:05 2017 Windows version 6.2 (Windows 8 or greater) 64bit
Sun Nov 26 19:22:05 2017 library versions: OpenSSL 1.0.2l 25 May 2017, LZO 2.10
Enter Management Password:
Sun Nov 26 19:22:05 2017 MANAGEMENT: TCP Socket listening on [AF_INET]127.0.0.1:25340
Sun Nov 26 19:22:05 2017 Need hold release from management interface, waiting...
Sun Nov 26 19:22:06 2017 MANAGEMENT: Client connected from [AF_INET]127.0.0.1:25340
Sun Nov 26 19:22:06 2017 MANAGEMENT: CMD 'state on'
Sun Nov 26 19:22:06 2017 MANAGEMENT: CMD 'log all on'
Sun Nov 26 19:22:06 2017 MANAGEMENT: CMD 'echo all on'
Sun Nov 26 19:22:06 2017 MANAGEMENT: CMD 'hold off'
Sun Nov 26 19:22:06 2017 MANAGEMENT: CMD 'hold release'
Sun Nov 26 19:22:06 2017 WARNING: No server certificate verification method has been enabled. See http://openvpn.net/howto.html#mitm for more info.
Sun Nov 26 19:22:06 2017 MANAGEMENT: >STATE:1511713326,RESOLVE,,,,,,
Sun Nov 26 19:22:06 2017 TCP/UDP: Preserving recently used remote address: [AF_INET]176.112.97.163:41416
Sun Nov 26 19:22:06 2017 Socket Buffers: R=[65536->65536] S=[65536->65536]
Sun Nov 26 19:22:06 2017 Attempting to establish TCP connection with [AF_INET]176.112.97.163:41416 [nonblock]
Sun Nov 26 19:22:06 2017 MANAGEMENT: >STATE:1511713326,TCP_CONNECT,,,,,,
Sun Nov 26 19:22:07 2017 TCP connection established with [AF_INET]176.112.97.163:41416
Sun Nov 26 19:22:07 2017 TCP_CLIENT link local: (not bound)
Sun Nov 26 19:22:07 2017 TCP_CLIENT link remote: [AF_INET]176.112.97.163:41416
Sun Nov 26 19:22:07 2017 MANAGEMENT: >STATE:1511713327,WAIT,,,,,,
Sun Nov 26 19:22:07 2017 MANAGEMENT: >STATE:1511713327,AUTH,,,,,,
Sun Nov 26 19:22:07 2017 TLS: Initial packet from [AF_INET]176.112.97.163:41416, sid=770063ff 0f47046b
Sun Nov 26 19:22:07 2017 VERIFY ERROR: depth=1, error=self signed certificate in certificate chain: C=RU, ST=Moscow, L=Moscow, O=Organization, OU=*****.ddns.net, CN=KEYCN, name=KEYNAME, emailAddress=***@***.ru
Sun Nov 26 19:22:07 2017 OpenSSL: error:14090086:SSL routines:ssl3_get_server_certificate:certificate verify failed
Sun Nov 26 19:22:07 2017 TLS_ERROR: BIO read tls_read_plaintext error
Sun Nov 26 19:22:07 2017 TLS Error: TLS object -> incoming plaintext read error
Sun Nov 26 19:22:07 2017 TLS Error: TLS handshake failed
Sun Nov 26 19:22:07 2017 Fatal TLS error (check_tls_errors_co), restarting
Sun Nov 26 19:22:07 2017 SIGUSR1[soft,tls-error] received, process restarting
Sun Nov 26 19:22:07 2017 MANAGEMENT: >STATE:1511713327,RECONNECTING,tls-error,,,,,
Sun Nov 26 19:22:07 2017 Restart pause, 5 second(s)
Sun Nov 26 19:22:09 2017 SIGTERM[hard,init_instance] received, process exiting
Sun Nov 26 19:22:09 2017 MANAGEMENT: >STATE:1511713329,EXITING,init_instance,,,,,
Лог на сервере:
Sun Nov 26 19:21:02 2017 us=793798 Current Parameter Settings:
Sun Nov 26 19:21:02 2017 us=793798 config = 'C:Program FilesOpenVPNconfigserver.ovpn'
Sun Nov 26 19:21:02 2017 us=793798 mode = 1
Sun Nov 26 19:21:02 2017 us=793798 show_ciphers = DISABLED
Sun Nov 26 19:21:02 2017 us=793798 show_digests = DISABLED
Sun Nov 26 19:21:02 2017 us=793798 NOTE: --mute triggered...
Sun Nov 26 19:21:02 2017 us=793798 291 variation(s) on previous 5 message(s) suppressed by --mute
Sun Nov 26 19:21:02 2017 us=793798 OpenVPN 2.4.4 x86_64-w64-mingw32 [SSL (OpenSSL)] [LZO] [LZ4] [PKCS11] [AEAD] built on Sep 26 2017
Sun Nov 26 19:21:02 2017 us=793798 Windows version 6.2 (Windows 8 or greater) 64bit
Sun Nov 26 19:21:02 2017 us=793798 library versions: OpenSSL 1.0.2l 25 May 2017, LZO 2.10
Sun Nov 26 19:21:02 2017 us=793798 NOTE: your local LAN uses the extremely common subnet address 192.168.0.x or 192.168.1.x. Be aware that this might create routing conflicts if you connect to the VPN server from public locations such as internet cafes that use the same subnet.
Sun Nov 26 19:21:02 2017 us=887552 Diffie-Hellman initialized with 1024 bit key
Sun Nov 26 19:21:02 2017 us=903178 TLS-Auth MTU parms [ L:1623 D:1210 EF:40 EB:0 ET:0 EL:3 ]
Sun Nov 26 19:21:02 2017 us=903178 interactive service msg_channel=0
Sun Nov 26 19:21:02 2017 us=903178 ROUTE_GATEWAY 192.168.0.1/255.255.255.0 I=7 HWADDR=90:2b:34:15:fd:6c
Sun Nov 26 19:21:02 2017 us=903178 open_tun
Sun Nov 26 19:21:02 2017 us=903178 TAP-WIN32 device [VPN Server] opened: \.Global{D07C10C5-1417-4AEF-A456-7B1ACB4CE04F}.tap
Sun Nov 26 19:21:02 2017 us=903178 TAP-Windows Driver Version 9.21
Sun Nov 26 19:21:02 2017 us=903178 TAP-Windows MTU=1500
Sun Nov 26 19:21:02 2017 us=903178 Notified TAP-Windows driver to set a DHCP IP/netmask of 192.168.5.1/255.255.255.252 on interface {D07C10C5-1417-4AEF-A456-7B1ACB4CE04F} [DHCP-serv: 192.168.5.2, lease-time: 31536000]
Sun Nov 26 19:21:02 2017 us=903178 Sleeping for 10 seconds...
Sun Nov 26 19:21:12 2017 us=912500 Successful ARP Flush on interface [9] {D07C10C5-1417-4AEF-A456-7B1ACB4CE04F}
Sun Nov 26 19:21:12 2017 us=912500 do_ifconfig, tt->did_ifconfig_ipv6_setup=0
Sun Nov 26 19:21:12 2017 us=912500 C:WINDOWSsystem32route.exe ADD 192.168.5.0 MASK 255.255.255.0 192.168.5.2
Sun Nov 26 19:21:12 2017 us=912500 ROUTE: CreateIpForwardEntry succeeded with dwForwardMetric1=35 and dwForwardType=4
Sun Nov 26 19:21:12 2017 us=912500 Route addition via IPAPI succeeded [adaptive]
Sun Nov 26 19:21:12 2017 us=912500 Data Channel MTU parms [ L:1623 D:1623 EF:123 EB:406 ET:0 EL:3 ]
Sun Nov 26 19:21:12 2017 us=912500 Could not determine IPv4/IPv6 protocol. Using AF_INET6
Sun Nov 26 19:21:12 2017 us=912500 Socket Buffers: R=[65536->65536] S=[65536->65536]
Sun Nov 26 19:21:12 2017 us=912500 setsockopt(IPV6_V6ONLY=0)
Sun Nov 26 19:21:12 2017 us=912500 Listening for incoming TCP connection on [AF_INET6][undef]:41416
Sun Nov 26 19:21:12 2017 us=912500 TCPv6_SERVER link local (bound): [AF_INET6][undef]:41416
Sun Nov 26 19:21:12 2017 us=912500 TCPv6_SERVER link remote: [AF_UNSPEC]
Sun Nov 26 19:21:12 2017 us=912500 MULTI: multi_init called, r=256 v=256
Sun Nov 26 19:21:12 2017 us=912500 IFCONFIG POOL: base=192.168.5.4 size=62, ipv6=0
Sun Nov 26 19:21:12 2017 us=912500 MULTI: TCP INIT maxclients=32 maxevents=36
Sun Nov 26 19:21:12 2017 us=912500 Initialization Sequence Completed
Sun Nov 26 19:22:07 2017 us=643519 MULTI: multi_create_instance called
Sun Nov 26 19:22:07 2017 us=643519 Re-using SSL/TLS context
Sun Nov 26 19:22:07 2017 us=643519 Control Channel MTU parms [ L:1623 D:1210 EF:40 EB:0 ET:0 EL:3 ]
Sun Nov 26 19:22:07 2017 us=643519 Data Channel MTU parms [ L:1623 D:1623 EF:123 EB:406 ET:0 EL:3 ]
Sun Nov 26 19:22:07 2017 us=643519 Local Options String (VER=V4): 'V4,dev-type tun,link-mtu 1559,tun-mtu 1500,proto TCPv4_SERVER,cipher AES-256-CBC,auth SHA1,keysize 256,key-method 2,tls-server'
Sun Nov 26 19:22:07 2017 us=643519 Expected Remote Options String (VER=V4): 'V4,dev-type tun,link-mtu 1559,tun-mtu 1500,proto TCPv4_CLIENT,cipher AES-256-CBC,auth SHA1,keysize 256,key-method 2,tls-client'
Sun Nov 26 19:22:07 2017 us=643519 TCP connection established with [AF_INET6]::ffff:79.126.13.128:57395
Sun Nov 26 19:22:07 2017 us=643519 TCPv6_SERVER link local: (not bound)
Sun Nov 26 19:22:07 2017 us=643519 TCPv6_SERVER link remote: [AF_INET6]::ffff:79.126.13.128:57395
Sun Nov 26 19:22:08 2017 us=621530 79.126.13.128 TLS: Initial packet from [AF_INET6]::ffff:79.126.13.128:57395, sid=88d68a0a f9b71958
Sun Nov 26 19:22:08 2017 us=919980 79.126.13.128 Connection reset, restarting [0]
Sun Nov 26 19:22:08 2017 us=919980 79.126.13.128 SIGUSR1[soft,connection-reset] received, client-instance restarting
Sun Nov 26 19:22:08 2017 us=919980 TCP/UDP: Closing socket
Да и помогите свернуть код в спойлер, что-то не получилось «cut-/cut»
by Vlad Turiceanu
Passionate about technology, Windows, and everything that has a power button, he spent most of his time developing new skills and learning more about the tech world. Coming… read more
Updated on January 17, 2023
- Since npm stopped automatically accepting self-signed certificates, users have started to report errors while trying to publish some packages in certain applications.
- The error can be fixed, usually, by upgrading the package manager or use the known registrars.
XINSTALL BY CLICKING THE DOWNLOAD FILE
This software will repair common computer errors, protect you from file loss, malware, hardware failure and optimize your PC for maximum performance. Fix PC issues and remove viruses now in 3 easy steps:
- Download Restoro PC Repair Tool that comes with Patented Technologies (patent available here).
- Click Start Scan to find Windows issues that could be causing PC problems.
- Click Repair All to fix issues affecting your computer’s security and performance
- Restoro has been downloaded by 0 readers this month.
For some time now, developers encountered a SELF_SIGNED_CERT_IN_CHAIN error during installing and publishing packages in certain applications and developer tools such as Node.js, npm, or Git.
Until a few years ago, when npm for instance announced that they would no longer support self-signed certificates.
This means that the certificate verification process was no longer automatic. So developers now have to set up their application to see the self-signed certificates.
How do I fix self-signed certificate in the certificate chain?

Depending on the tool you’re using, there are a few recommendations. Some are risky, some are safe. One thing is clear, though: you should not attempt to disable the certification verification process altogether.
For Node.js
You can insert an environment variable to allow untrusted certificates using the following command at the beginning of the code:
process.env['NODE_TLS_REJECT_UNAUTHORIZED'] = 0;This is risky and it’s not recommended to be used in production. Alternatively, use npm config set strict-ssl=false if you have to do this for many applications and you want to save repeating the process.
Users also suggest upgrading your version of Node, to fixes any existing bugs and vulnerabilities.
For npm
The recommended solution is, again, to upgrade your version of npm running one of the following:
npm install npm -g --ca=null
npm update npm -g
Or, tell your current version of npm to use known registrars, and after installing, stop using them:
npm config set ca ""
npm install npm -g
npm config delete caSome users mentioned that they only switched the registry URL from https to http:
npm config set registry="http://registry.npmjs.org/"We hope that one of these suggestions helped you fix the problem. Should you have any recommendations, please use the comments section below.
Newsletter
If you’re using a self-signed certificate on your Bitbucket server, you may receive SSL certificate errors when you try to perform certain actions. This page will help you resolve these errors.
Problem
When trying to perform a clone using instructions stated in Debug logging for Git operations on the client the following error is reported:
$ export GIT_CURL_VERBOSE=1
$ git clone https://username@git.example.com/scm/repository.git
Cloning into 'repository'...
* Couldn't find host git.example.com in the _netrc file; using defaults
* Adding handle: conn: 0x22a7568
* Adding handle: send: 0
* Adding handle: recv: 0
* Curl_addHandleToPipeline: length: 1
* - Conn 0 (0x22a7568) send_pipe: 1, recv_pipe: 0
* About to connect() to git.example.com port 443 (#0)
* Trying 10.253.136.142...
* Connected to git.example.com (10.253.136.142) port 443 (#0)
* successfully set certificate verify locations:
* CAfile: C:Program Files (x86)Git/bin/curl-ca-bundle.crt
CApath: c:/Users/username/Downloads
* SSL certificate problem: self signed certificate in certificate chain
* Closing connection 0
fatal: unable to access 'https://username@git.example.com/scm/repository.git': SSL certificate problem: self signed certificate in certificate chain
Cause
This is caused by git not trusting the certificate provided by your server.
Workaround
One possible workaround is to temporary disable SSL check for your git command in case you only need to perform a one time clone:
GIT_SSL_NO_VERIFY=true git clone https://username@git.example.com/scm/repository.git
or
git remote add origin <gitrepo>
git config --global http.sslVerify falseThe workaround is intended to be used for one-time only operations and not to be used frequently. Removing the SSL verification disproves the whole concept of having SSL implemented.
Resolution
Step1: Get a self-signed certificate of the remote server
There is multiple ways of exporting the certificate, Either from the Browser or using the OpenSSL command
Get Certificate using OpenSSL
Get Certificate using OpenSSL
$ echo | openssl s_client -servername NAME -connect HOST:PORT |
sed -ne '/-BEGIN CERTIFICATE-/,/-END CERTIFICATE-/p' > certificate.pemGet Certificate using the Web browser
Export Certificate in MAC
Trust Certificate in your browser
To trust a self-signed certificate, you need to add it to your Keychain.
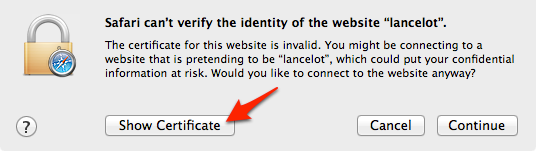
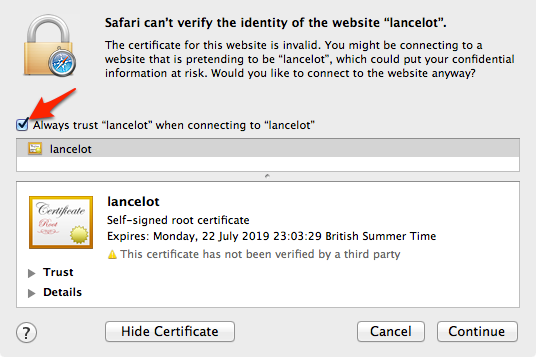
The easiest way to do that is to open the site in question in Safari, upon which you should get this dialog box:
Click ‘Show Certificate’ to reveal the full details:
Export Certificate in .pem format
Git doesn’t use the Mac OS X keychain to resolve this, so you need to trust the certificate explicitly.
- If you haven’t done so already, follow the steps in ‘Trust certificate in your browser, above
- Open Applications > Keychain Access and select ‘Certificates’ in the lower-left pane
- Type the website into the Search field in the top-right
- Select the certificate entry for the website, then in the menu click File > Export Items
- In the Save dialog, change ‘File Format’ to ‘Privacy Enhanced Mail (.pem)’ and save the file somewhere on your drive
Export Certificate From Firefox
- Access the URL of the remote server
- Click the Open padlock in the address bar.
- Click the arrow beside OpenConnection Secure.
- Click More Information. The OpenPage Info dialog box opens.
- Click View Certificate.
- The Certificate page opens.
- Scroll down to the Miscellaneous section.
- In the Download row, click the PEM (cert) link.
- In the dialog box that opens, click OK to save the certificate file to a known location.
- Navigate to the location for saving the file, and then click Save.
Step 2: Configure Git to trust the Certificate
For MAC/Linux:
Once the certificate is saved on the client you can instruct your git client to use it to trust the remote repository by updating the local git config:
# Initial clone
GIT_SSL_CAINFO=/path/to/certificate.pem
git clone https://username@git.example.com/scm/repository.git
# Ensure all future interactions with origin remote also work
cd repository
git config http.sslCAInfo /path/to/certificate.pemFor Windows Client:
Step 1: Import the certificate into the window trust store
Import a signed certificate into the local machine certificate store
- Enter Start | Run | MMC.
- Click File | Add/Remove Snap-in.
- In the Add or Remove Snap-ins window, select Certificates and click Add.
- Select the Computer account radio button when prompted and click Next
- Select Local computer (selected by default) and click Finish.
- Back in the Add or Remove Snap-ins window, click OK.
- In the MMC main console, click on the plus (+) symbol to expand the Certificate snap-in.
- To import the CA certificate, navigate to Trusted Root Certification Authorities | Certificates pane.
- Right-click within the Certificates panel and click All Tasks | Import to start the Certificate Import wizard.
- On successfully importing the CA certificate the wizard will bring you back to the MMC main console.
- Close the MMC console.
Step 2: Configure git to use the certificate in the windows Trust store
When using Windows, the problem resides that git by default uses the «Linux» crypto backend. Starting with Git for Windows 2.14, you can configure Git to use SChannel, the built-in Windows networking layer as the crypto backend. To do that, just run the following command in the GIT client:
git config --global http.sslbackend schannelThis means that it will use the Windows certificate storage mechanism and you don’t need to explicitly configure the curl CA storage (http.sslCAInfo) mechanism. Once you have updated the git config, Git will use the Certificate in the Windows certificate store and should not require http.sslCAInfo setting.
Содержание
- FIX: Self-signed certificate in certificate chain error
- How do I fix self-signed certificate in the certificate chain?
- For Node.js
- For npm
- ERR! self signed certificate in certificate chain #7519
- Comments
- Error: self signed certificate in certificate chain #2061
- Comments
- Footer
- Node.js v19.4.0 documentation
- TLS (SSL) #
- Determining if crypto support is unavailable #
- TLS/SSL concepts #
- Perfect forward secrecy #
- ALPN and SNI #
- Pre-shared keys #
- Client-initiated renegotiation attack mitigation #
- Session resumption #
- Modifying the default TLS cipher suite #
- X509 certificate error codes #
- Class: tls.CryptoStream #
- cryptoStream.bytesWritten #
- Class: tls.SecurePair #
- Event: ‘secure’ #
- Class: tls.Server #
- Event: ‘connection’ #
- Event: ‘keylog’ #
- Event: ‘newSession’ #
- Event: ‘OCSPRequest’ #
- Event: ‘resumeSession’ #
- Event: ‘secureConnection’ #
- Event: ‘tlsClientError’ #
- server.addContext(hostname, context) #
- server.address() #
- server.close([callback]) #
- server.getTicketKeys() #
- server.listen() #
- server.setSecureContext(options) #
- server.setTicketKeys(keys) #
- Class: tls.TLSSocket #
- new tls.TLSSocket(socket[, options]) #
- Event: ‘keylog’ #
- Event: ‘OCSPResponse’ #
- Event: ‘secureConnect’ #
- Event: ‘session’ #
- tlsSocket.address() #
- tlsSocket.authorizationError #
- tlsSocket.authorized #
- tlsSocket.disableRenegotiation() #
- tlsSocket.enableTrace() #
- tlsSocket.encrypted #
- tlsSocket.exportKeyingMaterial(length, label[, context]) #
- tlsSocket.getCertificate() #
- tlsSocket.getCipher() #
- tlsSocket.getEphemeralKeyInfo() #
- tlsSocket.getFinished() #
- tlsSocket.getPeerCertificate([detailed]) #
- tlsSocket.getPeerFinished() #
- tlsSocket.getPeerX509Certificate() #
- tlsSocket.getProtocol() #
- tlsSocket.getSession() #
- tlsSocket.getSharedSigalgs() #
- tlsSocket.getTLSTicket() #
- tlsSocket.getX509Certificate() #
- tlsSocket.isSessionReused() #
- tlsSocket.localAddress #
- tlsSocket.localPort #
- tlsSocket.remoteAddress #
- tlsSocket.remoteFamily #
- tlsSocket.remotePort #
- tlsSocket.renegotiate(options, callback) #
- tlsSocket.setMaxSendFragment(size) #
- tls.checkServerIdentity(hostname, cert) #
- tls.connect(options[, callback]) #
- tls.connect(path[, options][, callback]) #
- tls.connect(port[, host][, options][, callback]) #
- tls.createSecureContext([options]) #
- tls.createSecurePair([context][, isServer][, requestCert][, rejectUnauthorized][, options]) #
- tls.createServer([options][, secureConnectionListener]) #
- tls.getCiphers() #
FIX: Self-signed certificate in certificate chain error
- Since npm stopped automatically accepting self-signed certificates, users have started to report errors while trying to publish some packages in certain applications.
- The error can be fixed, usually, by upgrading the package manager or use the known registrars.
- If you want to read more about security certificate errors, take a look at our dedicated certificate errors section.
- Feel free to explore our Troubleshooting Hub for more helpful articles.
- Download Restoro PC Repair Tool that comes with Patented Technologies (patent available here) .
- Click Start Scan to find Windows issues that could be causing PC problems.
- Click Repair All to fix issues affecting your computer’s security and performance
- Restoro has been downloaded by 0 readers this month.
For some time now, developers encountered a SELF_SIGNED_CERT_IN_CHAIN error during installing and publishing packages in certain applications and developer tools such as Node.js, npm, or Git.
Until a few years ago, when npm for instance announced that they would no longer support self-signed certificates.
This means that the certificate verification process was no longer automatic. So developers now have to set up their application to see the self-signed certificates.
How do I fix self-signed certificate in the certificate chain?
Depending on the tool you’re using, there are a few recommendations. Some are risky, some are safe. One thing is clear, though: you should not attempt to disable the certification verification process altogether.
For Node.js
You can insert an environment variable to allow untrusted certificates using the following command at the beginning of the code:
This is risky and it’s not recommended to be used in production. Alternatively, use npm config set strict-ssl=false if you have to do this for many applications and you want to save repeating the process.
Users also suggest upgrading your version of Node, to fixes any existing bugs and vulnerabilities.
For npm
The recommended solution is, again, to upgrade your version of npm running one of the following:
npm install npm -g —ca=null
npm update npm — g
Or, tell your current version of npm to use known registrars, and after installing, stop using them:
Some users mentioned that they only switched the registry URL from https to http:
We hope that one of these suggestions helped you fix the problem. Should you have any recommendations, please use the comments section below.
Источник
ERR! self signed certificate in certificate chain #7519
I am brand new to Node and NPM.
I downloaded it today and installed it. (I am trying to get Aurelia up and running.)
The first command I tried was this:
And when that happened I got the following Error:
npm ERR! self signed certificate in certificate chain
I saw that a year ago this error happened a lot, but I don’t see why this would be happening to me now. (NOTE: I tried both to npm install npm -g —ca=null (gave the same error) and npm config set ca=»» (did not do anything))
Any suggestions?
NOTE: It may be related that my company does a «Man in the Middle» attack on almost all SSL traffic. (They have a trusted certificate that they have pushed out to all machines. They use that to intercept all traffic.) I don’t know if this could be the cause or not, but the certificate that they pushed out is not «Self Signed».
I did go to https://registry.npmjs.org/gulp and check the certificate at it is issued by my company (so my system admins are doing the «Man in the Middle» thing on that URL.
Also, the error message that told me to come here with my issue also said to post this, so here it is:
0 info it worked if it ends with ok
1 verbose cli [ ‘C:Program Filesnodejsnode.exe’,
1 verbose cli ‘C:Program Filesnodejsnode_modulesnpmbinnpm-cli.js’,
1 verbose cli ‘install’,
1 verbose cli ‘-g’,
1 verbose cli ‘gulp’ ]
2 info using npm@2.5.1
3 info using node@v0.12.0
4 verbose node symlink C:Program Filesnodejsnode.exe
5 silly cache add args [ ‘gulp’, null ]
6 verbose cache add spec gulp
7 silly cache add parsed spec < raw: ‘gulp’,
7 silly cache add scope: null,
7 silly cache add name: ‘gulp’,
7 silly cache add rawSpec: »,
7 silly cache add spec: ‘‘,
7 silly cache add type: ‘range’ >
8 verbose addNamed gulp@
9 silly addNamed semver.valid null
10 silly addNamed semver.validRange *
11 silly addNameRange < name: ‘gulp’, range: ‘*’, hasData: false >
12 silly mapToRegistry name gulp
13 silly mapToRegistry using default registry
14 silly mapToRegistry registry https://registry.npmjs.org/
15 silly mapToRegistry uri https://registry.npmjs.org/gulp
16 verbose addNameRange registry:https://registry.npmjs.org/gulp not in flight; fetching
17 verbose request uri https://registry.npmjs.org/gulp
18 verbose request no auth needed
19 info attempt registry request try #1 at 5:07:15 PM
20 verbose request id adc0ceb5a3fc1f77
21 http request GET https://registry.npmjs.org/gulp
22 info retry will retry, error on last attempt: Error: self signed certificate in certificate chain
23 info attempt registry request try #2 at 5:07:25 PM
24 http request GET https://registry.npmjs.org/gulp
25 info retry will retry, error on last attempt: Error: self signed certificate in certificate chain
26 info attempt registry request try #3 at 5:08:26 PM
27 http request GET https://registry.npmjs.org/gulp
28 verbose stack Error: self signed certificate in certificate chain
28 verbose stack at Error (native)
28 verbose stack at TLSSocket. (_tls_wrap.js:927:36)
28 verbose stack at TLSSocket.emit (events.js:104:17)
28 verbose stack at TLSSocket._finishInit (_tls_wrap.js:458:8)
29 verbose cwd C:Users18773
30 error Windows_NT 6.1.7601
31 error argv «C:Program Filesnodejsnode.exe» «C:Program Filesnodejsnode_modulesnpmbinnpm-cli.js» «install» «-g» «gulp»
32 error node v0.12.0
33 error npm v2.5.1
34 error code SELF_SIGNED_CERT_IN_CHAIN
35 error self signed certificate in certificate chain
36 error If you need help, you may report this error at:
36 error http://github.com/npm/npm/issues
37 verbose exit [ 1, true ]
The text was updated successfully, but these errors were encountered:
Источник
Error: self signed certificate in certificate chain #2061
I’m trying to analyze my requests against a server using Charles Proxy. The server uses TSL so I have the classic fake certificate to be able to view clear traffic.
NodeJS / Request don’t like it, so my script doesn’t run and throws that error.
How can I bypass this?
The text was updated successfully, but these errors were encountered:
in this case response is undefined.
response doesn’t have to be defined.
response will be only defined if an actual response arrived.
if there was some connection error that is not the case.
check for error to be defined, or response.statusCode to be greater or equal than 400.
if you want to debug this use
Thanks for the explanation. I found out how to avoid problems with fake certificates in case anyone is interested:
With that I can use fake SSL auth to inspect the communications between my client and a server.
My error was similar but now I»m good thanks @nmaxcom
Error: unable to verify the first certificate
at Error (native)
at TLSSocket. (_tls_wrap.js:929:36)
at TLSSocket.emit (events.js:104:17)
at TLSSocket._finishInit (_tls_wrap.js:460:8)
or you can just use let’s encrypt, certificates that are signed by a legit CA.
self signed certificates dont make sense now.
For self-signed CA, we can specify ‘rejectUnauthorized = false’.
Check request.js at line 623 & _tls_wrap.js in node.js.
Better alternatives are:
a) Do SSL termination at your load balancer
b) Use a free certificate
In this way you have a single configuration across all your environments.
You will have higher confidence on your deployments and filter errors earlier.
rejectUnauthorized works in options.rejectUnauthorized = false
but not in options.agentOptions.rejectUnauthorized = false
Sorry, only see the code. I get that strictSSL is just an alias to rejectUnauthorized
Have to say that’s a bad name, just use rejectUnauthorized 😭
getting this error while runnign code
Parse error: syntax error, unexpected ‘var’ (T_VAR), expecting end of file in C:xampphtdocsPHPIMAPadminindex.php on line 146
for people who suggest to set rejectUnauthorized=false what if i have internal servers that should have encrypted connections with each other with some self signed certificates , iguess setting rejectUnauthorized to false will stop the error but my connections are 100% prone to MITM atacks , I see that this is a bug in nodejs tls library that it suffers from and i can’t find any fix any where (i have google to page 5 of google results that is really deep) i don’t know how other people don’t talk about it , AM I missing something here! . please correct me if i am wrong !!
Both do not work for me
P.S. Running the code from within ELECTRON with ssl disable flag on.
For me, disabling Kaspersky antivirus solved the problem.
#2061 (comment) seems to be the answer to the general question
Gives no effect.
© 2023 GitHub, Inc.
You can’t perform that action at this time.
You signed in with another tab or window. Reload to refresh your session. You signed out in another tab or window. Reload to refresh your session.
Источник
Node.js v19.4.0 documentation
TLS (SSL) #
Source Code: lib/tls.js
The node:tls module provides an implementation of the Transport Layer Security (TLS) and Secure Socket Layer (SSL) protocols that is built on top of OpenSSL. The module can be accessed using:
Determining if crypto support is unavailable #
It is possible for Node.js to be built without including support for the node:crypto module. In such cases, attempting to import from tls or calling require(‘node:tls’) will result in an error being thrown.
When using CommonJS, the error thrown can be caught using try/catch:
When using the lexical ESM import keyword, the error can only be caught if a handler for process.on(‘uncaughtException’) is registered before any attempt to load the module is made (using, for instance, a preload module).
When using ESM, if there is a chance that the code may be run on a build of Node.js where crypto support is not enabled, consider using the import() function instead of the lexical import keyword:
TLS/SSL concepts #
TLS/SSL is a set of protocols that rely on a public key infrastructure (PKI) to enable secure communication between a client and a server. For most common cases, each server must have a private key.
Private keys can be generated in multiple ways. The example below illustrates use of the OpenSSL command-line interface to generate a 2048-bit RSA private key:
With TLS/SSL, all servers (and some clients) must have a certificate. Certificates are public keys that correspond to a private key, and that are digitally signed either by a Certificate Authority or by the owner of the private key (such certificates are referred to as «self-signed»). The first step to obtaining a certificate is to create a Certificate Signing Request (CSR) file.
The OpenSSL command-line interface can be used to generate a CSR for a private key:
Once the CSR file is generated, it can either be sent to a Certificate Authority for signing or used to generate a self-signed certificate.
Creating a self-signed certificate using the OpenSSL command-line interface is illustrated in the example below:
Once the certificate is generated, it can be used to generate a .pfx or .p12 file:
- in : is the signed certificate
- inkey : is the associated private key
- certfile : is a concatenation of all Certificate Authority (CA) certs into a single file, e.g. cat ca1-cert.pem ca2-cert.pem > ca-cert.pem
Perfect forward secrecy #
The term forward secrecy or perfect forward secrecy describes a feature of key-agreement (i.e., key-exchange) methods. That is, the server and client keys are used to negotiate new temporary keys that are used specifically and only for the current communication session. Practically, this means that even if the server’s private key is compromised, communication can only be decrypted by eavesdroppers if the attacker manages to obtain the key-pair specifically generated for the session.
Perfect forward secrecy is achieved by randomly generating a key pair for key-agreement on every TLS/SSL handshake (in contrast to using the same key for all sessions). Methods implementing this technique are called «ephemeral».
Currently two methods are commonly used to achieve perfect forward secrecy (note the character «E» appended to the traditional abbreviations):
- DHE: An ephemeral version of the Diffie-Hellman key-agreement protocol.
- ECDHE: An ephemeral version of the Elliptic Curve Diffie-Hellman key-agreement protocol.
To use perfect forward secrecy using DHE with the node:tls module, it is required to generate Diffie-Hellman parameters and specify them with the dhparam option to tls.createSecureContext() . The following illustrates the use of the OpenSSL command-line interface to generate such parameters:
If using perfect forward secrecy using ECDHE , Diffie-Hellman parameters are not required and a default ECDHE curve will be used. The ecdhCurve property can be used when creating a TLS Server to specify the list of names of supported curves to use, see tls.createServer() for more info.
Perfect forward secrecy was optional up to TLSv1.2, but it is not optional for TLSv1.3, because all TLSv1.3 cipher suites use ECDHE.
ALPN and SNI #
ALPN (Application-Layer Protocol Negotiation Extension) and SNI (Server Name Indication) are TLS handshake extensions:
- ALPN: Allows the use of one TLS server for multiple protocols (HTTP, HTTP/2)
- SNI: Allows the use of one TLS server for multiple hostnames with different certificates.
Pre-shared keys #
TLS-PSK support is available as an alternative to normal certificate-based authentication. It uses a pre-shared key instead of certificates to authenticate a TLS connection, providing mutual authentication. TLS-PSK and public key infrastructure are not mutually exclusive. Clients and servers can accommodate both, choosing either of them during the normal cipher negotiation step.
TLS-PSK is only a good choice where means exist to securely share a key with every connecting machine, so it does not replace the public key infrastructure (PKI) for the majority of TLS uses. The TLS-PSK implementation in OpenSSL has seen many security flaws in recent years, mostly because it is used only by a minority of applications. Please consider all alternative solutions before switching to PSK ciphers. Upon generating PSK it is of critical importance to use sufficient entropy as discussed in RFC 4086. Deriving a shared secret from a password or other low-entropy sources is not secure.
PSK ciphers are disabled by default, and using TLS-PSK thus requires explicitly specifying a cipher suite with the ciphers option. The list of available ciphers can be retrieved via openssl ciphers -v ‘PSK’ . All TLS 1.3 ciphers are eligible for PSK but currently only those that use SHA256 digest are supported they can be retrieved via openssl ciphers -v -s -tls1_3 -psk .
According to the RFC 4279, PSK identities up to 128 bytes in length and PSKs up to 64 bytes in length must be supported. As of OpenSSL 1.1.0 maximum identity size is 128 bytes, and maximum PSK length is 256 bytes.
The current implementation doesn’t support asynchronous PSK callbacks due to the limitations of the underlying OpenSSL API.
Client-initiated renegotiation attack mitigation #
The TLS protocol allows clients to renegotiate certain aspects of the TLS session. Unfortunately, session renegotiation requires a disproportionate amount of server-side resources, making it a potential vector for denial-of-service attacks.
To mitigate the risk, renegotiation is limited to three times every ten minutes. An ‘error’ event is emitted on the tls.TLSSocket instance when this threshold is exceeded. The limits are configurable:
- tls.CLIENT_RENEG_LIMIT Specifies the number of renegotiation requests. Default: 3 .
- tls.CLIENT_RENEG_WINDOW Specifies the time renegotiation window in seconds. Default: 600 (10 minutes).
The default renegotiation limits should not be modified without a full understanding of the implications and risks.
TLSv1.3 does not support renegotiation.
Session resumption #
Establishing a TLS session can be relatively slow. The process can be sped up by saving and later reusing the session state. There are several mechanisms to do so, discussed here from oldest to newest (and preferred).
Session identifiers #
Servers generate a unique ID for new connections and send it to the client. Clients and servers save the session state. When reconnecting, clients send the ID of their saved session state and if the server also has the state for that ID, it can agree to use it. Otherwise, the server will create a new session. See RFC 2246 for more information, page 23 and 30.
Resumption using session identifiers is supported by most web browsers when making HTTPS requests.
For Node.js, clients wait for the ‘session’ event to get the session data, and provide the data to the session option of a subsequent tls.connect() to reuse the session. Servers must implement handlers for the ‘newSession’ and ‘resumeSession’ events to save and restore the session data using the session ID as the lookup key to reuse sessions. To reuse sessions across load balancers or cluster workers, servers must use a shared session cache (such as Redis) in their session handlers.
Session tickets #
The servers encrypt the entire session state and send it to the client as a «ticket». When reconnecting, the state is sent to the server in the initial connection. This mechanism avoids the need for a server-side session cache. If the server doesn’t use the ticket, for any reason (failure to decrypt it, it’s too old, etc.), it will create a new session and send a new ticket. See RFC 5077 for more information.
Resumption using session tickets is becoming commonly supported by many web browsers when making HTTPS requests.
For Node.js, clients use the same APIs for resumption with session identifiers as for resumption with session tickets. For debugging, if tls.TLSSocket.getTLSTicket() returns a value, the session data contains a ticket, otherwise it contains client-side session state.
With TLSv1.3, be aware that multiple tickets may be sent by the server, resulting in multiple ‘session’ events, see ‘session’ for more information.
Single process servers need no specific implementation to use session tickets. To use session tickets across server restarts or load balancers, servers must all have the same ticket keys. There are three 16-byte keys internally, but the tls API exposes them as a single 48-byte buffer for convenience.
It’s possible to get the ticket keys by calling server.getTicketKeys() on one server instance and then distribute them, but it is more reasonable to securely generate 48 bytes of secure random data and set them with the ticketKeys option of tls.createServer() . The keys should be regularly regenerated and server’s keys can be reset with server.setTicketKeys() .
Session ticket keys are cryptographic keys, and they must be stored securely. With TLS 1.2 and below, if they are compromised all sessions that used tickets encrypted with them can be decrypted. They should not be stored on disk, and they should be regenerated regularly.
If clients advertise support for tickets, the server will send them. The server can disable tickets by supplying require(‘node:constants’).SSL_OP_NO_TICKET in secureOptions .
Both session identifiers and session tickets timeout, causing the server to create new sessions. The timeout can be configured with the sessionTimeout option of tls.createServer() .
For all the mechanisms, when resumption fails, servers will create new sessions. Since failing to resume the session does not cause TLS/HTTPS connection failures, it is easy to not notice unnecessarily poor TLS performance. The OpenSSL CLI can be used to verify that servers are resuming sessions. Use the -reconnect option to openssl s_client , for example:
Read through the debug output. The first connection should say «New», for example:
Subsequent connections should say «Reused», for example:
Modifying the default TLS cipher suite #
Node.js is built with a default suite of enabled and disabled TLS ciphers. This default cipher list can be configured when building Node.js to allow distributions to provide their own default list.
The following command can be used to show the default cipher suite:
This default can be replaced entirely using the —tls-cipher-list command-line switch (directly, or via the NODE_OPTIONS environment variable). For instance, the following makes ECDHE-RSA-AES128-GCM-SHA256:!RC4 the default TLS cipher suite:
The default can also be replaced on a per client or server basis using the ciphers option from tls.createSecureContext() , which is also available in tls.createServer() , tls.connect() , and when creating new tls.TLSSocket s.
The ciphers list can contain a mixture of TLSv1.3 cipher suite names, the ones that start with ‘TLS_’ , and specifications for TLSv1.2 and below cipher suites. The TLSv1.2 ciphers support a legacy specification format, consult the OpenSSL cipher list format documentation for details, but those specifications do not apply to TLSv1.3 ciphers. The TLSv1.3 suites can only be enabled by including their full name in the cipher list. They cannot, for example, be enabled or disabled by using the legacy TLSv1.2 ‘EECDH’ or ‘!EECDH’ specification.
Despite the relative order of TLSv1.3 and TLSv1.2 cipher suites, the TLSv1.3 protocol is significantly more secure than TLSv1.2, and will always be chosen over TLSv1.2 if the handshake indicates it is supported, and if any TLSv1.3 cipher suites are enabled.
The default cipher suite included within Node.js has been carefully selected to reflect current security best practices and risk mitigation. Changing the default cipher suite can have a significant impact on the security of an application. The —tls-cipher-list switch and ciphers option should by used only if absolutely necessary.
The default cipher suite prefers GCM ciphers for Chrome’s ‘modern cryptography’ setting and also prefers ECDHE and DHE ciphers for perfect forward secrecy, while offering some backward compatibility.
Old clients that rely on insecure and deprecated RC4 or DES-based ciphers (like Internet Explorer 6) cannot complete the handshaking process with the default configuration. If these clients must be supported, the TLS recommendations may offer a compatible cipher suite. For more details on the format, see the OpenSSL cipher list format documentation.
There are only five TLSv1.3 cipher suites:
- ‘TLS_AES_256_GCM_SHA384’
- ‘TLS_CHACHA20_POLY1305_SHA256’
- ‘TLS_AES_128_GCM_SHA256’
- ‘TLS_AES_128_CCM_SHA256’
- ‘TLS_AES_128_CCM_8_SHA256’
The first three are enabled by default. The two CCM -based suites are supported by TLSv1.3 because they may be more performant on constrained systems, but they are not enabled by default since they offer less security.
X509 certificate error codes #
Multiple functions can fail due to certificate errors that are reported by OpenSSL. In such a case, the function provides an via its callback that has the property code which can take one of the following values:
- ‘UNABLE_TO_GET_ISSUER_CERT’ : Unable to get issuer certificate.
- ‘UNABLE_TO_GET_CRL’ : Unable to get certificate CRL.
- ‘UNABLE_TO_DECRYPT_CERT_SIGNATURE’ : Unable to decrypt certificate’s signature.
- ‘UNABLE_TO_DECRYPT_CRL_SIGNATURE’ : Unable to decrypt CRL’s signature.
- ‘UNABLE_TO_DECODE_ISSUER_PUBLIC_KEY’ : Unable to decode issuer public key.
- ‘CERT_SIGNATURE_FAILURE’ : Certificate signature failure.
- ‘CRL_SIGNATURE_FAILURE’ : CRL signature failure.
- ‘CERT_NOT_YET_VALID’ : Certificate is not yet valid.
- ‘CERT_HAS_EXPIRED’ : Certificate has expired.
- ‘CRL_NOT_YET_VALID’ : CRL is not yet valid.
- ‘CRL_HAS_EXPIRED’ : CRL has expired.
- ‘ERROR_IN_CERT_NOT_BEFORE_FIELD’ : Format error in certificate’s notBefore field.
- ‘ERROR_IN_CERT_NOT_AFTER_FIELD’ : Format error in certificate’s notAfter field.
- ‘ERROR_IN_CRL_LAST_UPDATE_FIELD’ : Format error in CRL’s lastUpdate field.
- ‘ERROR_IN_CRL_NEXT_UPDATE_FIELD’ : Format error in CRL’s nextUpdate field.
- ‘OUT_OF_MEM’ : Out of memory.
- ‘DEPTH_ZERO_SELF_SIGNED_CERT’ : Self signed certificate.
- ‘SELF_SIGNED_CERT_IN_CHAIN’ : Self signed certificate in certificate chain.
- ‘UNABLE_TO_GET_ISSUER_CERT_LOCALLY’ : Unable to get local issuer certificate.
- ‘UNABLE_TO_VERIFY_LEAF_SIGNATURE’ : Unable to verify the first certificate.
- ‘CERT_CHAIN_TOO_LONG’ : Certificate chain too long.
- ‘CERT_REVOKED’ : Certificate revoked.
- ‘INVALID_CA’ : Invalid CA certificate.
- ‘PATH_LENGTH_EXCEEDED’ : Path length constraint exceeded.
- ‘INVALID_PURPOSE’ : Unsupported certificate purpose.
- ‘CERT_UNTRUSTED’ : Certificate not trusted.
- ‘CERT_REJECTED’ : Certificate rejected.
- ‘HOSTNAME_MISMATCH’ : Hostname mismatch.
Class: tls.CryptoStream #
The tls.CryptoStream class represents a stream of encrypted data. This class is deprecated and should no longer be used.
cryptoStream.bytesWritten #
The cryptoStream.bytesWritten property returns the total number of bytes written to the underlying socket including the bytes required for the implementation of the TLS protocol.
Class: tls.SecurePair #
Event: ‘secure’ #
The ‘secure’ event is emitted by the SecurePair object once a secure connection has been established.
As with checking for the server ‘secureConnection’ event, pair.cleartext.authorized should be inspected to confirm whether the certificate used is properly authorized.
Class: tls.Server #
Accepts encrypted connections using TLS or SSL.
Event: ‘connection’ #
This event is emitted when a new TCP stream is established, before the TLS handshake begins. socket is typically an object of type net.Socket but will not receive events unlike the socket created from the net.Server ‘connection’ event. Usually users will not want to access this event.
This event can also be explicitly emitted by users to inject connections into the TLS server. In that case, any Duplex stream can be passed.
Event: ‘keylog’ #
- line Line of ASCII text, in NSS SSLKEYLOGFILE format.
- tlsSocket The tls.TLSSocket instance on which it was generated.
The keylog event is emitted when key material is generated or received by a connection to this server (typically before handshake has completed, but not necessarily). This keying material can be stored for debugging, as it allows captured TLS traffic to be decrypted. It may be emitted multiple times for each socket.
A typical use case is to append received lines to a common text file, which is later used by software (such as Wireshark) to decrypt the traffic:
Event: ‘newSession’ #
History
The callback argument is now supported.
The ‘newSession’ event is emitted upon creation of a new TLS session. This may be used to store sessions in external storage. The data should be provided to the ‘resumeSession’ callback.
The listener callback is passed three arguments when called:
- sessionId The TLS session identifier
- sessionData The TLS session data
- callback A callback function taking no arguments that must be invoked in order for data to be sent or received over the secure connection.
Listening for this event will have an effect only on connections established after the addition of the event listener.
Event: ‘OCSPRequest’ #
The ‘OCSPRequest’ event is emitted when the client sends a certificate status request. The listener callback is passed three arguments when called:
- certificate The server certificate
- issuer The issuer’s certificate
- callback A callback function that must be invoked to provide the results of the OCSP request.
The server’s current certificate can be parsed to obtain the OCSP URL and certificate ID; after obtaining an OCSP response, callback(null, resp) is then invoked, where resp is a Buffer instance containing the OCSP response. Both certificate and issuer are Buffer DER-representations of the primary and issuer’s certificates. These can be used to obtain the OCSP certificate ID and OCSP endpoint URL.
Alternatively, callback(null, null) may be called, indicating that there was no OCSP response.
Calling callback(err) will result in a socket.destroy(err) call.
The typical flow of an OCSP request is as follows:
- Client connects to the server and sends an ‘OCSPRequest’ (via the status info extension in ClientHello).
- Server receives the request and emits the ‘OCSPRequest’ event, calling the listener if registered.
- Server extracts the OCSP URL from either the certificate or issuer and performs an OCSP request to the CA.
- Server receives ‘OCSPResponse’ from the CA and sends it back to the client via the callback argument
- Client validates the response and either destroys the socket or performs a handshake.
The issuer can be null if the certificate is either self-signed or the issuer is not in the root certificates list. (An issuer may be provided via the ca option when establishing the TLS connection.)
Listening for this event will have an effect only on connections established after the addition of the event listener.
An npm module like asn1.js may be used to parse the certificates.
Event: ‘resumeSession’ #
The ‘resumeSession’ event is emitted when the client requests to resume a previous TLS session. The listener callback is passed two arguments when called:
- sessionId The TLS session identifier
- callback A callback function to be called when the prior session has been recovered: callback([err[, sessionData]])
- err
- sessionData
The event listener should perform a lookup in external storage for the sessionData saved by the ‘newSession’ event handler using the given sessionId . If found, call callback(null, sessionData) to resume the session. If not found, the session cannot be resumed. callback() must be called without sessionData so that the handshake can continue and a new session can be created. It is possible to call callback(err) to terminate the incoming connection and destroy the socket.
Listening for this event will have an effect only on connections established after the addition of the event listener.
The following illustrates resuming a TLS session:
Event: ‘secureConnection’ #
The ‘secureConnection’ event is emitted after the handshaking process for a new connection has successfully completed. The listener callback is passed a single argument when called:
- tlsSocket The established TLS socket.
The tlsSocket.authorized property is a boolean indicating whether the client has been verified by one of the supplied Certificate Authorities for the server. If tlsSocket.authorized is false , then socket.authorizationError is set to describe how authorization failed. Depending on the settings of the TLS server, unauthorized connections may still be accepted.
The tlsSocket.alpnProtocol property is a string that contains the selected ALPN protocol. When ALPN has no selected protocol because the client or the server did not send an ALPN extension, tlsSocket.alpnProtocol equals false .
The tlsSocket.servername property is a string containing the server name requested via SNI.
Event: ‘tlsClientError’ #
The ‘tlsClientError’ event is emitted when an error occurs before a secure connection is established. The listener callback is passed two arguments when called:
- exception The Error object describing the error
- tlsSocket The tls.TLSSocket instance from which the error originated.
server.addContext(hostname, context) #
- hostname A SNI host name or wildcard (e.g. ‘*’ )
- context An object containing any of the possible properties from the tls.createSecureContext() options arguments (e.g. key , cert , ca , etc).
The server.addContext() method adds a secure context that will be used if the client request’s SNI name matches the supplied hostname (or wildcard).
When there are multiple matching contexts, the most recently added one is used.
server.address() #
Returns the bound address, the address family name, and port of the server as reported by the operating system. See net.Server.address() for more information.
server.close([callback]) #
- callback A listener callback that will be registered to listen for the server instance’s ‘close’ event.
- Returns:
The server.close() method stops the server from accepting new connections.
This function operates asynchronously. The ‘close’ event will be emitted when the server has no more open connections.
server.getTicketKeys() #
- Returns: A 48-byte buffer containing the session ticket keys.
Returns the session ticket keys.
See Session Resumption for more information.
server.listen() #
Starts the server listening for encrypted connections. This method is identical to server.listen() from net.Server .
server.setSecureContext(options) #
- options An object containing any of the possible properties from the tls.createSecureContext() options arguments (e.g. key , cert , ca , etc).
The server.setSecureContext() method replaces the secure context of an existing server. Existing connections to the server are not interrupted.
server.setTicketKeys(keys) #
- keys | | A 48-byte buffer containing the session ticket keys.
Sets the session ticket keys.
Changes to the ticket keys are effective only for future server connections. Existing or currently pending server connections will use the previous keys.
See Session Resumption for more information.
Class: tls.TLSSocket #
Performs transparent encryption of written data and all required TLS negotiation.
Instances of tls.TLSSocket implement the duplex Stream interface.
Methods that return TLS connection metadata (e.g. tls.TLSSocket.getPeerCertificate() ) will only return data while the connection is open.
new tls.TLSSocket(socket[, options]) #
History
| Version | Changes |
|---|---|
| v0.11.12 |
The enableTrace option is now supported.
ALPN options are supported now.
- socket | On the server side, any Duplex stream. On the client side, any instance of net.Socket (for generic Duplex stream support on the client side, tls.connect() must be used).
- options
- enableTrace : See tls.createServer()
- isServer : The SSL/TLS protocol is asymmetrical, TLSSockets must know if they are to behave as a server or a client. If true the TLS socket will be instantiated as a server. Default: false .
- server A net.Server instance.
- requestCert : Whether to authenticate the remote peer by requesting a certificate. Clients always request a server certificate. Servers ( isServer is true) may set requestCert to true to request a client certificate.
- rejectUnauthorized : See tls.createServer()
- ALPNProtocols : See tls.createServer()
- SNICallback : See tls.createServer()
- session A Buffer instance containing a TLS session.
- requestOCSP If true , specifies that the OCSP status request extension will be added to the client hello and an ‘OCSPResponse’ event will be emitted on the socket before establishing a secure communication
- secureContext : TLS context object created with tls.createSecureContext() . If a secureContext is not provided, one will be created by passing the entire options object to tls.createSecureContext() .
- . tls.createSecureContext() options that are used if the secureContext option is missing. Otherwise, they are ignored.
Construct a new tls.TLSSocket object from an existing TCP socket.
Event: ‘keylog’ #
- line Line of ASCII text, in NSS SSLKEYLOGFILE format.
The keylog event is emitted on a tls.TLSSocket when key material is generated or received by the socket. This keying material can be stored for debugging, as it allows captured TLS traffic to be decrypted. It may be emitted multiple times, before or after the handshake completes.
A typical use case is to append received lines to a common text file, which is later used by software (such as Wireshark) to decrypt the traffic:
Event: ‘OCSPResponse’ #
The ‘OCSPResponse’ event is emitted if the requestOCSP option was set when the tls.TLSSocket was created and an OCSP response has been received. The listener callback is passed a single argument when called:
- response The server’s OCSP response
Typically, the response is a digitally signed object from the server’s CA that contains information about server’s certificate revocation status.
Event: ‘secureConnect’ #
The ‘secureConnect’ event is emitted after the handshaking process for a new connection has successfully completed. The listener callback will be called regardless of whether or not the server’s certificate has been authorized. It is the client’s responsibility to check the tlsSocket.authorized property to determine if the server certificate was signed by one of the specified CAs. If tlsSocket.authorized === false , then the error can be found by examining the tlsSocket.authorizationError property. If ALPN was used, the tlsSocket.alpnProtocol property can be checked to determine the negotiated protocol.
The ‘secureConnect’ event is not emitted when a is created using the new tls.TLSSocket() constructor.
Event: ‘session’ #
The ‘session’ event is emitted on a client tls.TLSSocket when a new session or TLS ticket is available. This may or may not be before the handshake is complete, depending on the TLS protocol version that was negotiated. The event is not emitted on the server, or if a new session was not created, for example, when the connection was resumed. For some TLS protocol versions the event may be emitted multiple times, in which case all the sessions can be used for resumption.
On the client, the session can be provided to the session option of tls.connect() to resume the connection.
See Session Resumption for more information.
For TLSv1.2 and below, tls.TLSSocket.getSession() can be called once the handshake is complete. For TLSv1.3, only ticket-based resumption is allowed by the protocol, multiple tickets are sent, and the tickets aren’t sent until after the handshake completes. So it is necessary to wait for the ‘session’ event to get a resumable session. Applications should use the ‘session’ event instead of getSession() to ensure they will work for all TLS versions. Applications that only expect to get or use one session should listen for this event only once:
tlsSocket.address() #
History
| Version | Changes |
|---|---|
| v12.2.0 |
The family property now returns a string instead of a number.
The family property now returns a number instead of a string.
Returns the bound address , the address family name, and port of the underlying socket as reported by the operating system: < port: 12346, family: ‘IPv4’, address: ‘127.0.0.1’ >.
Returns the reason why the peer’s certificate was not been verified. This property is set only when tlsSocket.authorized === false .
tlsSocket.authorized #
This property is true if the peer certificate was signed by one of the CAs specified when creating the tls.TLSSocket instance, otherwise false .
tlsSocket.disableRenegotiation() #
Disables TLS renegotiation for this TLSSocket instance. Once called, attempts to renegotiate will trigger an ‘error’ event on the TLSSocket .
tlsSocket.enableTrace() #
When enabled, TLS packet trace information is written to stderr . This can be used to debug TLS connection problems.
The format of the output is identical to the output of openssl s_client -trace or openssl s_server -trace . While it is produced by OpenSSL’s SSL_trace() function, the format is undocumented, can change without notice, and should not be relied on.
tlsSocket.encrypted #
Always returns true . This may be used to distinguish TLS sockets from regular net.Socket instances.
tlsSocket.exportKeyingMaterial(length, label[, context]) #
length number of bytes to retrieve from keying material
label an application specific label, typically this will be a value from the IANA Exporter Label Registry.
context Optionally provide a context.
Returns: requested bytes of the keying material
Keying material is used for validations to prevent different kind of attacks in network protocols, for example in the specifications of IEEE 802.1X.
See the OpenSSL SSL_export_keying_material documentation for more information.
tlsSocket.getCertificate() #
Returns an object representing the local certificate. The returned object has some properties corresponding to the fields of the certificate.
See tls.TLSSocket.getPeerCertificate() for an example of the certificate structure.
If there is no local certificate, an empty object will be returned. If the socket has been destroyed, null will be returned.
tlsSocket.getCipher() #
History
| Version | Changes |
|---|---|
| v18.4.0 |
Return the IETF cipher name as standardName .
Return the minimum cipher version, instead of a fixed string ( ‘TLSv1/SSLv3’ ).
- Returns:
- name OpenSSL name for the cipher suite.
- standardName IETF name for the cipher suite.
- version The minimum TLS protocol version supported by this cipher suite. For the actual negotiated protocol, see tls.TLSSocket.getProtocol() .
Returns an object containing information on the negotiated cipher suite.
For example, a TLSv1.2 protocol with AES256-SHA cipher:
See SSL_CIPHER_get_name for more information.
tlsSocket.getEphemeralKeyInfo() #
Returns an object representing the type, name, and size of parameter of an ephemeral key exchange in perfect forward secrecy on a client connection. It returns an empty object when the key exchange is not ephemeral. As this is only supported on a client socket; null is returned if called on a server socket. The supported types are ‘DH’ and ‘ECDH’ . The name property is available only when type is ‘ECDH’ .
tlsSocket.getFinished() #
- Returns: | The latest Finished message that has been sent to the socket as part of a SSL/TLS handshake, or undefined if no Finished message has been sent yet.
As the Finished messages are message digests of the complete handshake (with a total of 192 bits for TLS 1.0 and more for SSL 3.0), they can be used for external authentication procedures when the authentication provided by SSL/TLS is not desired or is not enough.
Corresponds to the SSL_get_finished routine in OpenSSL and may be used to implement the tls-unique channel binding from RFC 5929.
tlsSocket.getPeerCertificate([detailed]) #
- detailed Include the full certificate chain if true , otherwise include just the peer’s certificate.
- Returns: A certificate object.
Returns an object representing the peer’s certificate. If the peer does not provide a certificate, an empty object will be returned. If the socket has been destroyed, null will be returned.
If the full certificate chain was requested, each certificate will include an issuerCertificate property containing an object representing its issuer’s certificate.
Certificate object #
History
| Version | Changes |
|---|---|
| v13.4.0, v12.16.0 |
Add «ca» property.
Support Elliptic Curve public key info.
A certificate object has properties corresponding to the fields of the certificate.
- ca true if a Certificate Authority (CA), false otherwise.
- raw The DER encoded X.509 certificate data.
- subject The certificate subject, described in terms of Country ( C ), StateOrProvince ( ST ), Locality ( L ), Organization ( O ), OrganizationalUnit ( OU ), and CommonName ( CN ). The CommonName is typically a DNS name with TLS certificates. Example: .
- issuer The certificate issuer, described in the same terms as the subject .
- valid_from The date-time the certificate is valid from.
- valid_to The date-time the certificate is valid to.
- serialNumber The certificate serial number, as a hex string. Example: ‘B9B0D332A1AA5635’ .
- fingerprint The SHA-1 digest of the DER encoded certificate. It is returned as a : separated hexadecimal string. Example: ‘2A:7A:C2:DD. ‘ .
- fingerprint256 The SHA-256 digest of the DER encoded certificate. It is returned as a : separated hexadecimal string. Example: ‘2A:7A:C2:DD. ‘ .
- fingerprint512 The SHA-512 digest of the DER encoded certificate. It is returned as a : separated hexadecimal string. Example: ‘2A:7A:C2:DD. ‘ .
- ext_key_usage (Optional) The extended key usage, a set of OIDs.
- subjectaltname (Optional) A string containing concatenated names for the subject, an alternative to the subject names.
- infoAccess (Optional) An array describing the AuthorityInfoAccess, used with OCSP.
- issuerCertificate (Optional) The issuer certificate object. For self-signed certificates, this may be a circular reference.
The certificate may contain information about the public key, depending on the key type.
For RSA keys, the following properties may be defined:
- bits The RSA bit size. Example: 1024 .
- exponent The RSA exponent, as a string in hexadecimal number notation. Example: ‘0x010001’ .
- modulus The RSA modulus, as a hexadecimal string. Example: ‘B56CE45CB7. ‘ .
- pubkey The public key.
For EC keys, the following properties may be defined:
- pubkey The public key.
- bits The key size in bits. Example: 256 .
- asn1Curve (Optional) The ASN.1 name of the OID of the elliptic curve. Well-known curves are identified by an OID. While it is unusual, it is possible that the curve is identified by its mathematical properties, in which case it will not have an OID. Example: ‘prime256v1’ .
- nistCurve (Optional) The NIST name for the elliptic curve, if it has one (not all well-known curves have been assigned names by NIST). Example: ‘P-256’ .
tlsSocket.getPeerFinished() #
- Returns: | The latest Finished message that is expected or has actually been received from the socket as part of a SSL/TLS handshake, or undefined if there is no Finished message so far.
As the Finished messages are message digests of the complete handshake (with a total of 192 bits for TLS 1.0 and more for SSL 3.0), they can be used for external authentication procedures when the authentication provided by SSL/TLS is not desired or is not enough.
Corresponds to the SSL_get_peer_finished routine in OpenSSL and may be used to implement the tls-unique channel binding from RFC 5929.
tlsSocket.getPeerX509Certificate() #
Returns the peer certificate as an object.
If there is no peer certificate, or the socket has been destroyed, undefined will be returned.
tlsSocket.getProtocol() #
Returns a string containing the negotiated SSL/TLS protocol version of the current connection. The value ‘unknown’ will be returned for connected sockets that have not completed the handshaking process. The value null will be returned for server sockets or disconnected client sockets.
Protocol versions are:
See the OpenSSL SSL_get_version documentation for more information.
tlsSocket.getSession() #
Returns the TLS session data or undefined if no session was negotiated. On the client, the data can be provided to the session option of tls.connect() to resume the connection. On the server, it may be useful for debugging.
See Session Resumption for more information.
Note: getSession() works only for TLSv1.2 and below. For TLSv1.3, applications must use the ‘session’ event (it also works for TLSv1.2 and below).
tlsSocket.getSharedSigalgs() #
tlsSocket.getTLSTicket() #
For a client, returns the TLS session ticket if one is available, or undefined . For a server, always returns undefined .
It may be useful for debugging.
See Session Resumption for more information.
tlsSocket.getX509Certificate() #
Returns the local certificate as an object.
If there is no local certificate, or the socket has been destroyed, undefined will be returned.
tlsSocket.isSessionReused() #
- Returns: true if the session was reused, false otherwise.
See Session Resumption for more information.
tlsSocket.localAddress #
Returns the string representation of the local IP address.
tlsSocket.localPort #
Returns the numeric representation of the local port.
tlsSocket.remoteAddress #
Returns the string representation of the remote IP address. For example, ‘74.125.127.100’ or ‘2001:4860:a005::68’ .
tlsSocket.remoteFamily #
Returns the string representation of the remote IP family. ‘IPv4’ or ‘IPv6’ .
tlsSocket.remotePort #
Returns the numeric representation of the remote port. For example, 443 .
tlsSocket.renegotiate(options, callback) #
History
| Version | Changes |
|---|---|
| v19.1.0 |
Passing an invalid callback to the callback argument now throws ERR_INVALID_ARG_TYPE instead of ERR_INVALID_CALLBACK .
- rejectUnauthorized If not false , the server certificate is verified against the list of supplied CAs. An ‘error’ event is emitted if verification fails; err.code contains the OpenSSL error code. Default: true .
- requestCert
callback If renegotiate() returned true , callback is attached once to the ‘secure’ event. If renegotiate() returned false , callback will be called in the next tick with an error, unless the tlsSocket has been destroyed, in which case callback will not be called at all.
Returns: true if renegotiation was initiated, false otherwise.
The tlsSocket.renegotiate() method initiates a TLS renegotiation process. Upon completion, the callback function will be passed a single argument that is either an Error (if the request failed) or null .
This method can be used to request a peer’s certificate after the secure connection has been established.
When running as the server, the socket will be destroyed with an error after handshakeTimeout timeout.
For TLSv1.3, renegotiation cannot be initiated, it is not supported by the protocol.
tlsSocket.setMaxSendFragment(size) #
- size The maximum TLS fragment size. The maximum value is 16384 . Default: 16384 .
- Returns:
The tlsSocket.setMaxSendFragment() method sets the maximum TLS fragment size. Returns true if setting the limit succeeded; false otherwise.
Smaller fragment sizes decrease the buffering latency on the client: larger fragments are buffered by the TLS layer until the entire fragment is received and its integrity is verified; large fragments can span multiple roundtrips and their processing can be delayed due to packet loss or reordering. However, smaller fragments add extra TLS framing bytes and CPU overhead, which may decrease overall server throughput.
tls.checkServerIdentity(hostname, cert) #
History
| Version | Changes |
|---|---|
| v18.0.0 |
Support for uniformResourceIdentifier subject alternative names has been disabled in response to CVE-2021-44531.
- hostname The host name or IP address to verify the certificate against.
- cert A certificate object representing the peer’s certificate.
- Returns: |
Verifies the certificate cert is issued to hostname .
Returns object, populating it with reason , host , and cert on failure. On success, returns .
This function is intended to be used in combination with the checkServerIdentity option that can be passed to tls.connect() and as such operates on a certificate object. For other purposes, consider using x509.checkHost() instead.
This function can be overwritten by providing an alternative function as the options.checkServerIdentity option that is passed to tls.connect() . The overwriting function can call tls.checkServerIdentity() of course, to augment the checks done with additional verification.
This function is only called if the certificate passed all other checks, such as being issued by trusted CA ( options.ca ).
Earlier versions of Node.js incorrectly accepted certificates for a given hostname if a matching uniformResourceIdentifier subject alternative name was present (see CVE-2021-44531). Applications that wish to accept uniformResourceIdentifier subject alternative names can use a custom options.checkServerIdentity function that implements the desired behavior.
tls.connect(options[, callback]) #
History
| Version | Changes |
|---|---|
| v17.3.1, v16.13.2, v14.18.3, v12.22.9 |
Added onread option.
The highWaterMark option is accepted now.
The pskCallback option is now supported.
Support the allowHalfOpen option.
The hints option is now supported.
The enableTrace option is now supported.
The timeout option is supported now.
The lookup option is supported now.
The ALPNProtocols option can be a TypedArray or DataView now.
ALPN options are supported now.
The secureContext option is supported now.
host Host the client should connect to. Default: ‘localhost’ .
port Port the client should connect to.
path Creates Unix socket connection to path. If this option is specified, host and port are ignored.
socket Establish secure connection on a given socket rather than creating a new socket. Typically, this is an instance of net.Socket , but any Duplex stream is allowed. If this option is specified, path , host , and port are ignored, except for certificate validation. Usually, a socket is already connected when passed to tls.connect() , but it can be connected later. Connection/disconnection/destruction of socket is the user’s responsibility; calling tls.connect() will not cause net.connect() to be called.
allowHalfOpen If set to false , then the socket will automatically end the writable side when the readable side ends. If the socket option is set, this option has no effect. See the allowHalfOpen option of net.Socket for details. Default: false .
rejectUnauthorized If not false , the server certificate is verified against the list of supplied CAs. An ‘error’ event is emitted if verification fails; err.code contains the OpenSSL error code. Default: true .
- hint: optional message sent from the server to help client decide which identity to use during negotiation. Always null if TLS 1.3 is used.
- Returns: in the form < psk: , identity: >or null to stop the negotiation process. psk must be compatible with the selected cipher’s digest. identity must use UTF-8 encoding.
When negotiating TLS-PSK (pre-shared keys), this function is called with optional identity hint provided by the server or null in case of TLS 1.3 where hint was removed. It will be necessary to provide a custom tls.checkServerIdentity() for the connection as the default one will try to check host name/IP of the server against the certificate but that’s not applicable for PSK because there won’t be a certificate present. More information can be found in the RFC 4279.
ALPNProtocols : | | | | | | An array of strings, Buffer s, TypedArray s, or DataView s, or a single Buffer , TypedArray , or DataView containing the supported ALPN protocols. Buffer s should have the format [len][name][len][name]. e.g. ‘x08http/1.1x08http/1.0’ , where the len byte is the length of the next protocol name. Passing an array is usually much simpler, e.g. [‘http/1.1’, ‘http/1.0’] . Protocols earlier in the list have higher preference than those later.
servername : Server name for the SNI (Server Name Indication) TLS extension. It is the name of the host being connected to, and must be a host name, and not an IP address. It can be used by a multi-homed server to choose the correct certificate to present to the client, see the SNICallback option to tls.createServer() .
checkServerIdentity(servername, cert) A callback function to be used (instead of the builtin tls.checkServerIdentity() function) when checking the server’s host name (or the provided servername when explicitly set) against the certificate. This should return an if verification fails. The method should return undefined if the servername and cert are verified.
session A Buffer instance, containing TLS session.
minDHSize Minimum size of the DH parameter in bits to accept a TLS connection. When a server offers a DH parameter with a size less than minDHSize , the TLS connection is destroyed and an error is thrown. Default: 1024 .
highWaterMark : Consistent with the readable stream highWaterMark parameter. Default: 16 * 1024 .
secureContext : TLS context object created with tls.createSecureContext() . If a secureContext is not provided, one will be created by passing the entire options object to tls.createSecureContext() .
onread If the socket option is missing, incoming data is stored in a single buffer and passed to the supplied callback when data arrives on the socket, otherwise the option is ignored. See the onread option of net.Socket for details.
. tls.createSecureContext() options that are used if the secureContext option is missing, otherwise they are ignored.
. Any socket.connect() option not already listed.
The callback function, if specified, will be added as a listener for the ‘secureConnect’ event.
tls.connect() returns a tls.TLSSocket object.
Unlike the https API, tls.connect() does not enable the SNI (Server Name Indication) extension by default, which may cause some servers to return an incorrect certificate or reject the connection altogether. To enable SNI, set the servername option in addition to host .
The following illustrates a client for the echo server example from tls.createServer() :
tls.connect(path[, options][, callback]) #
- path Default value for options.path .
- options See tls.connect() .
- callback See tls.connect() .
- Returns:
Same as tls.connect() except that path can be provided as an argument instead of an option.
A path option, if specified, will take precedence over the path argument.
tls.connect(port[, host][, options][, callback]) #
- port Default value for options.port .
- host Default value for options.host .
- options See tls.connect() .
- callback See tls.connect() .
- Returns:
Same as tls.connect() except that port and host can be provided as arguments instead of options.
A port or host option, if specified, will take precedence over any port or host argument.
tls.createSecureContext([options]) #
History
| Version | Changes |
|---|---|
| v15.1.0, v14.18.0 |
Added privateKeyIdentifier and privateKeyEngine options to get private key from an OpenSSL engine.
Added sigalgs option to override supported signature algorithms.
TLSv1.3 support added.
The ca: option now supports BEGIN TRUSTED CERTIFICATE .
The minVersion and maxVersion can be used to restrict the allowed TLS protocol versions.
The ecdhCurve cannot be set to false anymore due to a change in OpenSSL.
The options parameter can now include clientCertEngine .
The ecdhCurve option can now be multiple ‘:’ separated curve names or ‘auto’ .
If the key option is an array, individual entries do not need a passphrase property anymore. Array entries can also just be string s or Buffer s now.
The ca option can now be a single string containing multiple CA certificates.
Added in: v0.11.13
- options
- ca | | | Optionally override the trusted CA certificates. Default is to trust the well-known CAs curated by Mozilla. Mozilla’s CAs are completely replaced when CAs are explicitly specified using this option. The value can be a string or Buffer , or an Array of strings and/or Buffer s. Any string or Buffer can contain multiple PEM CAs concatenated together. The peer’s certificate must be chainable to a CA trusted by the server for the connection to be authenticated. When using certificates that are not chainable to a well-known CA, the certificate’s CA must be explicitly specified as a trusted or the connection will fail to authenticate. If the peer uses a certificate that doesn’t match or chain to one of the default CAs, use the ca option to provide a CA certificate that the peer’s certificate can match or chain to. For self-signed certificates, the certificate is its own CA, and must be provided. For PEM encoded certificates, supported types are «TRUSTED CERTIFICATE», «X509 CERTIFICATE», and «CERTIFICATE». See also tls.rootCertificates .
- cert | | | Cert chains in PEM format. One cert chain should be provided per private key. Each cert chain should consist of the PEM formatted certificate for a provided private key , followed by the PEM formatted intermediate certificates (if any), in order, and not including the root CA (the root CA must be pre-known to the peer, see ca ). When providing multiple cert chains, they do not have to be in the same order as their private keys in key . If the intermediate certificates are not provided, the peer will not be able to validate the certificate, and the handshake will fail.
- sigalgs Colon-separated list of supported signature algorithms. The list can contain digest algorithms ( SHA256 , MD5 etc.), public key algorithms ( RSA-PSS , ECDSA etc.), combination of both (e.g ‘RSA+SHA384’) or TLS v1.3 scheme names (e.g. rsa_pss_pss_sha512 ). See OpenSSL man pages for more info.
- ciphers Cipher suite specification, replacing the default. For more information, see Modifying the default TLS cipher suite. Permitted ciphers can be obtained via tls.getCiphers() . Cipher names must be uppercased in order for OpenSSL to accept them.
- clientCertEngine Name of an OpenSSL engine which can provide the client certificate.
- crl | | | PEM formatted CRLs (Certificate Revocation Lists).
- dhparam | Diffie-Hellman parameters, required for perfect forward secrecy. Use openssl dhparam to create the parameters. The key length must be greater than or equal to 1024 bits or else an error will be thrown. Although 1024 bits is permissible, use 2048 bits or larger for stronger security. If omitted or invalid, the parameters are silently discarded and DHE ciphers will not be available.
- ecdhCurve A string describing a named curve or a colon separated list of curve NIDs or names, for example P-521:P-384:P-256 , to use for ECDH key agreement. Set to auto to select the curve automatically. Use crypto.getCurves() to obtain a list of available curve names. On recent releases, openssl ecparam -list_curves will also display the name and description of each available elliptic curve. Default:tls.DEFAULT_ECDH_CURVE .
- honorCipherOrder Attempt to use the server’s cipher suite preferences instead of the client’s. When true , causes SSL_OP_CIPHER_SERVER_PREFERENCE to be set in secureOptions , see OpenSSL Options for more information.
- key | | | | Private keys in PEM format. PEM allows the option of private keys being encrypted. Encrypted keys will be decrypted with options.passphrase . Multiple keys using different algorithms can be provided either as an array of unencrypted key strings or buffers, or an array of objects in the form . The object form can only occur in an array. object.passphrase is optional. Encrypted keys will be decrypted with object.passphrase if provided, or options.passphrase if it is not.
- privateKeyEngine Name of an OpenSSL engine to get private key from. Should be used together with privateKeyIdentifier .
- privateKeyIdentifier Identifier of a private key managed by an OpenSSL engine. Should be used together with privateKeyEngine . Should not be set together with key , because both options define a private key in different ways.
- maxVersion Optionally set the maximum TLS version to allow. One of ‘TLSv1.3’ , ‘TLSv1.2’ , ‘TLSv1.1’ , or ‘TLSv1’ . Cannot be specified along with the secureProtocol option; use one or the other. Default:tls.DEFAULT_MAX_VERSION .
- minVersion Optionally set the minimum TLS version to allow. One of ‘TLSv1.3’ , ‘TLSv1.2’ , ‘TLSv1.1’ , or ‘TLSv1’ . Cannot be specified along with the secureProtocol option; use one or the other. Avoid setting to less than TLSv1.2, but it may be required for interoperability. Default:tls.DEFAULT_MIN_VERSION .
- passphrase Shared passphrase used for a single private key and/or a PFX.
- pfx | | | | PFX or PKCS12 encoded private key and certificate chain. pfx is an alternative to providing key and cert individually. PFX is usually encrypted, if it is, passphrase will be used to decrypt it. Multiple PFX can be provided either as an array of unencrypted PFX buffers, or an array of objects in the form . The object form can only occur in an array. object.passphrase is optional. Encrypted PFX will be decrypted with object.passphrase if provided, or options.passphrase if it is not.
- secureOptions Optionally affect the OpenSSL protocol behavior, which is not usually necessary. This should be used carefully if at all! Value is a numeric bitmask of the SSL_OP_* options from OpenSSL Options.
- secureProtocol Legacy mechanism to select the TLS protocol version to use, it does not support independent control of the minimum and maximum version, and does not support limiting the protocol to TLSv1.3. Use minVersion and maxVersion instead. The possible values are listed as SSL_METHODS, use the function names as strings. For example, use ‘TLSv1_1_method’ to force TLS version 1.1, or ‘TLS_method’ to allow any TLS protocol version up to TLSv1.3. It is not recommended to use TLS versions less than 1.2, but it may be required for interoperability. Default: none, see minVersion .
- sessionIdContext Opaque identifier used by servers to ensure session state is not shared between applications. Unused by clients.
- ticketKeys : 48-bytes of cryptographically strong pseudorandom data. See Session Resumption for more information.
- sessionTimeout The number of seconds after which a TLS session created by the server will no longer be resumable. See Session Resumption for more information. Default: 300 .
tls.createServer() sets the default value of the honorCipherOrder option to true , other APIs that create secure contexts leave it unset.
tls.createServer() uses a 128 bit truncated SHA1 hash value generated from process.argv as the default value of the sessionIdContext option, other APIs that create secure contexts have no default value.
The tls.createSecureContext() method creates a SecureContext object. It is usable as an argument to several tls APIs, such as tls.createServer() and server.addContext() , but has no public methods.
A key is required for ciphers that use certificates. Either key or pfx can be used to provide it.
If the ca option is not given, then Node.js will default to using Mozilla’s publicly trusted list of CAs.
tls.createSecurePair([context][, isServer][, requestCert][, rejectUnauthorized][, options]) #
History
| Version | Changes |
|---|---|
| v12.12.0 |
ALPN options are supported now.
Deprecated since: v0.11.3
- context A secure context object as returned by tls.createSecureContext()
- isServer true to specify that this TLS connection should be opened as a server.
- requestCert true to specify whether a server should request a certificate from a connecting client. Only applies when isServer is true .
- rejectUnauthorized If not false a server automatically reject clients with invalid certificates. Only applies when isServer is true .
- options
- enableTrace : See tls.createServer()
- secureContext : A TLS context object from tls.createSecureContext()
- isServer : If true the TLS socket will be instantiated in server-mode. Default: false .
- server A net.Server instance
- requestCert : See tls.createServer()
- rejectUnauthorized : See tls.createServer()
- ALPNProtocols : See tls.createServer()
- SNICallback : See tls.createServer()
- session A Buffer instance containing a TLS session.
- requestOCSP If true , specifies that the OCSP status request extension will be added to the client hello and an ‘OCSPResponse’ event will be emitted on the socket before establishing a secure communication.
Creates a new secure pair object with two streams, one of which reads and writes the encrypted data and the other of which reads and writes the cleartext data. Generally, the encrypted stream is piped to/from an incoming encrypted data stream and the cleartext one is used as a replacement for the initial encrypted stream.
tls.createSecurePair() returns a tls.SecurePair object with cleartext and encrypted stream properties.
Using cleartext has the same API as tls.TLSSocket .
The tls.createSecurePair() method is now deprecated in favor of tls.TLSSocket() . For example, the code:
can be replaced by:
where secureSocket has the same API as pair.cleartext .
tls.createServer([options][, secureConnectionListener]) #
History
| Version | Changes |
|---|---|
| v5.0.0 |
If ALPNProtocols is set, incoming connections that send an ALPN extension with no supported protocols are terminated with a fatal no_application_protocol alert.
The options parameter now supports net.createServer() options.
The options parameter can now include clientCertEngine .
The ALPNProtocols option can be a TypedArray or DataView now.
ALPN options are supported now.
ALPNProtocols : | | | | | | An array of strings, Buffer s, TypedArray s, or DataView s, or a single Buffer , TypedArray , or DataView containing the supported ALPN protocols. Buffer s should have the format [len][name][len][name]. e.g. 0x05hello0x05world , where the first byte is the length of the next protocol name. Passing an array is usually much simpler, e.g. [‘hello’, ‘world’] . (Protocols should be ordered by their priority.)
clientCertEngine Name of an OpenSSL engine which can provide the client certificate.
enableTrace If true , tls.TLSSocket.enableTrace() will be called on new connections. Tracing can be enabled after the secure connection is established, but this option must be used to trace the secure connection setup. Default: false .
handshakeTimeout Abort the connection if the SSL/TLS handshake does not finish in the specified number of milliseconds. A ‘tlsClientError’ is emitted on the tls.Server object whenever a handshake times out. Default: 120000 (120 seconds).
rejectUnauthorized If not false the server will reject any connection which is not authorized with the list of supplied CAs. This option only has an effect if requestCert is true . Default: true .
requestCert If true the server will request a certificate from clients that connect and attempt to verify that certificate. Default: false .
sessionTimeout The number of seconds after which a TLS session created by the server will no longer be resumable. See Session Resumption for more information. Default: 300 .
SNICallback(servername, callback) A function that will be called if the client supports SNI TLS extension. Two arguments will be passed when called: servername and callback . callback is an error-first callback that takes two optional arguments: error and ctx . ctx , if provided, is a SecureContext instance. tls.createSecureContext() can be used to get a proper SecureContext . If callback is called with a falsy ctx argument, the default secure context of the server will be used. If SNICallback wasn’t provided the default callback with high-level API will be used (see below).
ticketKeys : 48-bytes of cryptographically strong pseudorandom data. See Session Resumption for more information.
- socket: the server tls.TLSSocket instance for this connection.
- identity: identity parameter sent from the client.
- Returns: | | pre-shared key that must either be a buffer or null to stop the negotiation process. Returned PSK must be compatible with the selected cipher’s digest.
When negotiating TLS-PSK (pre-shared keys), this function is called with the identity provided by the client. If the return value is null the negotiation process will stop and an «unknown_psk_identity» alert message will be sent to the other party. If the server wishes to hide the fact that the PSK identity was not known, the callback must provide some random data as psk to make the connection fail with «decrypt_error» before negotiation is finished. PSK ciphers are disabled by default, and using TLS-PSK thus requires explicitly specifying a cipher suite with the ciphers option. More information can be found in the RFC 4279.
pskIdentityHint optional hint to send to a client to help with selecting the identity during TLS-PSK negotiation. Will be ignored in TLS 1.3. Upon failing to set pskIdentityHint ‘tlsClientError’ will be emitted with ‘ERR_TLS_PSK_SET_IDENTIY_HINT_FAILED’ code.
. Any tls.createSecureContext() option can be provided. For servers, the identity options ( pfx , key / cert , or pskCallback ) are usually required.
. Any net.createServer() option can be provided.
Creates a new tls.Server . The secureConnectionListener , if provided, is automatically set as a listener for the ‘secureConnection’ event.
The ticketKeys options is automatically shared between node:cluster module workers.
The following illustrates a simple echo server:
The server can be tested by connecting to it using the example client from tls.connect() .
tls.getCiphers() #
Returns an array with the names of the supported TLS ciphers. The names are lower-case for historical reasons, but must be uppercased to be used in the ciphers option of tls.createSecureContext() .
Not all supported ciphers are enabled by default. See Modifying the default TLS cipher suite.
Cipher names that start with ‘tls_’ are for TLSv1.3, all the others are for TLSv1.2 and below.
Источник
Adblock
detector
| Version | Changes |
|---|---|
| v19.0.0 |